Refer to the exhibit.
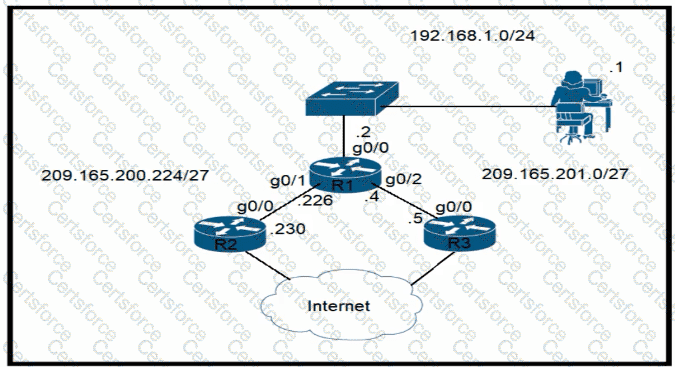
Router R1 currently is configured to use R3 as the primary route to the Internet, and the route uses the default administrative distance settings. A network engineer must configure R1 so that it uses R2 as a backup, but only if R3 goes down. Which command must the engineer configure on R1 so that it correctly uses R2 as a backup route, without changing the administrative distance configuration on the link to R3?
What role does a hypervisor provide for each virtual machine in server virtualization?
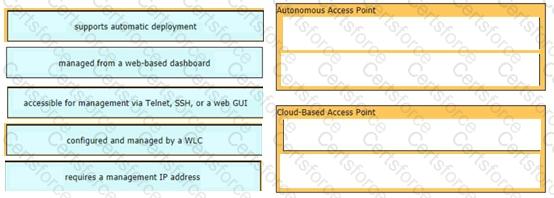
Drag and drop the facts about wireless architectures from the left onto the types of access point on the right. Not all options are used.
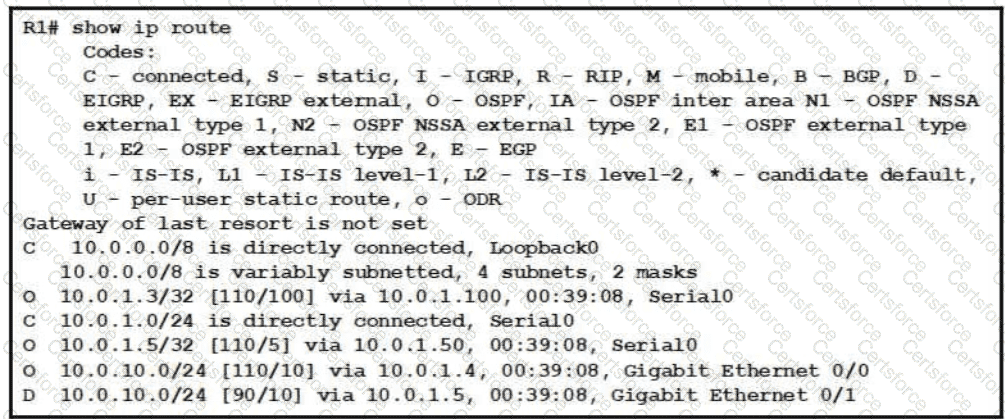
Refer to the exhibit.
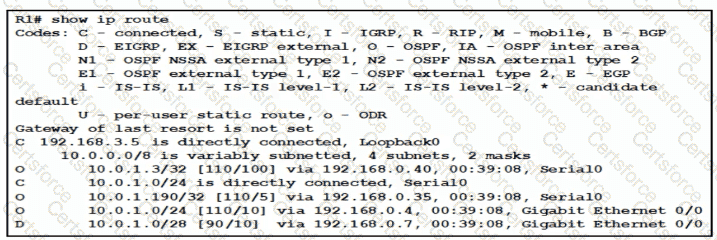
Traffic sourced from the loopback0 Interface is trying to connect via ssh to the host at 10.0.1.15. What Is the next hop to the destination address?
Refer to the exhibit.
