How does authentication differ from authorization?
Which part of the HTTP request is used in REST API basic authentication to carry credentials?
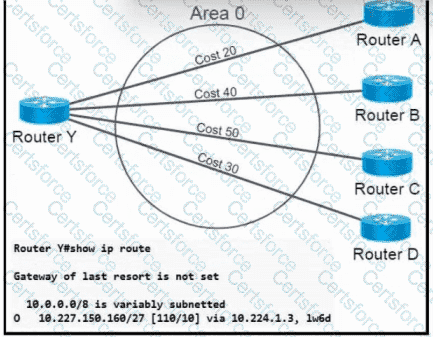
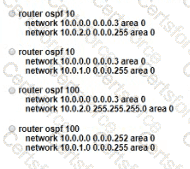
Refer to the exhibit. OSPF neighbors routers A, B, C, and D are sending a route for 10.227.150.160/27. When the current route for 10.227.150.160/27 becomes unavailable, which cost will router Y use to route traffic to 10.227.150.160/27?
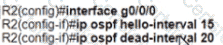
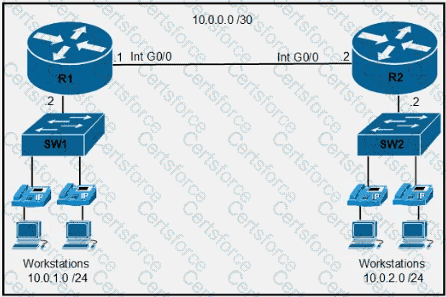
Refer to the exhibit.
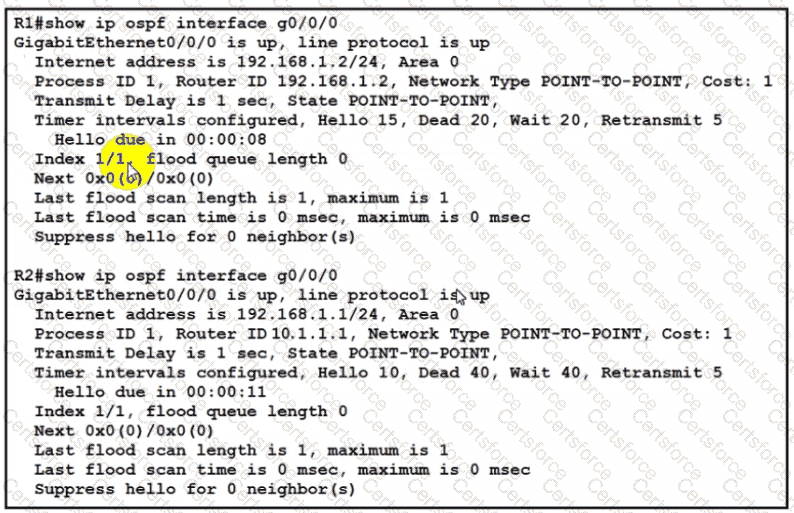
The network engineer is configuring router R2 as a replacement router on the network After the initial configuration is applied it is determined that R2 failed to show R1 as a neighbor Which configuration must be applied to R2 to complete the OSPF configuration and enable it to establish the neighbor relationship with R1?
A)
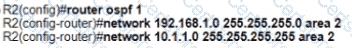
B)

C)

D)
Refer to the exhibit.
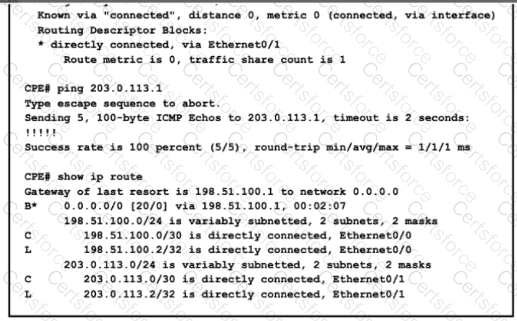
After configuring a new static route on the CPE. the engineer entered this series of commands to verify that the new configuration is operating normally When is the static default route installed into the routing table?
What is a link-local all-nodes IPv6 multicast address?
