Refer to the exhibit.
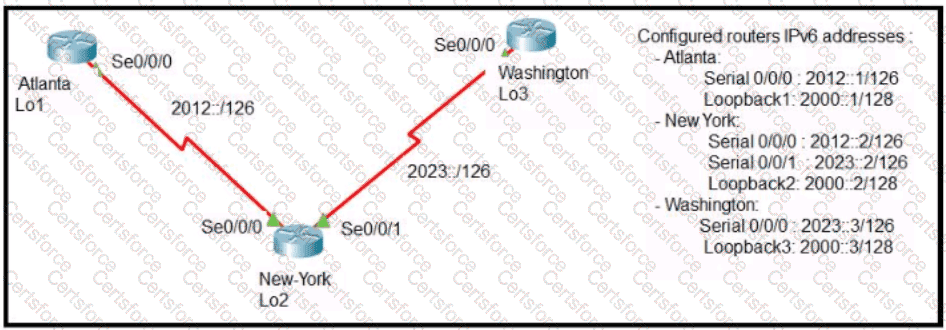
The New York router is configured with static routes pointing to the Atlanta and Washington sites. Which two tasks must be performed so that the Serial0/0/0 interfaces on the Atlanta and Washington routers can reach one another?
(Choose two.)
Which two spanning-tree states are bypassed on an interface running PortFast? (Choose two.)
A network administrator is setting up a new IPv6 network using the 64-bit address 2001 0EB8 00C1 2200:0001 0000 0000 0331/64 To simplify the configuration the administrator has decided to compress the address Which IP address must the administrator configure?
How does Rapid PVST+ create a fast loop-free network topology?
Refer to the exhibit.
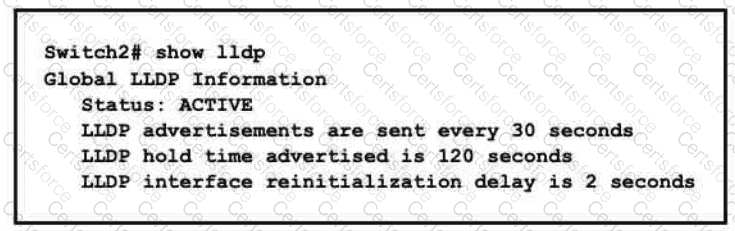
A network engineer must update the configuration on Switch2 so that it sends LLDP packets every minute and the information sent via LLDP is refreshed every 3 minutes Which configuration must the engineer apply?
A)
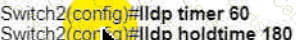
B)
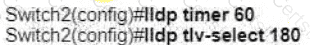
C)
D)
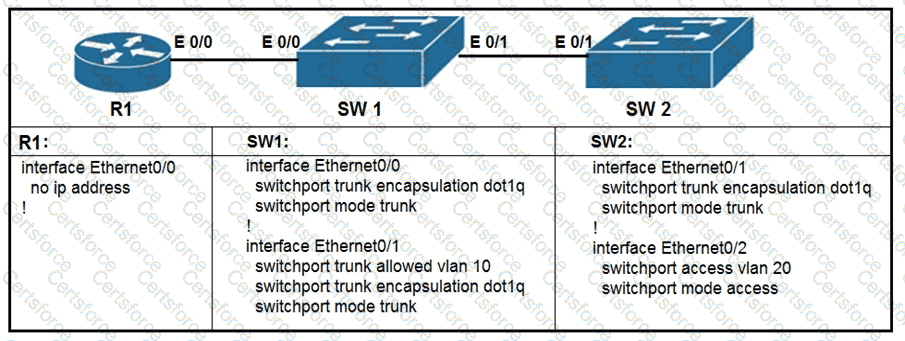
Refer to the exhibit.
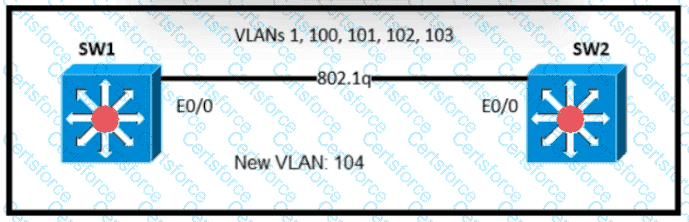
An engineer is asked to insert the new VLAN into the existing trunk without modifying anything previously configured Which command accomplishes this task?
What are two benefits of FHRPs? (Choose two.)