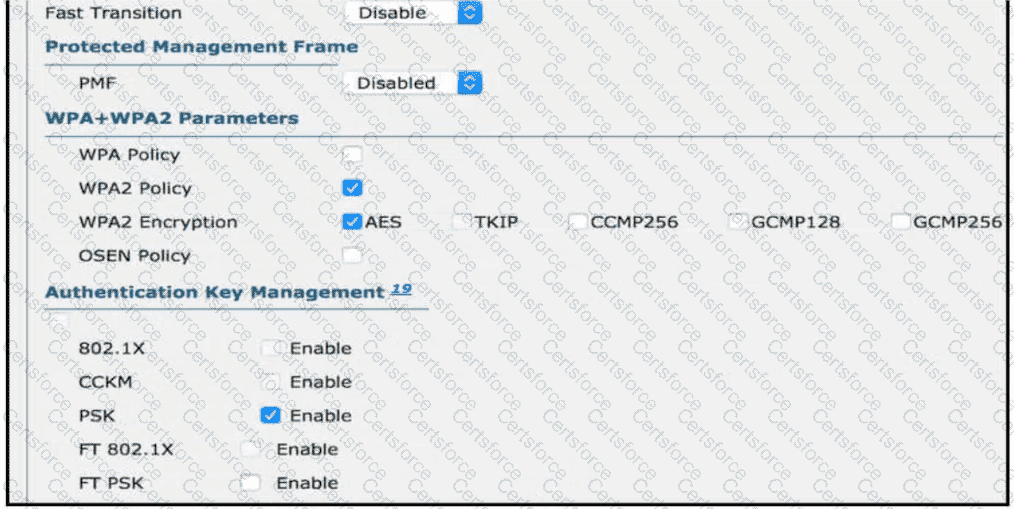
Users need to connect to the wireless network with IEEE 802. 11r-compatible devices. The connection must be maintained as users travel between floors or to other areas in the building What must be the configuration of the connection?
An engineer needs to add an old switch back into a network. To prevent the switch from corrupting the VLAN database which action must be taken?
Refer to the exhibit.
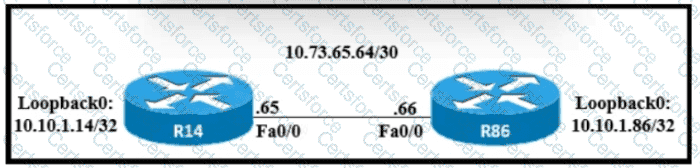
A static route must be configured on R14 to forward traffic for the 172 21 34 0/25 network that resides on R86 Which command must be used to fulfill the request?
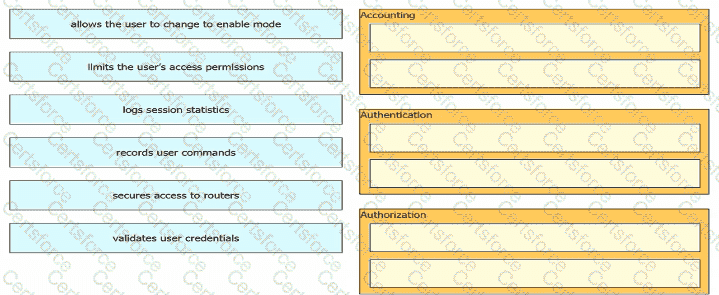
Drag and drop the descriptions of AAA services from the left onto the corresponding services on the right.
An engineer must configure an OSPF neighbor relationship between router R1 and R3 The authentication configuration has been configured and the connecting interfaces are in the same 192.168 1.0/30 sublet. What are the next two steps to complete the configuration? (Choose two.)
Refer to the exhibit.
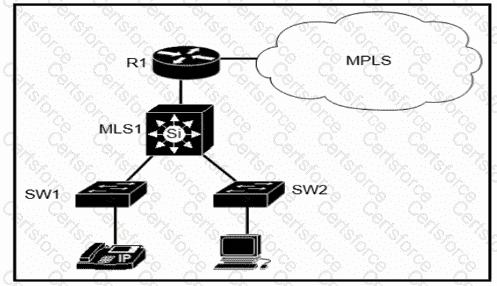
Which plan must be Implemented to ensure optimal QoS marking practices on this network?
Which configuration is needed to generate an RSA key for SSH on a router?
