Which type of organization should use a collapsed-core architecture?
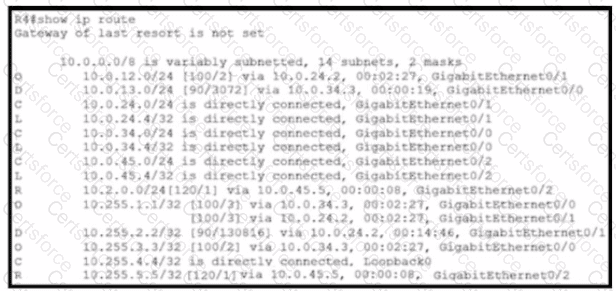
Refer to the exhibit.
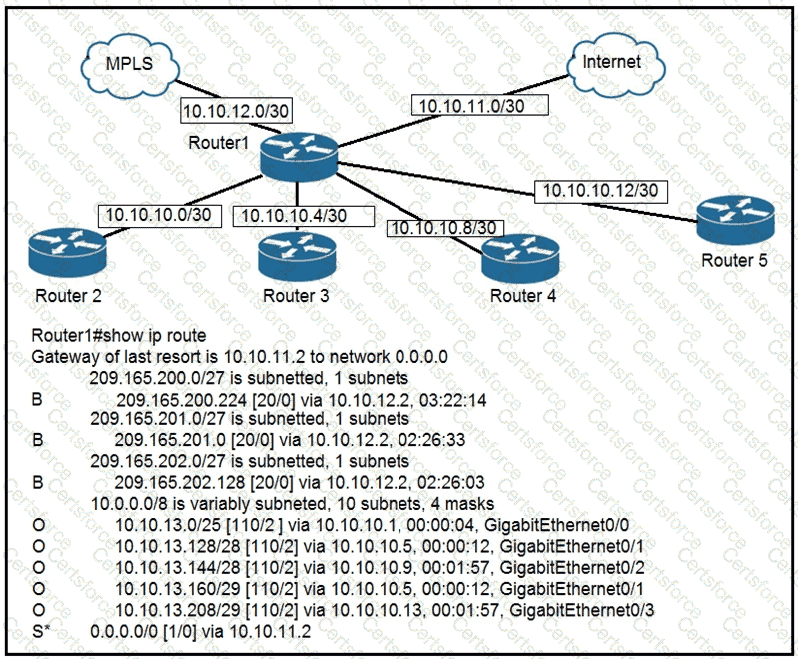
To which device does Router1 send packets that are destined to host 10.10.13.165?
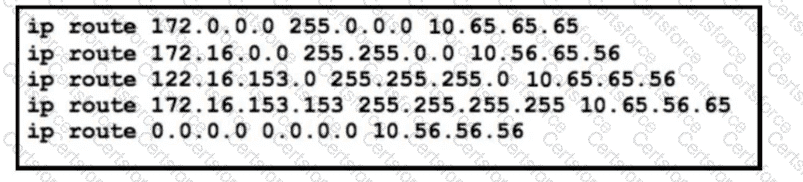
Refer to the exhibit. The static routes were implemented on the border router. What is the next hop IP address for a ping sent to 172.16.153.154 from the border router?
Which type of protocol is VRRP?
If a notice-level messaging is sent to a syslog server, which event has occurred?
A network engineer must configure the router R1 GigabitEthernet1/1 interface to connect to the router R2 GigabitEthernet1/1 interface. For the configuration to be applied the engineer must compress the address 2001:0db8:0000:0000:0500:000a:400F:583B. Which command must be issued on the interface?
An organization developed new security policies and decided to print the policies and distribute them to all personnel so that employees review and apply the policies. Which element of a security program is the organization implementing?
Refer to the exhibit.
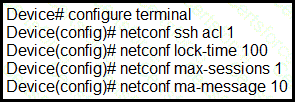
A network engineer must configure NETCONF. After creating the configuration, the engineer gets output from the command show line but not from show running- config. Which command completes the configuration?
Which configuration ensures that the switch is always the root for VLAN 750?
Refer to the exhibit.
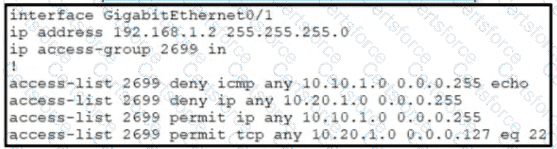
A network administrator must permit SSH access to remotely manage routers in a network. The operations team resides on the 10.20.1.0/25 network. Which command will accomplish this task?
Which technology can prevent client devices from arbitrarily connecting to the network without state remediation?
The SW1 interface g0/1 is in the down/down state. Which two configurations are valid reasons for the interface conditions?(choose two)
Which technology must be implemented to configure network device monitoring with the highest security?
Which protocol uses the SSL?
Refer to the exhibit.
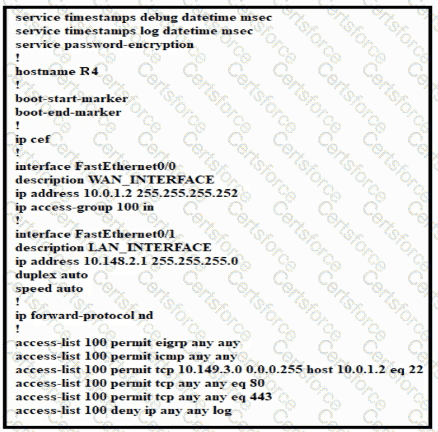
Which configuration enables DHCP addressing for hosts connected to interface FastEthernetO/1 on router R4?