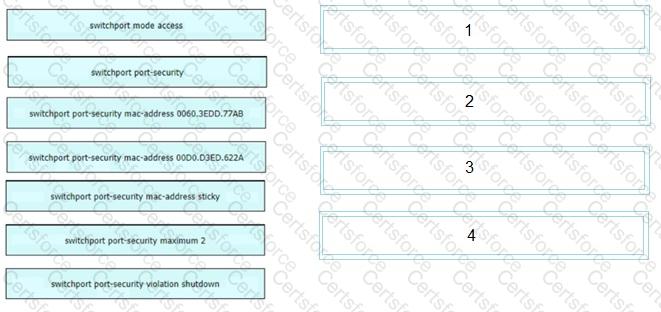
An engineer is tasked to configure a switch with port security to ensure devices that forward unicasts multicasts and broadcasts are unable to flood the port The port must be configured to permit only two random MAC addresses at a time Drag and drop the required configuration commands from the left onto the sequence on the right Not all commands are used.
What provides centralized control of authentication and roaming In an enterprise network?
Refer to the exhibit.
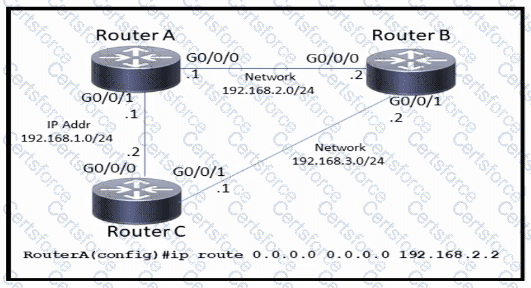
Which command must be issued to enable a floating static default route on router A?
What is a characteristic of private IPv4 addressing?
Refer to the exhibit.
Which network prefix was learned via EIGRP?
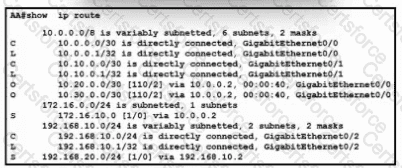
Refer to the exhibit. What is the administrative distance for the advertised prefix that includes the host IP address 192.168.20.1?
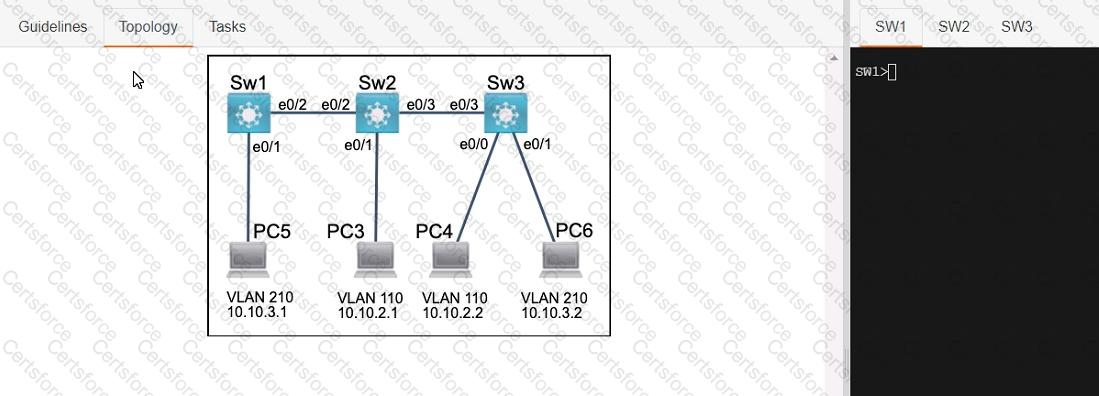
Three switches must be configured for Layer 2 connectivity. The company requires only the designated VLANs to be configured on their respective switches and permitted accross any links between switches for security purposes. Do not modify or delete VTP configurations.
The network needs two user-defined VLANs configured:
VLAN 110: MARKETING
VLAN 210: FINANCE
1. Configure the VLANs on the designated switches and assign them as access ports to the interfaces connected to the PCs.
