Refer to exhibit.
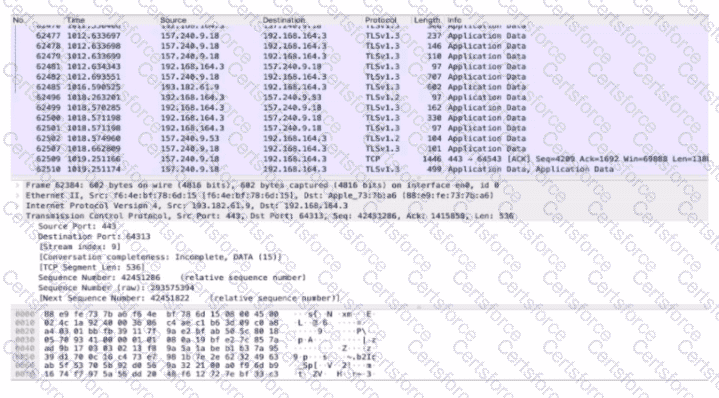
An analyst performs the analysis of the pcap file to detect the suspicious activity. What challenges did the analyst face in terms of data visibility?
An analyst received a ticket regarding a degraded processing capability for one of the HR department's servers. On the same day, an engineer noticed a disabled antivirus software and was not able to determine when or why it occurred. According to the NIST Incident Handling Guide, what is the next phase of this investigation?
Which statement describes patch management?
How does agentless monitoring differ from agent-based monitoring?
What is the impact of encapsulation on the network?
An engineer received a ticket to investigate a potentially malicious file detected by a malware scanner that was trying to execute multiple commands. During the initial review, the engineer discovered that the file was created two days prior. Further analyses show that the file was downloaded from a known malicious domain after a successful phishing attempt on an asset owner. At which phase of the Cyber Kill Chain was this attack mitigated?
Which type of evidence supports a theory or an assumption that results from initial evidence?
What is the relationship between a vulnerability and a threat?
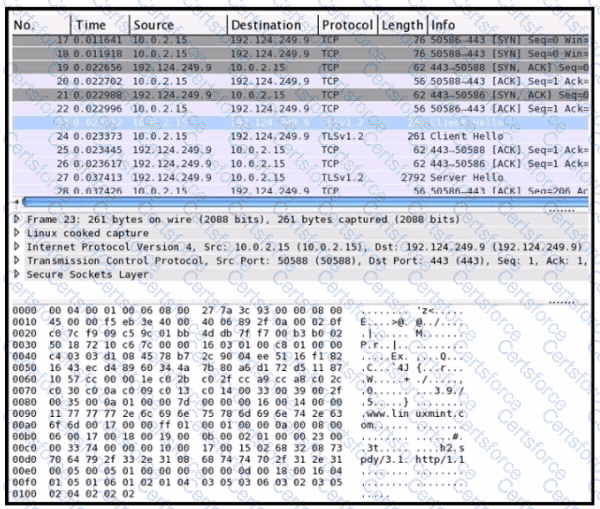
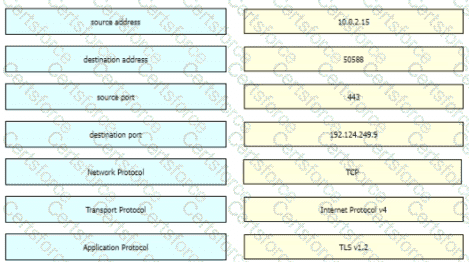
Refer to the exhibit Drag and drop the element names from the left onto the corresponding pieces of the PCAP file on the right.
What is data encapsulation?