A CMS plugin creates two files that are accessible from the Internet myplugin html and exploitable php A newly discovered exploit takes advantage of an injection vulnerability m exploitable php To exploit the vulnerability an HTTP POST must be sent with specific variables to exploitable php A security engineer notices traffic to the webserver that consists of only HTTP GET requests to myplugin html Which category does this activity fall under?
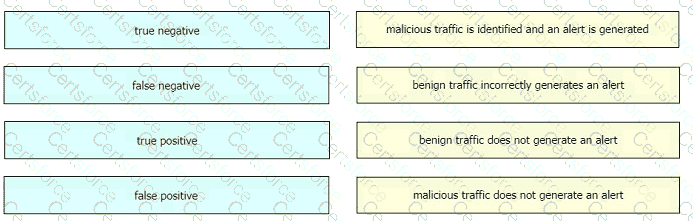
Drag and drop the event term from the left onto the description on the right.
In digital communications, which method is recommended for securely exchanging public keys between users T0n2262144790 and D4n4126220794?
Which category relates to improper use or disclosure of PII data?
Refer to the exhibit.

Which type of log is displayed?
What is a Heartbleed vulnerability?
How does an attack surface differ from an attack vector?
Which of these is a defense-in-depth strategy principle?
Refer to the exhibit.
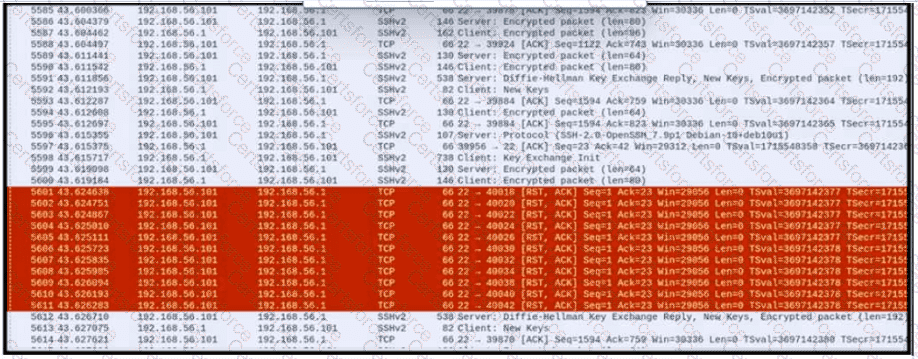
An engineer is analyzing a PCAP file after a recent breach An engineer identified that the attacker used an aggressive ARP scan to scan the hosts and found web and SSH servers. Further analysis showed several SSH Server Banner and Key Exchange Initiations. The engineer cannot see the exact data being transmitted over an encrypted channel and cannot identify how the attacker gained access How did the attacker gain access?
During which phase of the forensic process is data that is related to a specific event labeled and recorded to preserve its integrity?