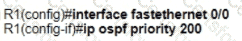
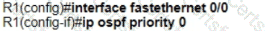
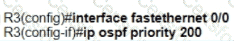
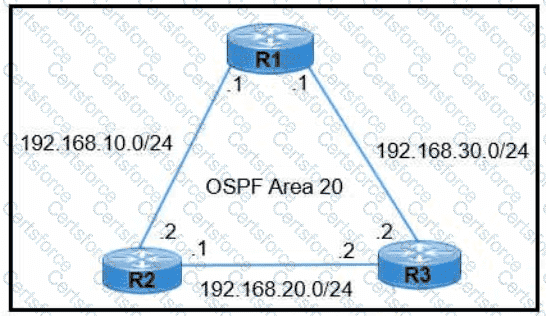
Refer to the exhibit.
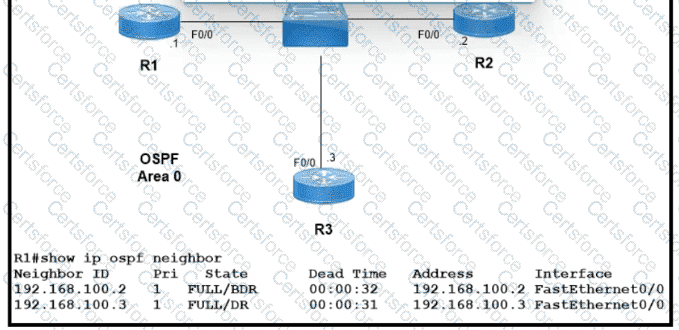
Which two configurations must the engineer apply on this network so that R1 becomes the DR? (Choose two.)
A)
B)
C)
D)
E)
In which situation is private IPv4 addressing appropriate for a new subnet on the network of an organization?
An organization has decided to start using cloud-provided services. Which cloud service allows the organization to install its own operating system on a virtual machine?
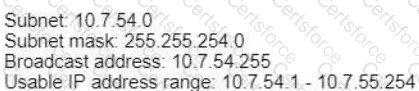
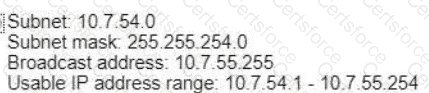
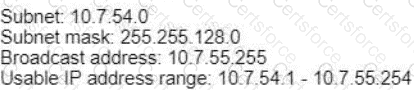
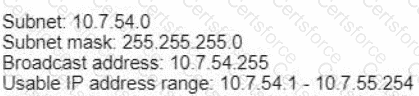
Refer to the exhibit.

The router has been configured with a supernet to accommodate the requirement for 380 users on a subnet The requirement already considers 30% future growth. Which configuration verifies the IP subnet on router R4?
A)
B)
C)
D)
Refer to the exhibit.
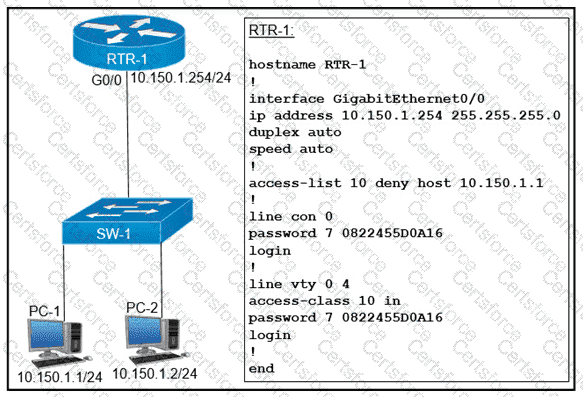
An access list is created to deny Telnet access from host PC-1 to RTR-1 and allow access from all other hosts A Telnet attempt from PC-2 gives this message: " % Connection refused by remote host " Without allowing Telnet access from PC-1, which action must be taken to permit the traffic?
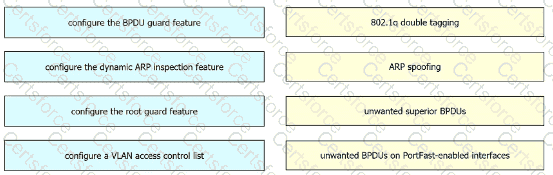
Drag and drop the threat-mitigation techniques from the left onto the types of threat or attack they mitigate on the right.
