Which event artifact is used to identify HTTP GET requests for a specific file?
What is the difference between mandatory access control (MAC) and discretionary access control (DAC)?
Which evasion method is being used when TLS is observed between two endpoints?
Refer to the exhibit.
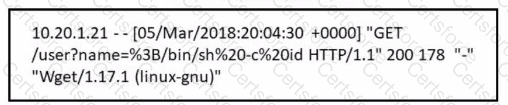
Which attack is being attempted against a web application?
When communicating via TLS, the client initiates the handshake to the server and the server responds back with its certificate for identification.
Which information is available on the server certificate?
An analyst performs traffic analysis to detect data exfiltration and identifies a high frequency of DNS requests in a small period of time Which technology makes this behavior feasible?
During which phase of the forensic process are tools and techniques used to extract information from the collected data?
Which management concept best describes developing, operating, maintaining, upgrading, and disposing of all resources?
What is the difference between a threat and an exploit?
Refer to the exhibit.
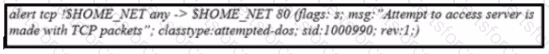
What is the outcome of the command?