An analyst must choose one source of information for further troubleshooting. A key requirement is to use low storage space over the next 12 months while being able to quickly determine the source and scope of an attack to effectively mitigate it. Which source of information should the analyst choose?
A user received a targeted spear-phishing email and identified it as suspicious before opening the content. To which category of the Cyber Kill Chain model does to this type of event belong?
Which attack represents the evasion technique of resource exhaustion?
An organization that develops high-end technology is going through an internal audit The organization uses two databases The main database stores patent information and a secondary database stores employee names and contact information A compliance team is asked to analyze the infrastructure and identify protected data Which two types of protected data should be identified? (Choose two)
Refer to the exhibit.
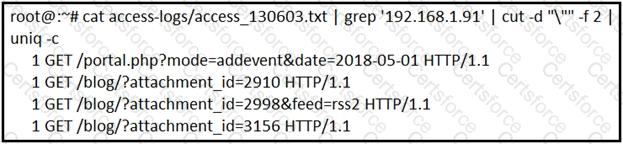
What is depicted in the exhibit?
A user received an email attachment named "Hr405-report2609-empl094.exe" but did not run it. Which category of the cyber kill chain should be assigned to this type of event?
A SOC analyst is investigating an incident that involves a Linux system that is identifying specific sessions. Which identifier tracks an active program?
What is the purpose of a ransomware attack?
What is the impact of encryption?
An organization's security team detected network spikes coming from the internal network. An investigation concluded that the spike in traffic was from intensive network scanning. How must the analyst collect the traffic to isolate the suspicious host?