Refer to the exhibit.
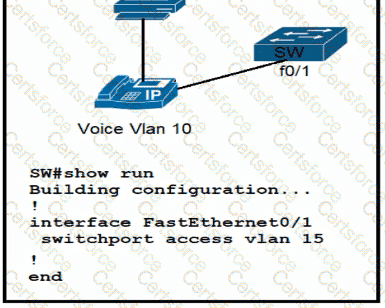
All VLANs are present in the VLAN database. Which command sequence must be applied to complete the configuration?
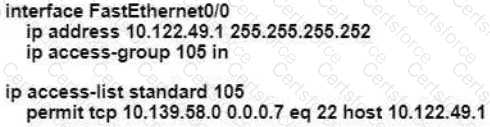
An engineer is configuring remote access to a router from IP subnet 10.139.58.0/28. The domain name, crypto keys, and SSH have been configured. Which configuration enables the traffic on the destination router?
A)
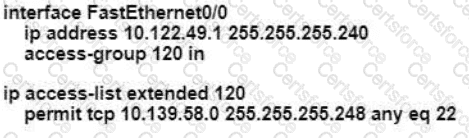
B)
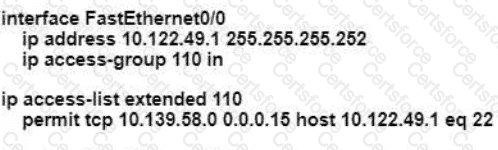
C)
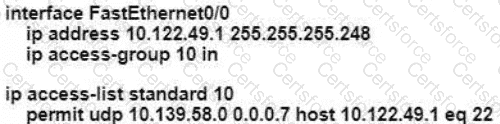
D)
What criteria is used first during me root port selection process?
What is the purpose of a southbound API in a control based networking architecture?
Which two minimum parameters must be configured on an active interface to enable OSPFv2 to operate? (Choose two)
Refer to the exhibit.
Which two commands must be configured on router R1 to enable the router to accept secure remote-access connections? (Choose two)
A frame that enters a switch fails the Frame Check Sequence. Which two interface counters are incremented? (Choose two)
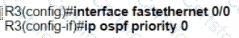
Refer to the exhibit.
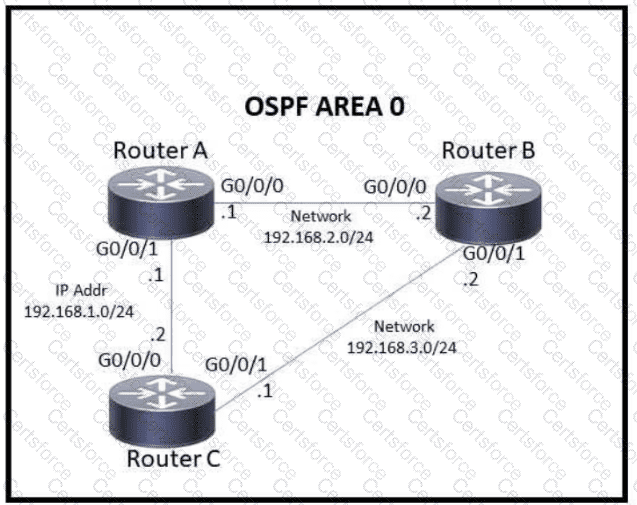
Which action must be taken to ensure that router A is elected as the DR for OSPF area 0?
Refer to the exhibit.
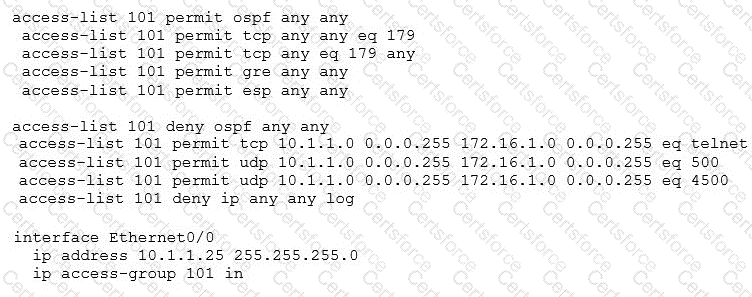
A network administrator has been tasked with securing VTY access to a router. Which access-list entry accomplishes this task?