2. Configure the e0/2 interfaces on Sw1 and Sw2 as 802.1q trunks with only the required VLANs permitted.
3. Configure the e0/3 interfaces on Sw2 and Sw3 as 802.1q trunks with only the required VLANs permitted.
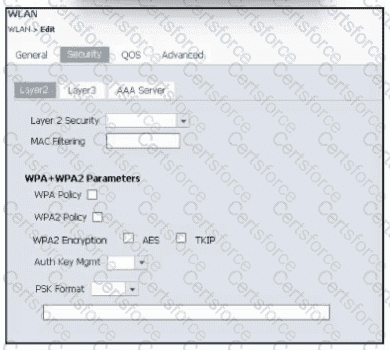
Refer to the exhibit. An engineer is using the Cisco WLC GUI to configure a WLAN for WPA2 encryption with AES and preshared key Cisc0123456. After the engineer selects the WPA + WPA2 option from the Layer 2 Security drop-down, which two tasks must they perform to complete the process? (Choose two)
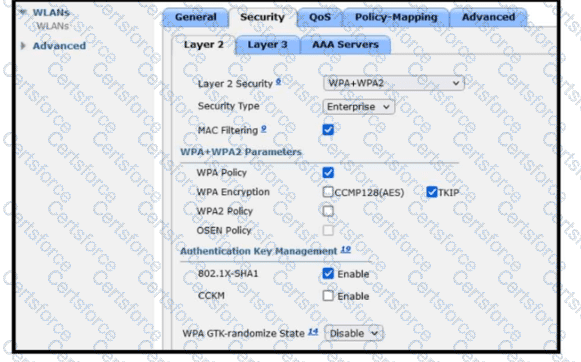
Refer to the exhibit. A guest WLAN must be created that prompts the client for a username and password on the local web page of the WLC. Which two actions must be performed on the Layer 2 tab before enabling the Authentication option on the Layer 3 tab? (Choose two.)
A new DHCP server has been deployed in a corporate environment with lease time set to eight hours. Which CMD command on a Windows-based device allows the engineer to verify the DHCP lease expiration?
Which two QoS tools provide congestion management? (Choose two.)
Which security protocol is appropriate for a WPA3 implementation?
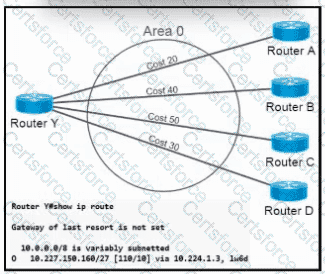
Refer to the exhibit. OSPF neighbors routers A, B, C, and D are sending a route for 10.227.150.160/27. When the current route for 10.227.150.160/27 becomes unavailable, which cost will router Y use to route traffic to 10.227.150.160/27?
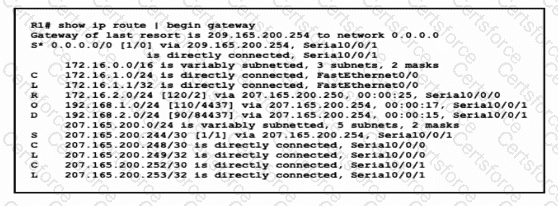
Which interface condition is occurring in this output?

When a site-to-site VPN is configured, which IPsec mode provides encapsulation and encryption of the entire original P packet?
In which way does a spine-and-leaf architecture allow for scalability in a network when additional access ports are required?
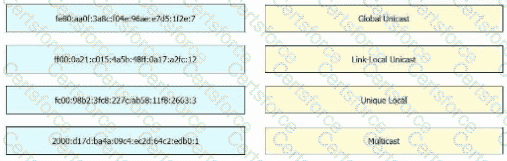
Drag and drop the IPv6 address from the left onto the type on the right.
An engineer requires a switch interface to actively attempt to establish a trunk link with a neighbor switch. What command must be configured?
Refer to the exhibit.
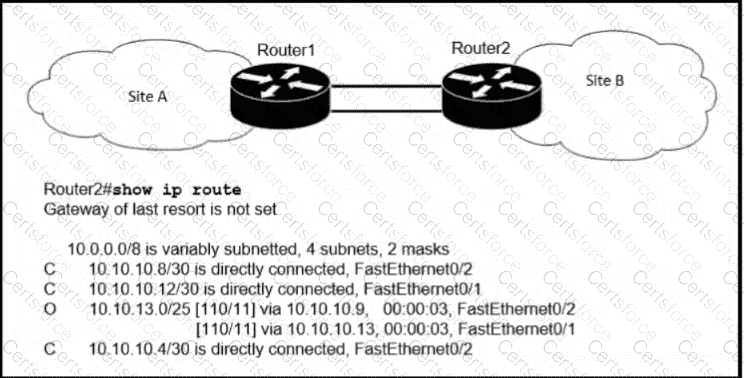
If OSPF Is running on this network, how does Router2 handle traffic from Site B to 10.10.13.128/25 at Site A?