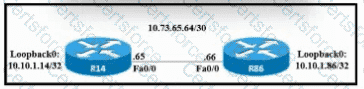
Refer to the exhibit. A static route must be configured on R14 to forward traffic for the 172.21.34.0/25 network that resides on R86. Which command must be used to fulfill the request?
What is a characteristic of private IPv4 addressing?
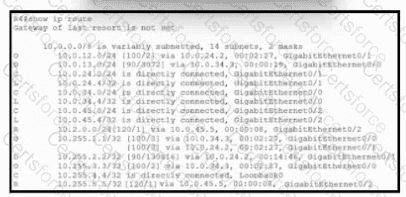
Refer to the exhibit. Of the routes learned with dynamic routing protocols, which has the least preferred metric?
Which technology is appropriate for communication between an SDN controller and applications running over the network?
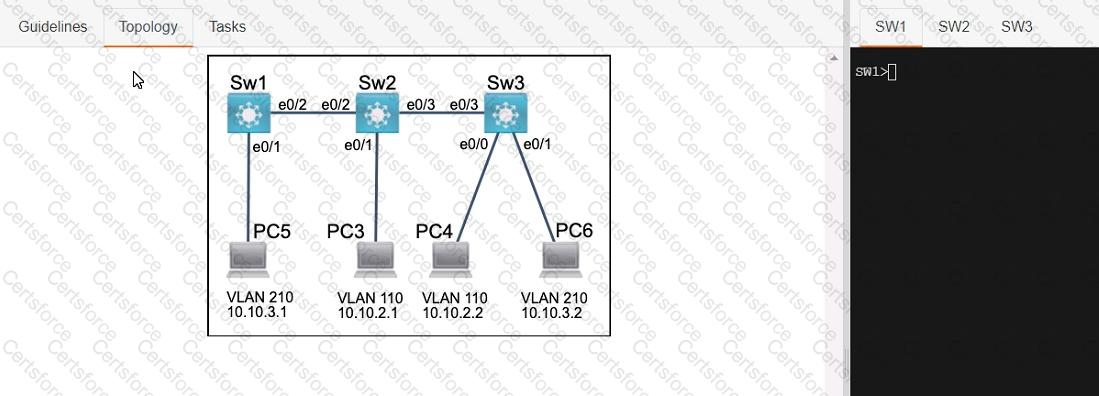
Three switches must be configured for Layer 2 connectivity. The company requires only the designated VLANs to be configured on their respective switches and permitted accross any links between switches for security purposes. Do not modify or delete VTP configurations.
The network needs two user-defined VLANs configured:
VLAN 110: MARKETING
VLAN 210: FINANCE
1. Configure the VLANs on the designated switches and assign them as access ports to the interfaces connected to the PCs.
2. Configure the e0/2 interfaces on Sw1 and Sw2 as 802.1q trunks with only the required VLANs permitted.
3. Configure the e0/3 interfaces on Sw2 and Sw3 as 802.1q trunks with only the required VLANs permitted.
What is a characteristic of a Layer 2 switch?
Which combination of methods satisfies the minimum security requirements when a new multifactor authentication solution is deployed?
What are two behaviors of a point-to-point WAN topology? (Choose two.)
Which action implements physical access control as part of the security program of an organization?
Which IP address is used when an administrator must open a web-based management session with a lightweight AP?
What is a characteristic of private IPv4 addressing?
What is the purpose of the ip address dhcp command?
An engineer must configure R1 for a new user account. The account must meet these requirements:
* It must be configured in the local database.
* The username is engineer.
* It must use the strongest password configurable. Which command must the engineer configure on the router?
Refer to the exhibit.