Which Layer 2 switch function encapsulates packets for different VLANs so that the packets traverse the same port and maintain traffic separation between the VLANs?
Which feature on the Cisco Wireless LAN Controller when enabled restricts management access from specific networks?
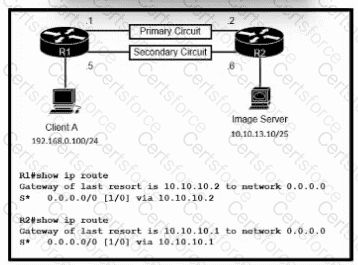
Refer to the exhibit. Routers R1 and R2 have been configured with their respective LAN interfaces. The two circuits are operational and reachable across the WAN. Which command set establishes failover redundancy if the primary circuit goes down?
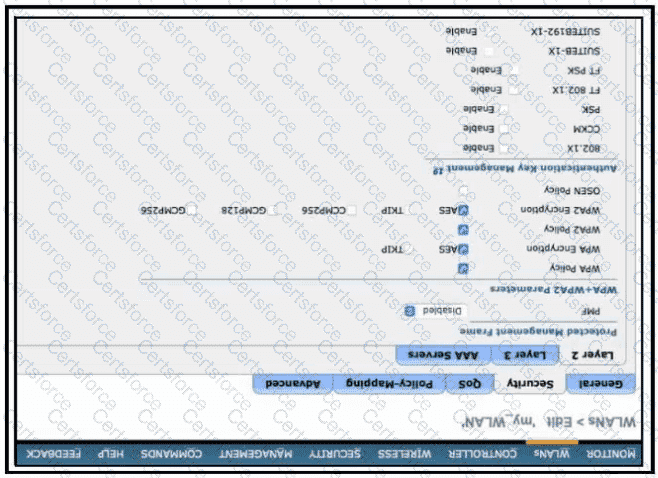
Refer to the exhibit.
Which configuration is needed to configure a WLAN with WPA2 only and with a password that is 63 characters long?
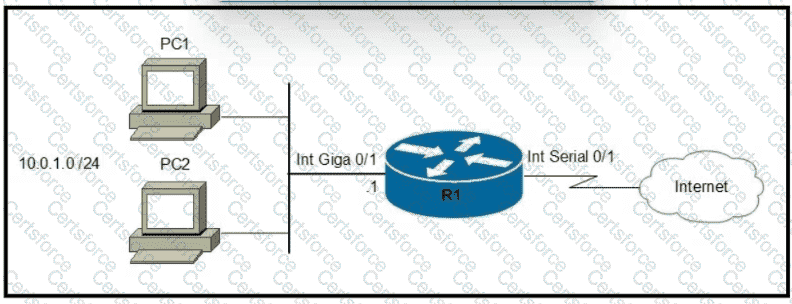
Refer to the exhibit.
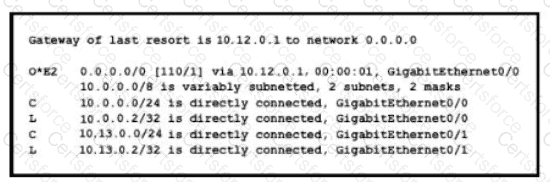
If configuring a static default route on the router with the ip route 0.0.0.0 0.0.0.0 10.13.0.1 120 command how does the router respond?
Refer to the exhibit.
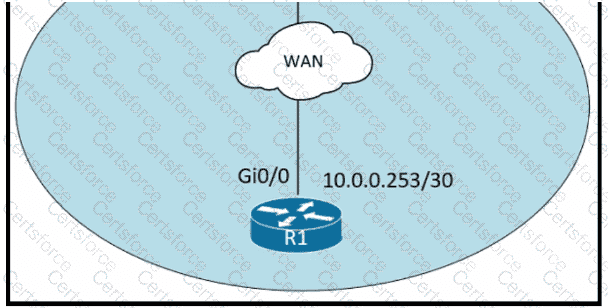
An administrator must turn off the Cisco Discovery Protocol on the port configured with address last usable address in the 10.0.0.0/30 subnet. Which command set meets the requirement?