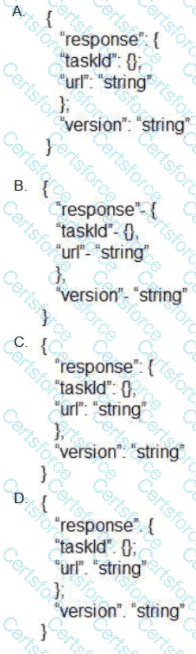
Which output displays a JSON data representation?
How will Link Aggregation be Implemented on a Cisco Wireless LAN Controller?
Which QoS Profile is selected in the GUI when configuring a voice over WLAN deployment?
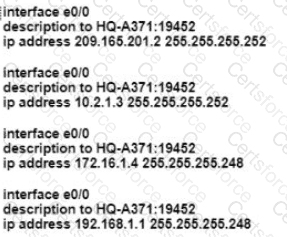
Refer to the exhibit.
What commands are needed to add a subinterface to Ethernet0/0 on R1 to allow for VLAN 20, with IP address 10.20.20.1/24?
When a floating static route is configured, which action ensures that the backup route is used when the primary route fails?
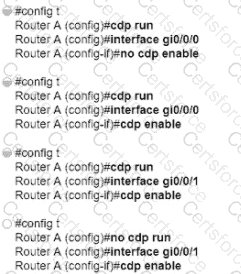
Refer to the exhibit.
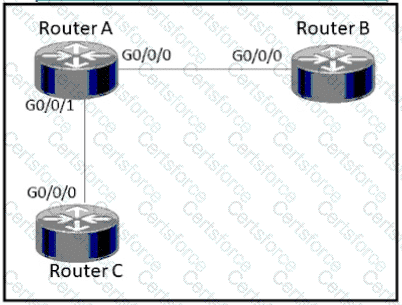
How must router A be configured so that it only sends Cisco Discovery Protocol Information to router C?
Refer to the exhibit.
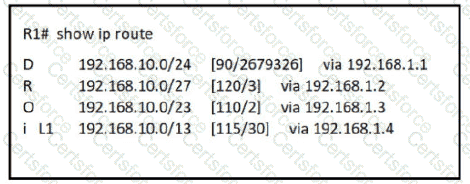
How does router R1 handle traffic to 192.168.10.16?
What are two benefits of controller-based networking compared to traditional networking?
In software defined architectures, which plane is distributed and responsible for traffic forwarding?
How are the switches in a spine-and-leaf topology interconnected?
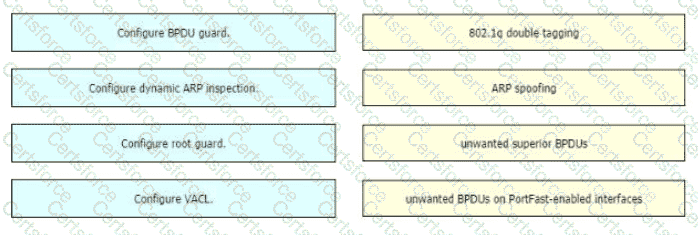
Drag and drop the threat-mitigation techniques from the left onto the types of threat or attack they mitigate on the right.
What is the maximum length of characters used in an SSID?
Connectivity between four routers has been established. IP connectivity must be configured in the order presented to complete the implementation. No dynamic routing protocols are included.
1. Configure static routing using host routes to establish connectivity from router R3 to the router R1 Loopback address using the source IP of 209.165.200.230.
2. Configure an IPv4 default route on router R2 destined for router R4.
3. Configure an IPv6 default router on router R2 destined for router R4.

Which type of wireless encryption is used for WPA2 in preshared key mode?
Refer to the exhibit.
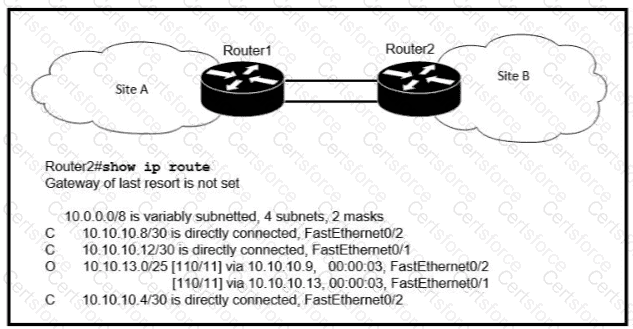
If OSPF is running on this network, how does Router 2 handle traffic from Site B to 10.10.13/25 at Site A?