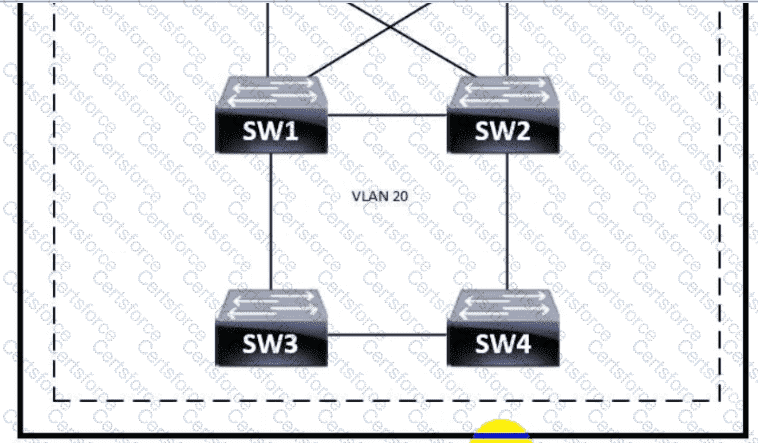
Which switch becomes the root of a spanning tree for VLAN 20 if all li links are of equal speed?
What is an expected outcome when network management automation is deployed?
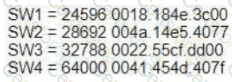
Refer to the exhibit.
Which two commands when used together create port channel 10? (Choose two.)
Refer to the exhibit.
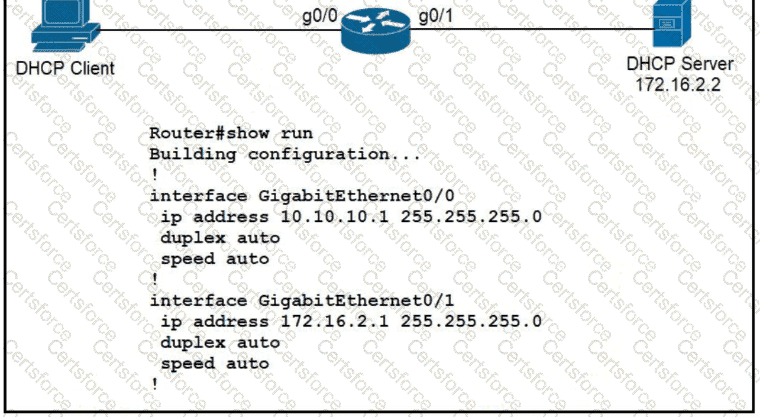
An engineer is configuring a new router on the network and applied this configuration. Which additional configuration allows the PC to obtain its IP address from a DHCP server?
Refer to the exhibit.
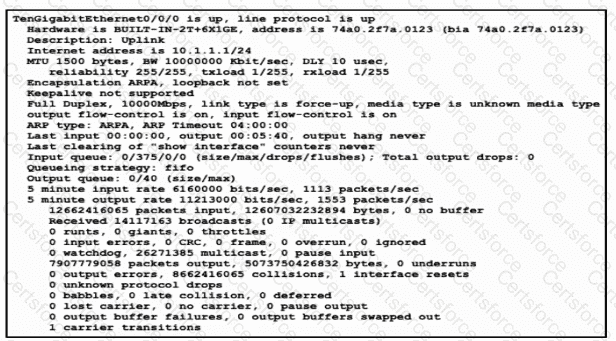
Traffic that is flowing over interface TenGigabitEthernet0/0 experiences slow transfer speeds. What is the reason for the issue?
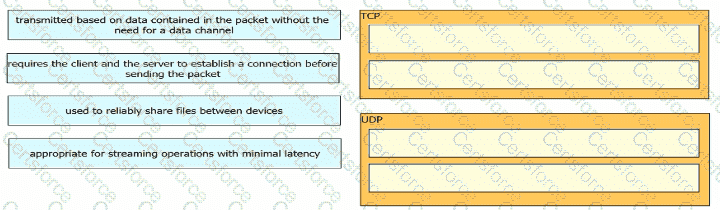
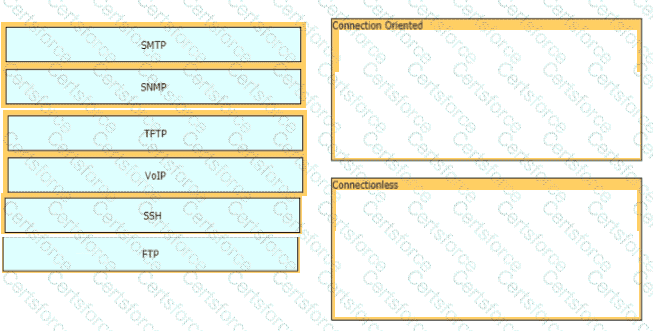
Drag and drop the TCP or UDP details from the left onto their corresponding protocols on the right.
