A pharmaceutical lab hired a consultant to identify potential risks associated with Building 2, a new facility that is under construction. The consultant received the IT project plan, which includes the following VLAN design:
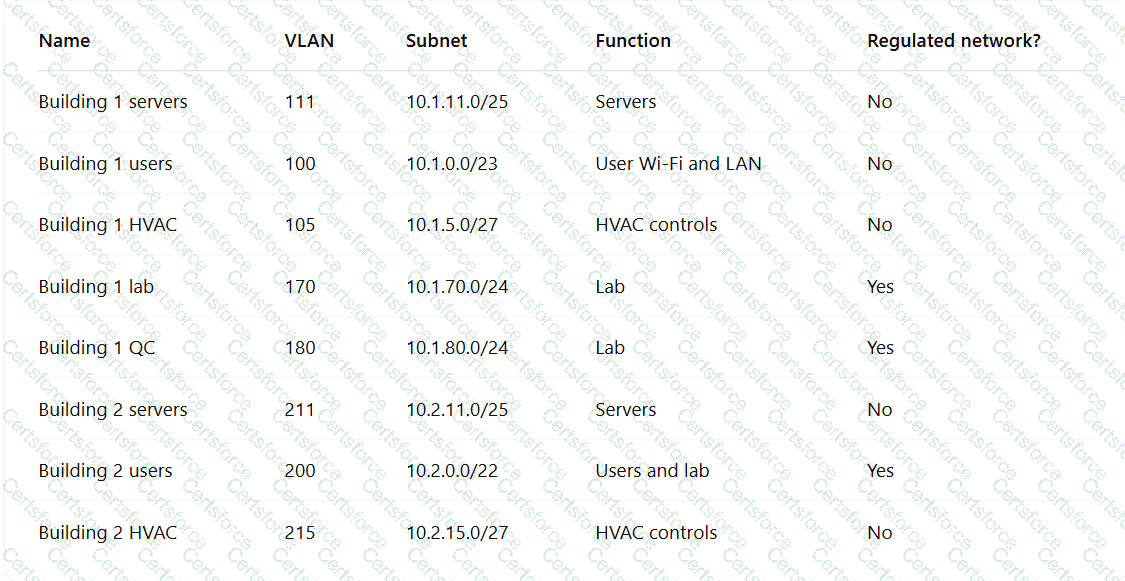
Which of the following TTPs should the consultant recommend be addressed first?
A security officer performs due diligence activities before implementing a third-party solution into the enterprise environment. The security officer needs evidence from the third party that a data subject access request handling process is in place. Which of the following is the security officer most likely seeking to maintain compliance?
A security engineer reviews an after action report from a previous security breach and notes a long lag time between detection and containment of a compromised account. The engineer suggests using SOAR to address this concern. Which of the following best explains the engineer ' s goal?
A security engineer is given the following requirements:
• An endpoint must only execute Internally signed applications
• Administrator accounts cannot install unauthorized software.
• Attempts to run unauthorized software must be logged
Which of the following best meets these requirements?
A security engineer wants to stay up-to-date on new detections that are released on a regular basis. The engineer ' s organization uses multiple tools rather than one specific vendor security stack. Which of the following rule-based languages is the most appropriate to use as a baseline for detection rules with the multiple security tool setup?
A security engineer performed a code scan that resulted in many false positives. The security engineer must find asolution that improves the quality of scanning results before application deployment. Which of the following is the best solution?
A security engineer needs to create multiple servers in a company ' s private cloud. The servers should have a virtual network infrastructure that supports connectivity, as well as security configurations applied using predefined templates. Which of the following is the best option for the security engineer to consider for the deployment?
Developers have been creating and managing cryptographic material on their personal laptops fix use in production environment. A security engineer needs to initiate a more secure process. Which of thefollowing is the best strategy for the engineer to use?
A systems administrator works with engineers to process and address vulnerabilities as a result of continuous scanning activities. The primary challenge faced by the administrator is differentiating between valid and invalid findings. Which of the following would the systems administrator most likely verify is properly configured?
A security analyst receives the following SIEM alert for review:
Time | Event
03/07/2025 UTC 13:54:06 | MACHINE: hr_talent_01.corp.local " cd " SUCCESS
03/07/2025 UTC 13:54:07 | MACHINE: hr_talent_01.corp.local " cd ../../ " SUCCESS
03/07/2025 UTC 13:54:08 | MACHINE: hr_talent_01.corp.local " sudo cat /etc/shadow " SUCCESS
Which of the following best describes the incident that occurred on the device?