Which regex matches only on all lowercase letters?
When an event is investigated, which type of data provides the investigate capability to determine if data exfiltration has occurred?
Refer to the exhibit.
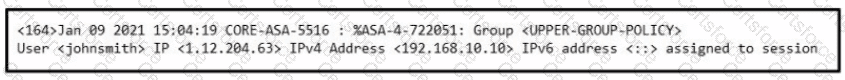
Which type of evidence is this file?
Which type of data collection requires the largest amount of storage space?
What is vulnerability management?
Which security principle is violated by running all processes as root or administrator?
Drag and drop the security concept on the left onto the example of that concept on the right.

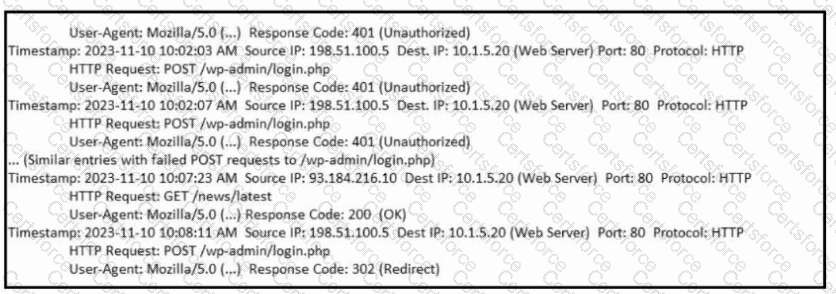
Refer to the exhibit. What is occurring?
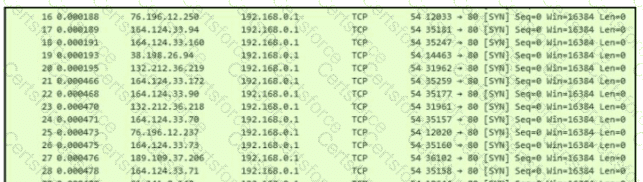
A company is using several network applications that require high availability and responsiveness, such that milliseconds of latency on network traffic is not acceptable. An engineer needs to analyze the network and identify ways to improve traffic movement to minimize delays. Which information must the engineer obtain for this analysis?
Refer to the exhibit.
Which application-level protocol is being targeted?