Refer to the exhibit.
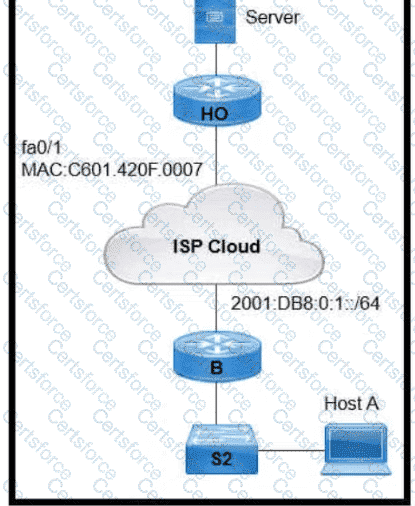
An engineer is configuring the HO router. Which IPv6 address configuration must be applied to the router fa0 ' 1 interface for the router to assign a unique 64-brt IPv6 address to Itself?
Refer to the exhibit.
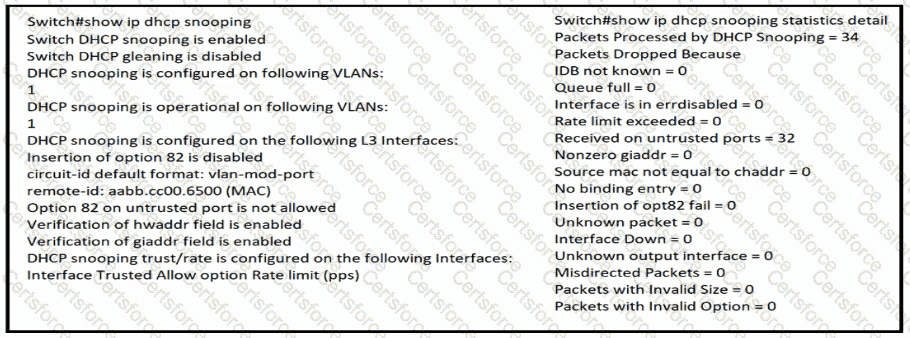
The DHCP server and clients are connected to the same switch. What is the next step to complete the DHCP configuration to allow clients on VLAN 1 to receive addresses from the DHCP server?
A network engineer must implement an IPv6 configuration on the vlan 2000 interface to create a routable locally-unique unicast address that is blocked from being advertised to the internet. Which configuration must the engineer apply?
What is a function of Opportunistic Wireless Encryption in an environment?
Refer to the exhibit.
Which types of JSON data is shown
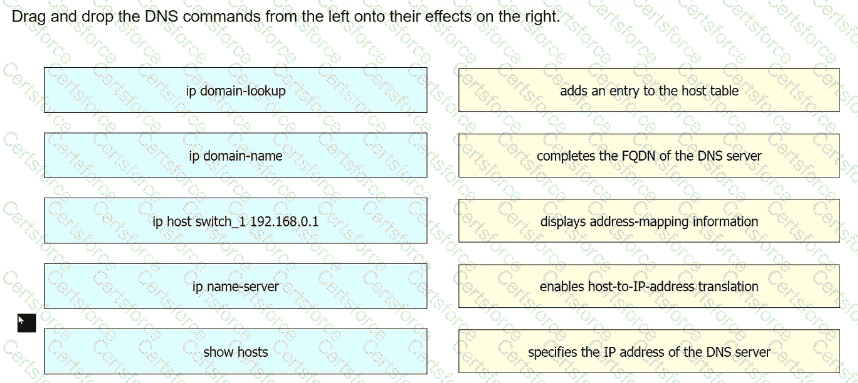
Drag and drop the DNS commands from the left onto their effects on the right.
Refer to the exhibit.

