How is Al used to identify issues within network traffic?
Which two principles must be considered when using per-hop behavior in QoS? (Choose two.)
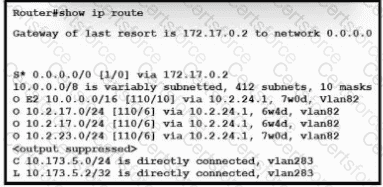
Refer to the exhibit. What is the value of the administrative distance for the default gateway?
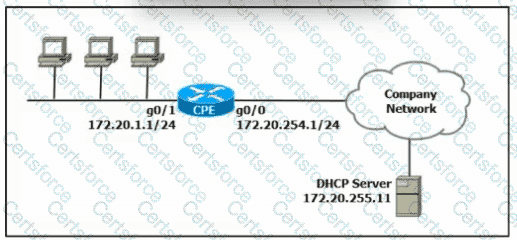
Refer to the exhibit. A network engineer must configure the CPE router to allow computers in the 172.20.1.0/24 network to obtain their IP configurations from the central DHCP server. Which configuration must the engineer apply to the CPE?
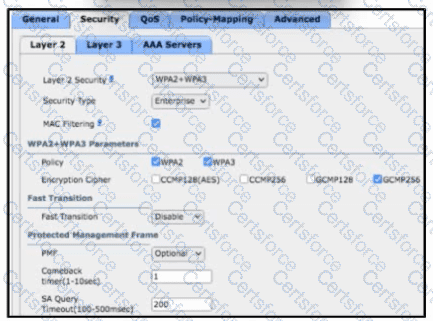
Refer to the exhibit. The Wi-Fi SSID " Office_WLAN " has Layer 2 Security configured with MAC filtering enabled. What additional security is provided by this specific feature?
Which statement describes virtual machines?
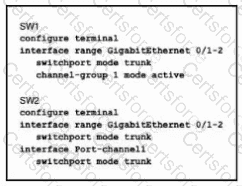
Refer to the exhibit. An LACP EtherChannel between two directly connected switches is in the configuration process.
Which command must be configured on switch SW2’s Gi0/1-2 interfaces to establish the channel to SW1?
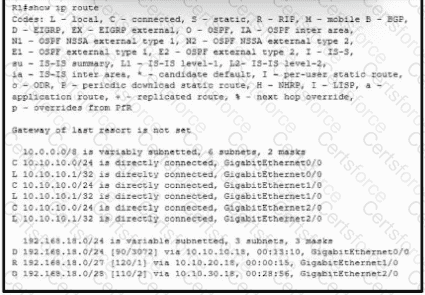
Refer to the exhibit. Which interface does a packet take to reach the host address of 192.168.18.16?
What is the function of generative AI in network operations?
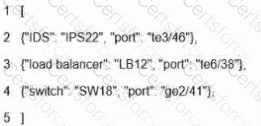
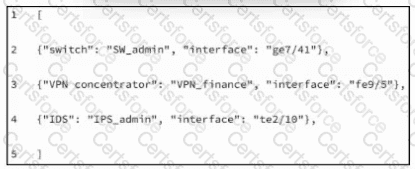
What is represented by the word " switch " within this JSON schema?
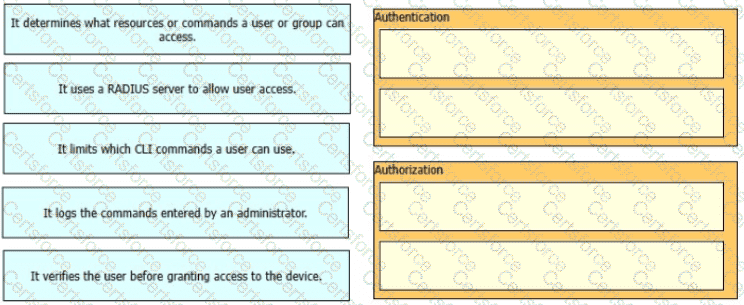
Drag and drop the AAA features from the left onto the corresponding AAA security services on the right Not all options are used.
