Refer to the exhibit.
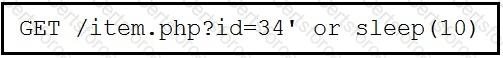
This request was sent to a web application server driven by a database. Which type of web server attack is represented?
What is the difference between inline traffic interrogation (TAPS) and traffic mirroring (SPAN)?
Which metric should be used when evaluating the effectiveness and scope of a Security Operations Center?
Which two elements of the incident response process are stated in NIST Special Publication 800-61 r2? (Choose two.)
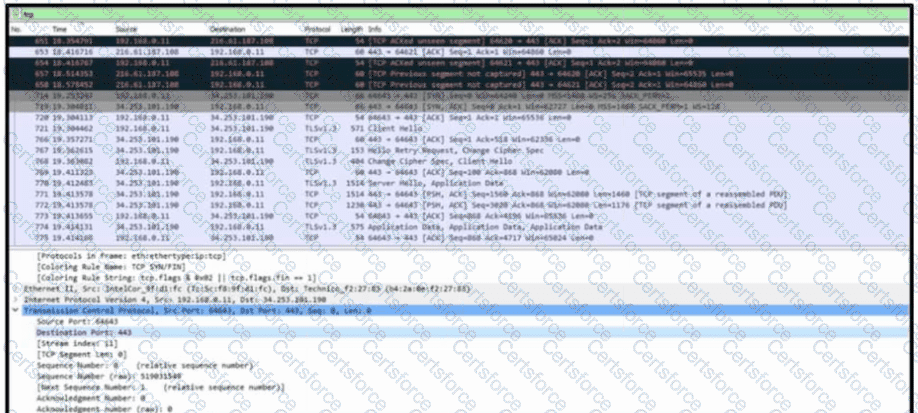
Refer to the exhibit. A communication issue exists between hosts 192.168.0.11 and 34.253.101.190. What is a description of the initial TCP connection?
Which process is used when IPS events are removed to improve data integrity?
What is a comparison between rule-based and statistical detection?
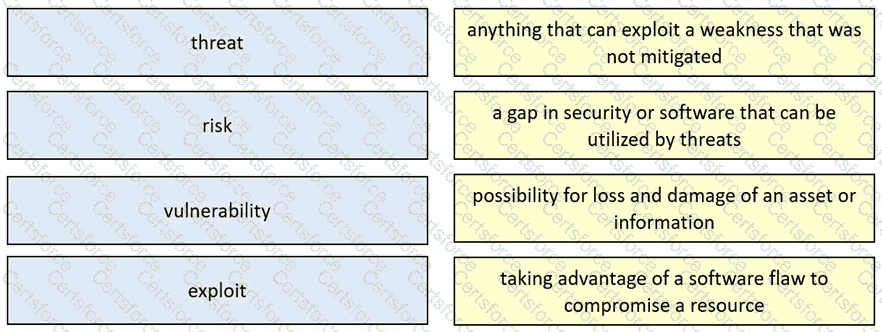
Drag and drop the security concept from the left onto the example of that concept on the right.
An engineer must configure network systems to detect command-and-control communications by decrypting ingress and egress perimeter traffic and allowing network security devices to detect malicious outbound communications. Which technology must be used to accomplish this task?
What is a description of a social engineering attack?