Which virtual MAC address is used by VRRP group 1?
Which protocol does an IPv4 host use to obtain a dynamically assigned IP address?
Drag and drop the DNS lookup components from the left onto the functions on the right.

An engineer must configure a/30 subnet between two routers. Which usable IP address and subnet mask combination meets this criteria?
What is the purpose of using First Hop Redundancy Protocol in a specific subnet?
What is the total number of users permitted to simultaneously browse the controller management pages when using the AireOS GUI?
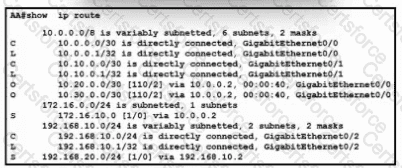
Refer to the exhibit. What is the administrative distance for the advertised prefix that includes the host IP address 192.168.20.1?
How does automation leverage data models to reduce the operational complexity of a managed network?
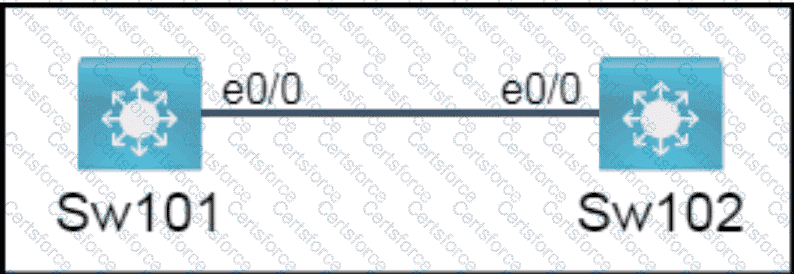
All physical cabling is in place. A company plans to deploy 32 new sites.
The sites will utilize both IPv4 and IPv6 networks.
1 . Subnet 172.25.0.0/16 to meet the subnet requirements and maximize
the number of hosts
Using the second subnet
• Assign the first usable IP address to e0/0 on Sw1O1
• Assign the last usable IP address to e0/0 on Sw102
2. Subnet to meet the subnet requirements and maximize
the number of hosts
c Using the second subnet
• Assign an IPv6 GUA using a unique 64-Bit interface identifier
on e0/0 on Sw101
• Assign an IPv6 GUA using a unique 64-Bit interface identifier
on eO/O on swi02
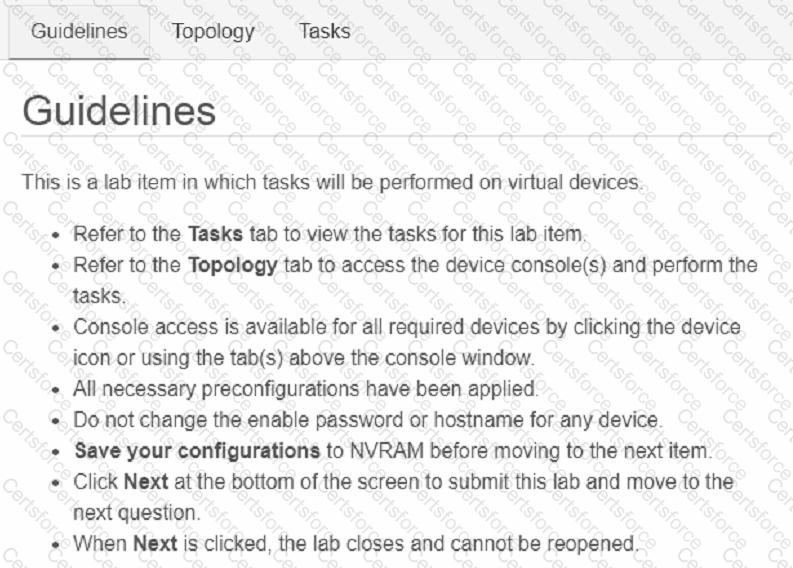
Guidelines
This is a lab item in which tasks will be performed on virtual devices.
• Refer to the Tasks tab to view the tasks for this lab item.
• Refer to the Topology tab to access the device console(s) and perform the tasks.
• Console access is available for all required devices by clicking the device icon or using
the tab(s) above the console window.
• All necessary preconfigurations have been applied.
• Do not change the enable password or hostname for any device.
• Save your configurations to NVRAM before moving to the next item.
• Click Next at the bottom of the screen to submit this lab and move to the next question.
• When Next is clicked, the lab closes and cannot be reopened.