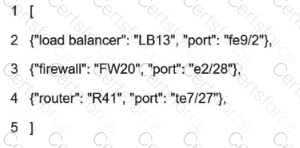
What is represented by the word " LB13 " within this JSON schema?
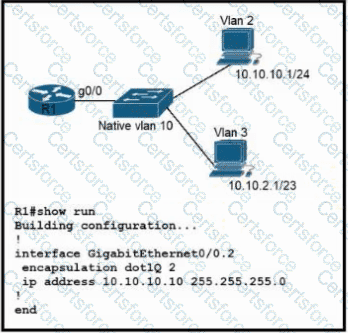
Refer to the exhibit. Configurations for the switch and PCs are complete.
Which configuration must be applied so that VLANs 2 and 3 communicate back and forth?
Refer to the exhibit. What is represented in line 2 within this JSON schema?
What is a characteristic of an SSID in wireless networks?
Which type of wired port is required when an AP offers one unique SSID, passes client data and management traffic, and is in autonomous mode?
Refer to the exhibit.
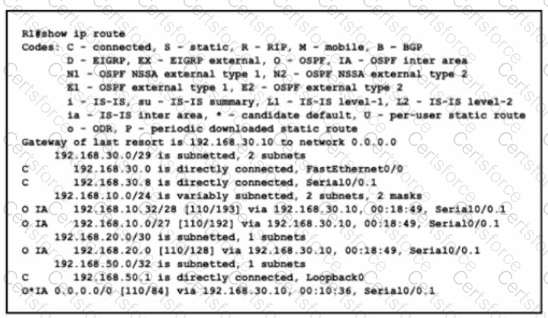
What is the metric for the route to the 192.168.10.33 host?
Refer to the exhibit.
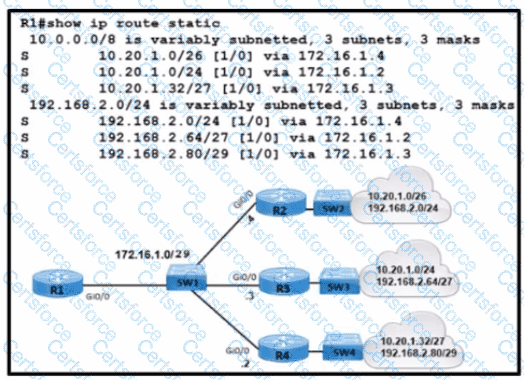
What is the correct next hop for router R1 to reach IP addresses 192.168.2.86 and 10.20.1.50?
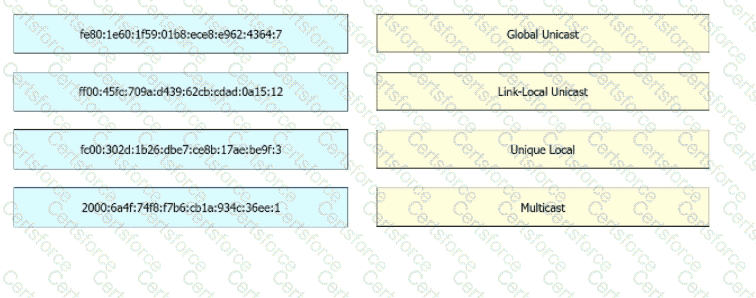
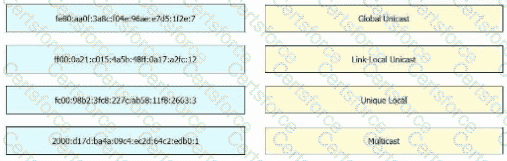
Drag and drop the IPv6 address from the left onto the type on the right.