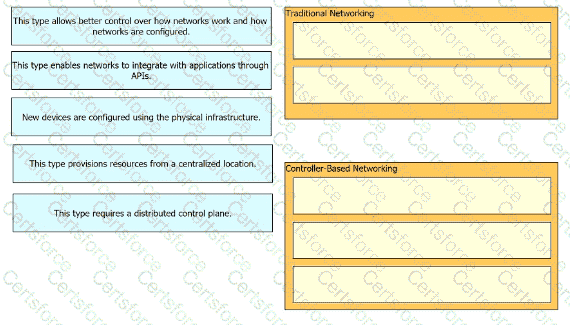
Drag and drop the statements about networking from the left onto the corresponding networking types on the right.
What is a network appliance that checks the state of a packet to determine whether the packet is legitimate?
How does QoS optimize voice traffic?

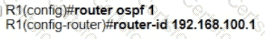
Refer to the exhibit. After the configuration is applied, the two routers fail to establish an OSPF neighbor relationship. what is the reason for the problem?
Refer to the exhibit.
Web traffic is coming in from the WAN interface. Which route takes precedence when the router is processing traffic destined for the LAN network at 10 0.10.0/24?
What is the difference between IPv6 unicast and anycast addressing?
Which QoS traffic handling technique retains excess packets in a queue and reschedules these packets for later transmission when the configured maximum bandwidth has been surpassed?
Refer to the exhibit.
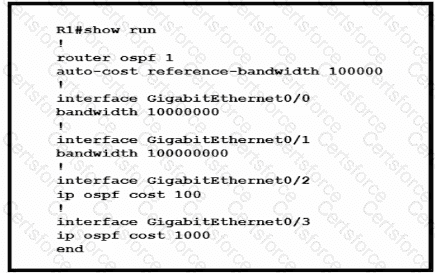
Router R1 resides in OSPF Area 0. After updating the R1 configuration to influence the paths that it will use to direct traffic, an engineer verified that each of the four Gigabit interfaces has the same route to 10.10.0.0/16. Which interface will R1 choose to send traffic to reach the route?
OSPF must be configured between routers R1 and R2. Which OSPF configuration must be applied to router R1 to avoid a DR/BDR election?
Which type of IPv6 address is similar to a unicast address but is assigned to multiple devices on the same network at the same time?
Which type of network attack overwhelms the target server by sending multiple packets to a port until the half-open TCP resources of the target are exhausted?
When configuring a WLAN with WPA2 PSK in the Cisco Wireless LAN Controller GUI, which two formats are available to select? (Choose two)
Refer to the exhibit.
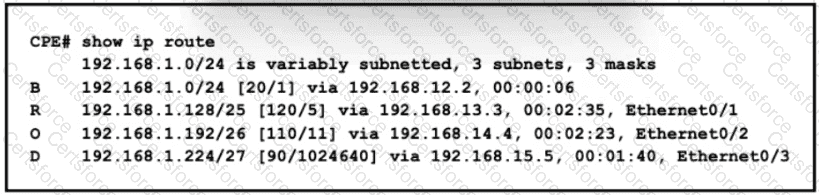
All traffic enters the CPE router from interface Serial0/3 with an IP address of 192 168 50 1 Web traffic from the WAN is destined for a LAN network where servers are load-balanced An IP packet with a destination address of the HTTP virtual IP of 192 1681 250 must be forwarded Which routing table entry does the router use?
Refer to the exhibit.
R1 learns all routes via OSPF Which command configures a backup static route on R1 to reach the 192 168.20.0/24 network via R3?
What Is the path for traffic sent from one user workstation to another workstation on a separate switch In a Ihree-lter architecture model?
Which WLC management connection type is vulnerable to man-in-the-middle attacks?
Which protocol is used for secure remote CLI access?
What is one reason to implement LAG on a Cisco WLC?