A company developed a new solution that needs to track any changes to the data, and the changes need to be quickly identified. If any changes are attempted without prior approval, multiple events must be triggered, such as:
Raising alerts
Blocking the unapproved changes
Quickly removing access to the data
Which of the following solutions best meets these requirements?
A global organization is reviewing potential vendors to outsource a critical payroll function. Each vendor ' s plan includes using local resources in multiple regions to ensure compliance with all regulations. The organization ' s Chief Information Security Officer is conducting a risk assessment on the potential outsourcing vendors ' subprocessors. Which of the following best explains the need for this risk assessment?
After an incident response exercise, a security administrator reviews the following table:

Which of the following should the administrator do to beat support rapid incident response in the future?
A company implements an Al model that handles sensitive and personally identifiable information. Which of the following threats is most likely the company ' s primary concern?
A company migrating to aremote work model requires that company-owned devices connect to a VPN before logging in to the device itself. The VPN gateway requires that a specific key extension is deployed to the machine certificates in the internal PKI. Which of the following best explains this requirement?
A security architect is performing threat-modeling activities related to an acquired overseas software company that will be integrated with existing products and systems Once its software is integrated, the software company will process customer data for the acqumng company Given the following:
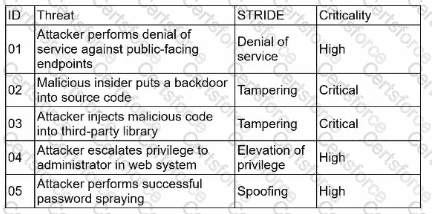
Which of the following mitigations would reduce the risk of the most significant threats?
A company ' s security policy states that any publicly available server must be patched within 12 hours after a patch is released A recent llS zero-day vulnerability was discovered that affects all versions of the Windows Server OS:
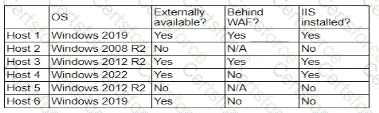
Which of the following hosts should a security analyst patch first once a patch is available?
A security administrator needs to review the efficacy of the detection rules configured on the SIEM by employing real-world attacker TTPs. Which of the following actions should the security administrator take to accomplish this objective?
A global organization wants to manage all endpoint and user telemetry. The organization also needs to differentiate this data based on which office it is correlated to. Which of the following strategies best aligns with this goal?
An organization is implementing Zero Trust architecture A systems administrator must increase the effectiveness of the organization ' s context-aware access system. Which of the following is the best way to improve the effectiveness of the system?