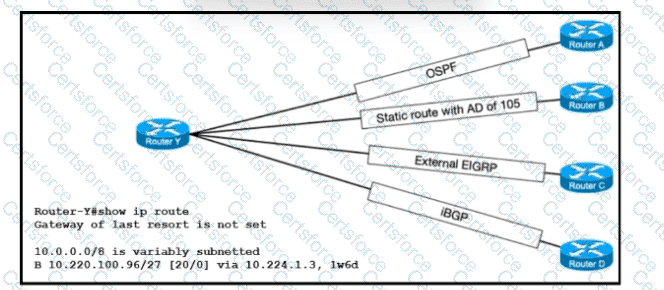
Refer to the exhibit. The route for 10.220.100.96/27 has been very unstable. The same route has four backups to routers A, B, C, and D via the respective methods. The routing protocol defaults for router Y have not been changed. When the current route for 10.220.100.96/27 becomes unavailable, which router will router Y use to route traffic to 10.220.100.96/27?
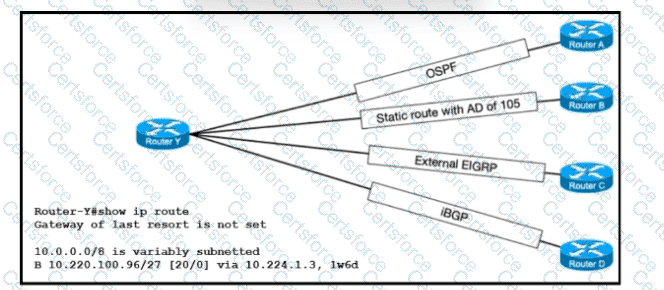
Refer to the exhibit. The route for 10.220.100.96/27 has been very unstable. The same route has four backups to routers A, B, C, and D via the respective methods. The routing protocol defaults for router Y have not been changed. When the current route for 10.220.100.96/27 becomes unavailable, which router will router Y use to route traffic to 10.220.100.96/27?
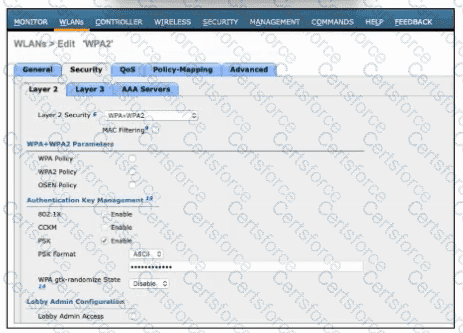
Refer to the exhibit. A network engineer is configuring a WLAN to use a WPA2 PSK and allow only specific clients to join. Which two actions must be taken to complete the process? (Choose two)
Which interface is used to send traffic to the destination network?
O 10.76.170 161/26 |110/102] via FO/17
O 10.76.170 161/26[110/27e31] via FO/2 0
R 10.76.170.161/261120/15] via FO/8
R 10.76.170.161/26 [120/10] via FO/12
Drag and drop the IPv6 address from the left onto the type on the right.
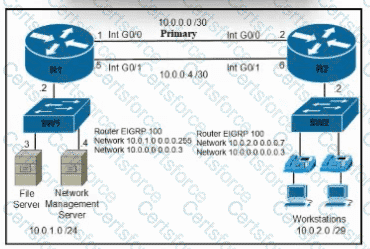
Refer to the exhibit. A secondary route is required on router R1 to pass traffic to the LAN network on R2 if the primary link fails. Which command must be entered to configure the router?
How are API keys used to enforce rate limiting?
An engineer must update the configuration on two PCs in two different subnets to communicate locally with each other. One PC is configured with IP address 192.168.25.128/25 and the other with 192.168.25.100/25. Which network mask must the engineer configure on both PCs to enable the communication?
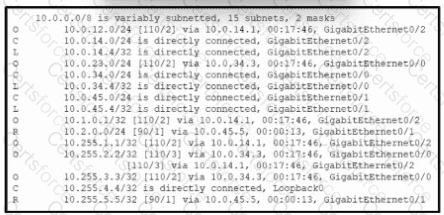
Refer to the exhibit. Which routes are configured with their default administrative distances?
