What is threat hunting?
Which type of data is used to detect anomalies in the network?
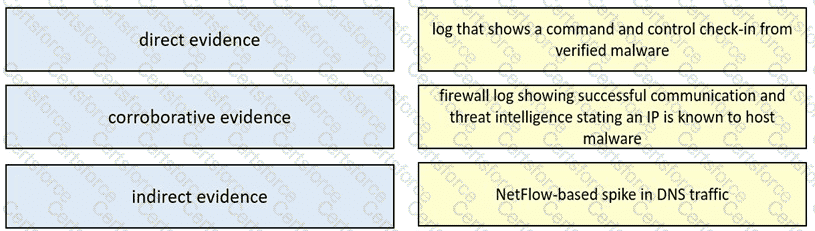
Drag and drop the type of evidence from the left onto the description of that evidence on the right.
What is an evasion technique?
Which two measures are used by the defense-m-depth strategy? (Choose two)
A security engineer must determine why a new core application does not work as desired The client can send requests toward the application server but receives no response One of the requirements is to gather all packets Data needs to be reliable without any delay or packet drops Which solution best meets this need?
Refer to the exhibit.
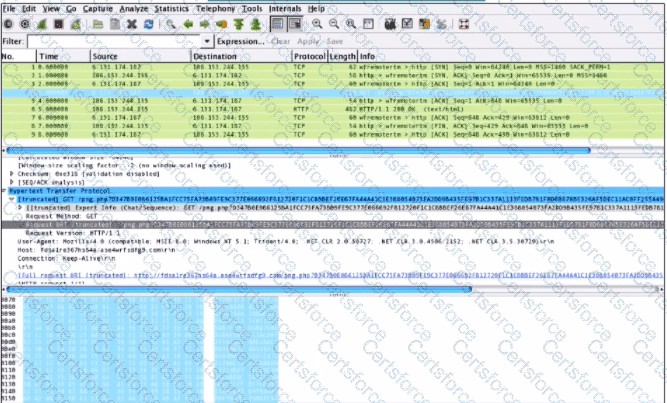
What is shown in this PCAP file?
An engineer needs to discover alive hosts within the 192.168.1.0/24 range without triggering intrusive portscan alerts on the IDS device using Nmap. Which command will accomplish this goal?
An organization is cooperating with several third-party companies. Data exchange is on an unsecured channel using port 80 Internal employees use the FTP service to upload and download sensitive data An engineer must ensure confidentiality while preserving the integrity of the communication. Which technology must the engineer implement in this scenario'?
A security team receives a ticket to investigate suspicious emails sent to company employees from known malicious domains. Further analysis shows that a targeted phishing attempt was successfully blocked by the company’s email antivirus. At which step of the Cyber Kill Chain did the security team mitigate this attack?