Which action is taken by the data plane within a network device?
Refer to the exhibit.
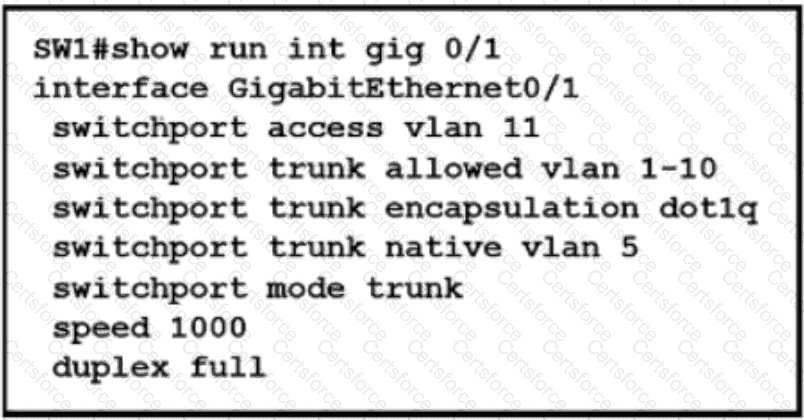
Which action is expected from SW1 when the untagged frame is received on the GigabitEthernet0/1 interface?
Refer to the exhibit.
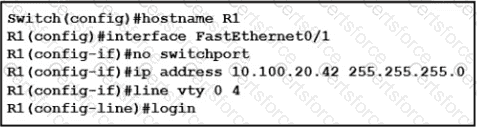
An engineer booted a new switch and applied this configuration via the console port. Which additional configuration must be applied to allow administrators to authenticate directly to enable privilege mode via Telnet using a local username and password?
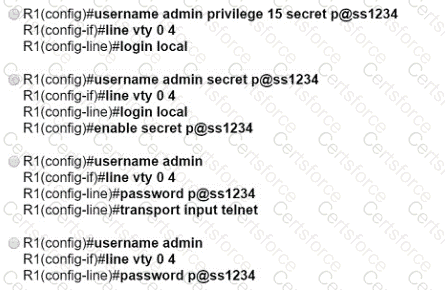
Refer to the exhibit.
Of the routes learned with dynamic routing protocols, which has the least preferred metric?
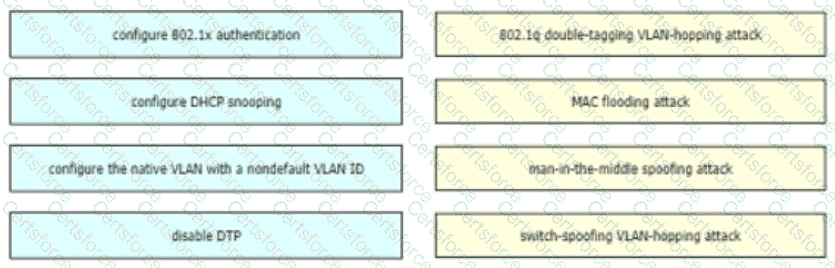
Drag and drop the attack-mitigation techniques from the left onto the Types of attack that they mitigate on the right.
Refer to the exhibit.
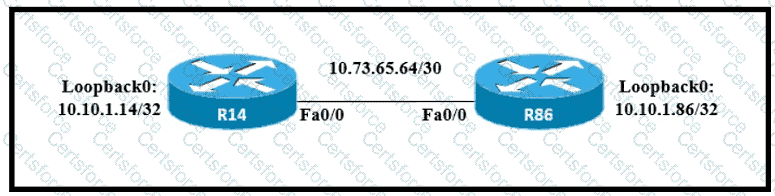
All interfaces are configured with duplex auto and ip ospf network broadcast. Which configuration allows routers R14 and R86 to form an OSPFv2 adjacency and act as a central point for exchanging OSPF information between routers?




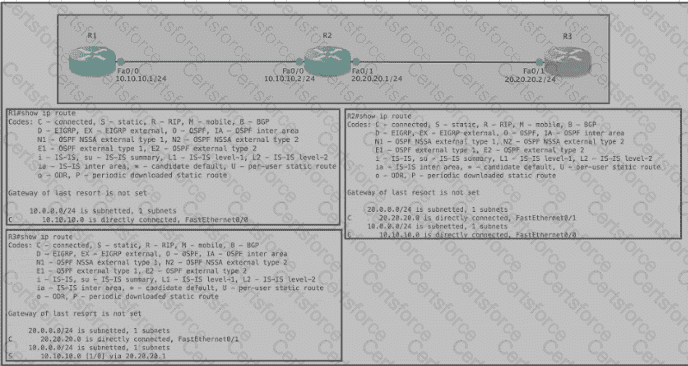
Refer to the exhibit Router R1 Fa0/0 is unable to ping router R3 Fa0 ' 1. Which action must be taken in router R1 to help resolve the configuration issue?