Which security monitoring data type requires the largest storage space?
What describes the defense-m-depth principle?
Refer to exhibit.
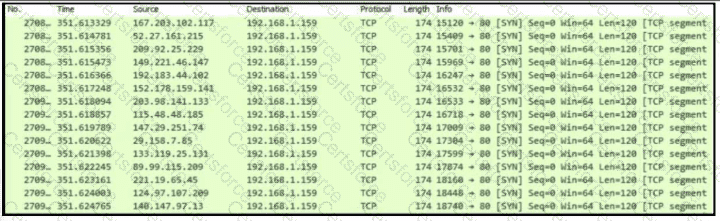
An engineer is Investigating an Intrusion and Is analyzing the pcap file. Which two key elements must an engineer consider? (Choose two.)
An engineer runs a suspicious file in a sandbox analysis tool to see the outcome. The analysis report shows that outbound callouts were made post infection.
Which two pieces of information from the analysis report are needed to investigate the callouts? (Choose two.)
Refer to the exhibit.
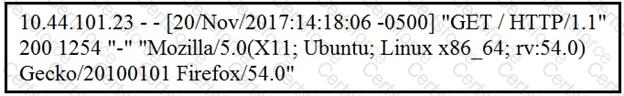
What does the message indicate?
What is a ransomware attack?
What is the difference between an attack vector and attack surface?
What should an engineer use to aid the trusted exchange of public keys between user tom0411976943 and dan1968754032?
An organization has recently adjusted its security stance in response to online threats made by a known hacktivist group.
What is the initial event called in the NIST SP800-61?
An engineer must gather data for monitoring purposes from different network devices. The engineer needs to collect events from the local network and use that information for packet sniffing. The solution must create an exact copy of traffic and provide full fidelity. Which solution should the engineer use?