Which syslog message logging level displays interface line protocol up/down events?
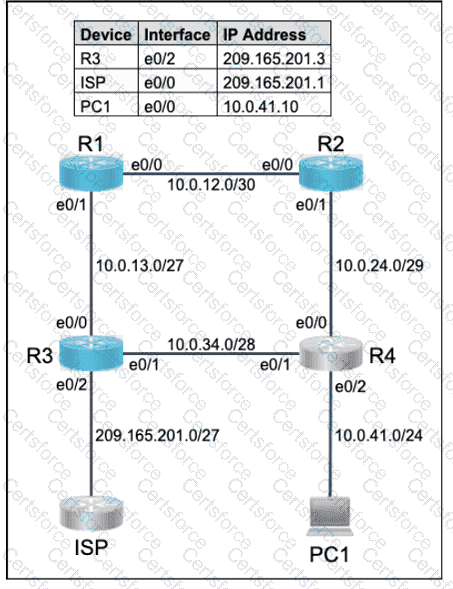
All physical cabling is in place. Router R4 and PCI are fully configured and
inaccessible. R4 ' s WAN interfaces use .4 in the last octet for each subnet.
Configurations should ensure that connectivity is established end-to-end.
1 . Configure static routing to ensure RI prefers the path through R2 to
reach only PCI on R4 ' s LAN
2. Configure static routing that ensures traffic sourced from RI will take
an alternate path through R3 to PCI in the event of an outage along
the primary path
3. Configure default routes on RI and R3 to the Internet using the least number of hops
Guidelines
This is a lab item in which tasks will be performed on virtual devices.
• Refer to the Tasks tab to view the tasks for this lab item.
• Refer to the Topology tab to access the device console(s) and perform the tasks.
• Console access is available for all required devices by clicking the device icon or using
the tab(s) above the console window.
• All necessary preconfigurations have been applied.
• Do not change the enable password or hostname for any device.
• Save your configurations to NVRAM before moving to the next item.
• Click Next at the bottom of the screen to submit this lab and move to the next question.
• When Next is clicked, the lab closes and cannot be reopened.
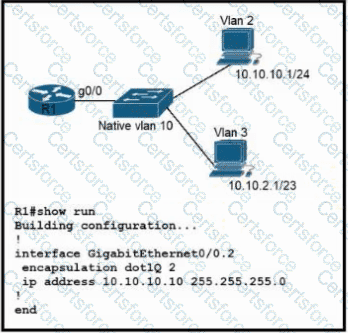
Refer to the exhibit. Configurations for the switch and PCs are complete.
Which configuration must be applied so that VLANs 2 and 3 communicate back and forth?
Aswitch receives a frame with the destination MAC address 3C:5D: 7E:9F: 1A:2B.
Switch# show ethernet-frame-and-mac-address-table
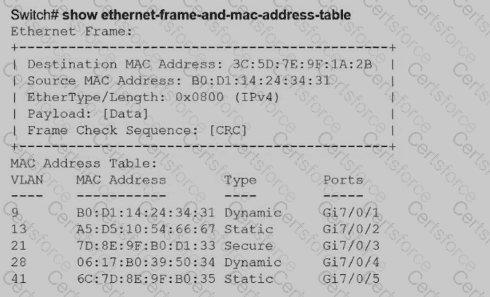
How does the switch handle the frame?
