An organization is increasing its focus on training that addresses new social engineering and phishing attacks. Which of the following is the organization most concerned about?
During a security assessment using an EDR solution, a security engineer generates the following report about the assets in the system:
Initial report:
Device | Type | EDR status | Infection Status
LN002 | Linux SE | Enabled (unmanaged) | Unknown
OWIN23 | Windows 7 | Enabled | Clean
OWIN29 | Windows 10 | Enabled (bypass) | Clean
MAC005 | Mac OS | Enabled | Clean
After five days:
Device | Type | EDR status | Infection Status
LN002 | Linux SE | Enabled (unmanaged) | Unknown
OWIN23 | Windows 7 | Enabled | Clean
OWIN29 | Windows 10 | Enabled (bypass) | Infected
MAC005 | Mac OS | Disabled | Clean
Which of the following most likely enabled the infection?
An organization hires a security consultant to establish a SOC that includes athreat-modeling function. During initial activities, the consultant works with system engineers to identify antipatterns within the environment. Which of the following is most critical for the engineers to disclose to the consultant during this phase?
A security architect is designing Zero Trust enforcement policies for all end users. The majority of users work remotely and travel frequently for work. Which of the following controls should the security architect do first?
A vulnerability can on a web server identified the following:
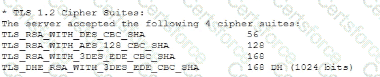
Which of the following actions would most likely eliminate on path decryption attacks? (Select two).
A healthcare system recently suffered from a ransomware incident. As a result, the board of directors decided to hire a security consultant to improve existing network security. The security consultant found that the healthcare network was completely flat, had no privileged access limits, and had open RDP access to servers with personal health information. As the consultant builds the remediation plan, which of the following solutions would best solve these challenges? (Select three).
A company that relies on an COL system must keep it operating until a new solution is available Which of the following is the most secure way to meet this goal?
A company has the following requirements for a cloud-based web application:
• Must authenticate customers
• Must prevent data exposure
• Must allow customer access to data throughout the cloud environment
• Must restrict access by specific regions
Which of the following solutions best addresses these security requirements?
All organization is concerned about insider threats from employees who have individual access to encrypted material. Which of the following techniques best addresses this issue?
PKI can be used to support security requirements in the change management process. Which of the following capabilities does PKI provide for messages?