The router has been configured with a subnet to accommodate the requirement for 380 users on a subnet. The requirement already considers 30% future growth. Which configuration verifies the IP subnet on router R4?
What is the RFC 4627 default encoding for JSON text?
Which two practices are recommended for an acceptable security posture in a network? (Choose two)
Which advantage does the network assurance capability of Cisco DNA Center provide over traditional campus management?
Refer to the exhibit. An engineer is asked to confère router R1 so that it forms an OSPF single-area neighbor relationship with R2. Which command sequence must be implemented to configure the router?
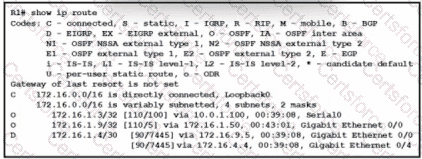
Refer to the exhibit. How does router R1 handle traffic to the 172.16.1.4/30 subnet?
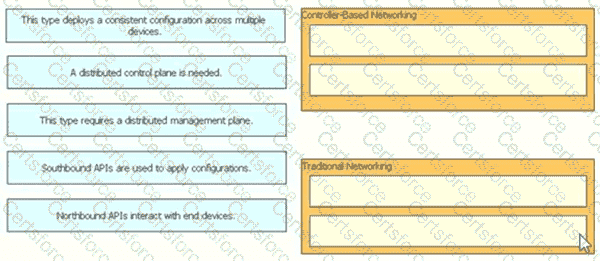
What is the difference between controller-based networks and traditional networks as they relate to control-plane and/or data-plane functions?
Drag and drop the statement about networking from the left into the Corresponding networking types on the right. Not all statements are used.
What is the difference regarding reliability and communication type between TCP and UDP?
Refer to the exhibit.
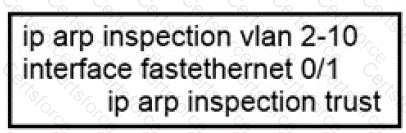
If the network environment is operating normally, which type of device must be connected to interface FastEthernet 0/1?
Refer to the exhibit.
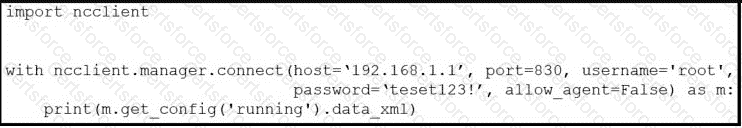
After running the code in the exhibit, which step reduces the amount of data that the NETCONF server returns to the NETCONF client, to only the interface ' s configuration?
Drag and drop the network protocols from the left onto the correct transport services on the right.
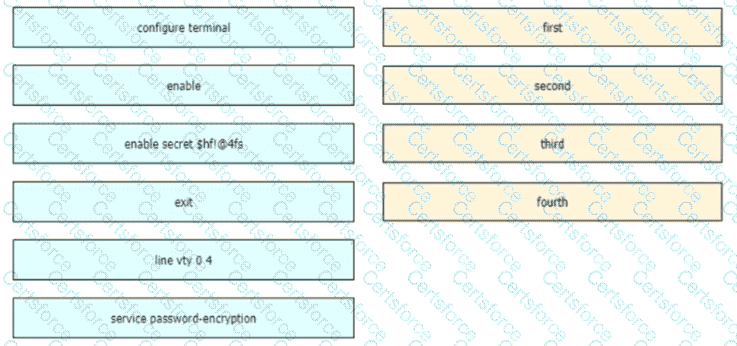
An engineer is configuring an encrypted password for the enable command on a router where the local user database has already been configured Drag and drop the configuration commands from the left into the correct sequence on the right Not all commands are used
What is an appropriate use for private IPv4 addressing?
What are two roles of Domain Name Services (DNS)? (Choose Two)
Which two outcomes are predictable behaviors for HSRP? (Choose two.)
What is the purpose of traffic shaping?
What is a DHCP client?
Refer to the exhibit.
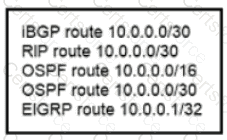
A router reserved these five routes from different routing information sources.
Which two routes does the router install in its routing table? (Choose two)