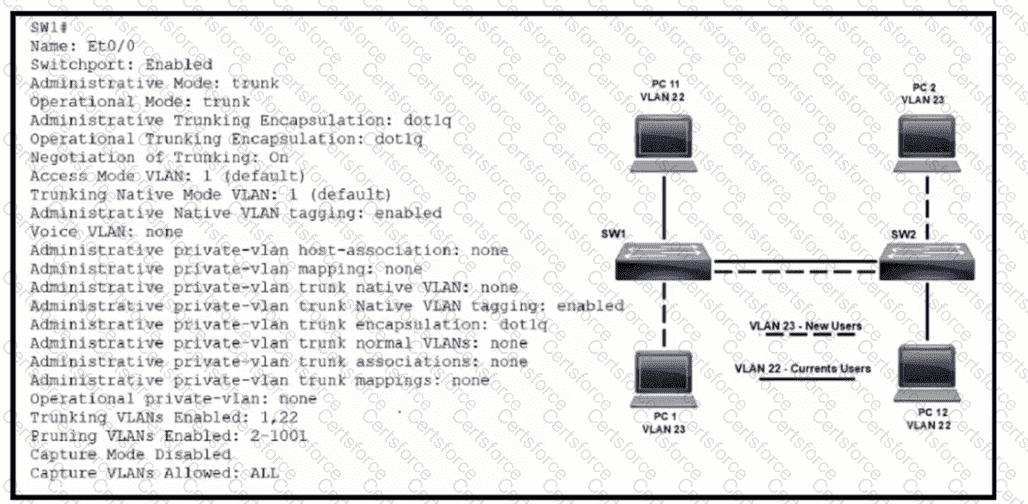
Refer to the exhibit. VLAN 23 is being implemented between SW1 and SW2. The command show interface ethernet0/0 switchport has been issued on SW1. Ethernet0/0 on SW1 is the uplink to SW2. Which command when entered on the uplink interface allows PC 1 and PC 2 to communicate without impact to the communication between PC 11 and PC 12?
When an access point is seeking to join wireless LAN controller, which message is sent to the AP- Manager interface?
A packet from a company s branch office is destined to host 172.31.0.1 at headquarters. The sending router has three possible matches in its routing table for the packet prefixes: 172. 31.0 .0/16.72.31.0.0724. and 172.31 0 0/25. How does the router handle the packet?
What are two differences between WPA2 and WPA3 wireless security? (Choose two.)
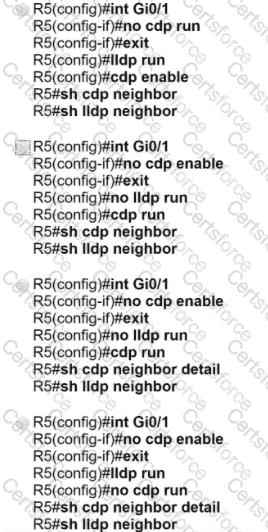
Refer to the exhibit.
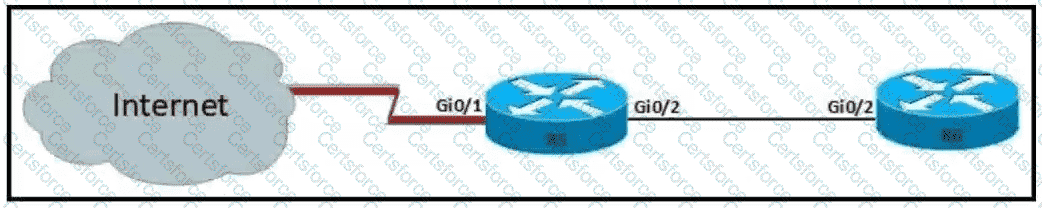
For security reasons, automatic neighbor discovery must be disabled on the R5 Gi0/1 interface. These tasks must be completed:
• Disable all neighbor discovery methods on R5 interface GiO/1.
• Permit neighbor discovery on R5 interface GiO/2.
• Verify there are no dynamically learned neighbors on R5 interface Gi0/1.
• Display the IP address of R6*s interface Gi0/2.
Which configuration must be used?
How does IPsec provide secure networking for applications within an organization?
How do TCP and UDP fit into a query-response model?
What are two examples of multifactor authentication? (Choose two.)
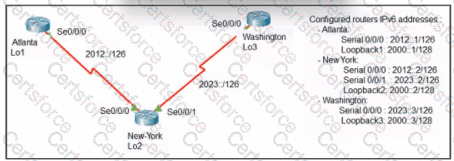
Refer to the exhibit. An engineer configured the New York router with static routes that point to the Atlanta and Washington sites. Which command must be configured on the Atlanta and Washington routers so that both sites are able to reach the Lo2 interface on the New York router?
