A penetration tester reviews the following router configuration:
set-system services ssh root login-allow
set-system services web-management https allow
set-system services syslog file interactive
set-system services log mode stream
set-interfaces 0 family inet address 10.12.14.1/8
Which of the following changes is the best way to enhance security?
John Doe ' s email account was compromised. The attacker ' s access to John Doe ' s account was removed and MFA was implemented. The attacker convinced Joe Roe in the accounting department to pay a fraudulent invoice through email exchanges. A security analyst is reviewing the headers from the initial email that Joe Roe received:
Received: from 221.15.11.103 (221.15.11.103.mta.com [221.15.11.103])
by with esmtps (TLS 1.2)
Received-SPF: pass
Received: from 18.132.124.10 (18.132.124.10-internal.com [18.132.124.10])
by mx7sgwt-3S (Postfix) with ESMTPS id zRhQ22fmNnQCdys
DKIM-Signature: v=1; c=relaxed/relaxed; d=example.com;
s=default; t=1672873468;
h=To: Message-ID: Date: Content-Type: Subject: From: From: To: Cc: Subject;
To: jroe@example.com
Message-ID: _73/A4-32616-C36L8ZbYC4p
Date: Mon, 07 Apr 2025 +0000
Content-Type: multipart/alternative; boundary=
MIME-Version: 1.0
Reply-To: jdoe@exampl.com
Subject: FW: Invoice
From: jdoe@exampl.com
X-SpamProbability: 0.095349
Which of the following best explains how the attacker was able to get the invoice paid?
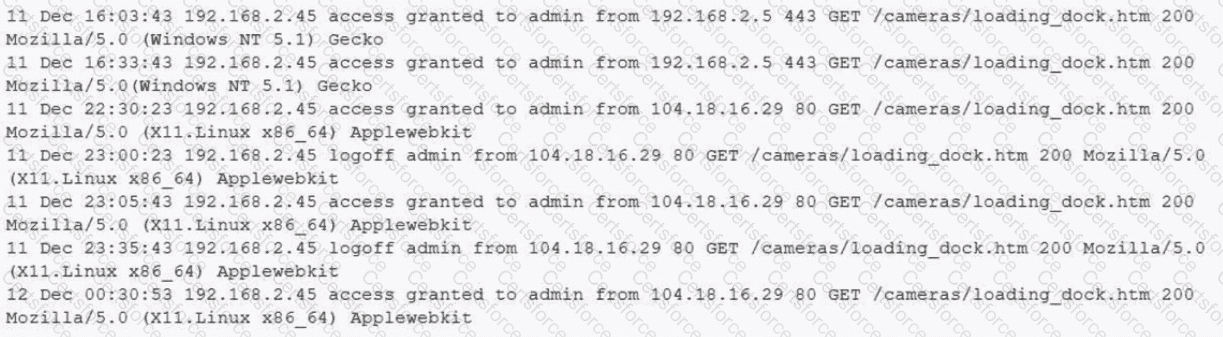
A building camera is remotely accessed and disabled from the remote console application during off-hours. A security analyst reviews the following logs:
A security architect is onboarding a new EDR agent on servers that traditionally do not have internet access. In order for the agent to receive updates and report back to the management console, some changes must be made. Which of the following should the architect do to best accomplish this requirement? (Select two).
An analyst wants to conduct a risk assessment on a new application that is being deployed. Given the following information:
• Total budget allocation for the new application is unavailable.
• Recovery time objectives have not been set.
• Downtime loss calculations cannot be provided.
Which of the following statements describes the reason a qualitative assessment is the best option?
In order to follow new regulations, the Chief Information Security Officer plans to use a defense-in-depth approach for a perimeter network. Which of the following protections would best achieve this goal?
A security engineer needs to remediate a SWEET32 vulnerability in an OpenSSH-based application and review existing configurations. Which of the following should the security engineer do? (Select two.)
A company implemented a NIDS and a NIPS on the most critical environments. Since this implementation, the company has been experiencing network connectivity issues. Which of the following should the security architect recommend for a new NIDS/NIPS implementation?
A company is preparing to move a new version of a web application to production. No issues were reported during security scanning or quality assurance in the CI/CD pipeline. Which of the following actions should thecompany take next?
Engineers at a cloud service provider can now access newly deployed customer environments from their personal laptops. The engineers are concerned that unmanaged systems may present unknown vulnerabilities to customer environments, which might become a significant liability to the service provider. Which of the following deployments provides the most secure solution to prevent access through non-authorized endpoints?
A company experienced a data breach, resulting in the disclosure of extremely sensitive data regarding a merger. As a regulated entity, the company must comply with reporting and disclosure requirements. The company is concerned about its public image and shareholder values. Which of the following best supports the organization in addressing its concerns?