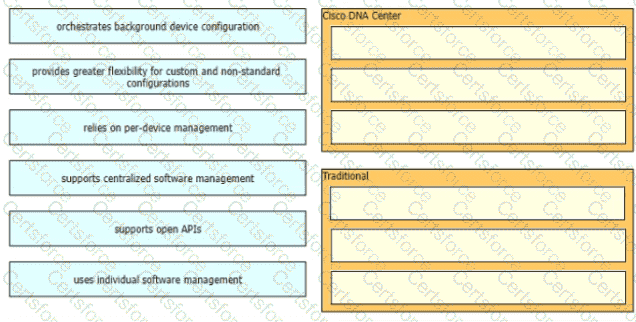
Drag and drop the characteristics of device-management technologies from the left onto the corresponding deployment types on the right.
Refer to the exhibit.
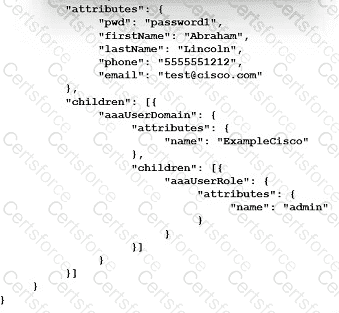
How many objects are present in the given JSON-encoded data?
In a cloud-computing environment what is rapid elasticity?
Which two features introduced in SNMPv2 provides the ability to retrieve large amounts of data in one request
When a WPA2-PSK WLAN is configured in the Wireless LAN Controller, what is the minimum number of characters that is required in ASCII format?
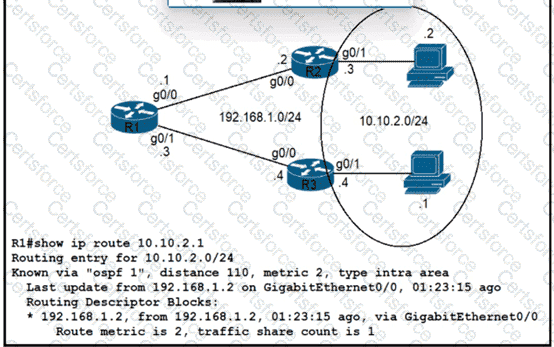
Refer to the exhibit.
Traffic from R1 to the 10.10.2.0/24 subnet uses 192.168.1.2 as its next hop. An network engineer wants to update the R1 configuration so that traffic with destination 10.10.2.1 passes through router R3, and all other traffic to the 10.10.20/24 subnet passes through r2. Which command must be used?
Which protocol should be used to transfer large files on a company intranet that allows TCP ports 20 and 21 through the firewall?
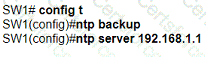
An engineer is configuring switch SW1 to act an NTP server when all upstream NTP server connectivity fails. Which configuration must be used?
A)
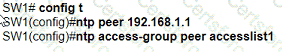
B)
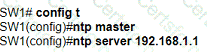
C)
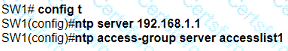
D)
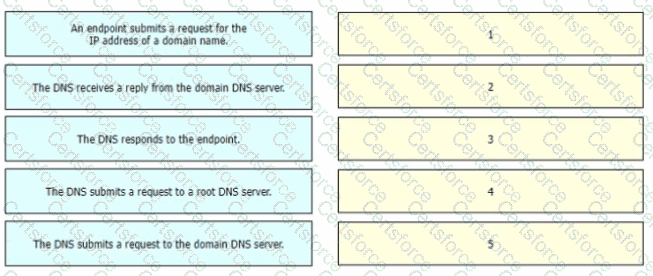
Drag and drop the steps in a standard DNS lookup operation from the left into the order on the right.