What is a benefit of independent resource scaling in Cisco
HyperFlex hybrid architecture?
Which solution provides remote and direct file-level access to users and systems?
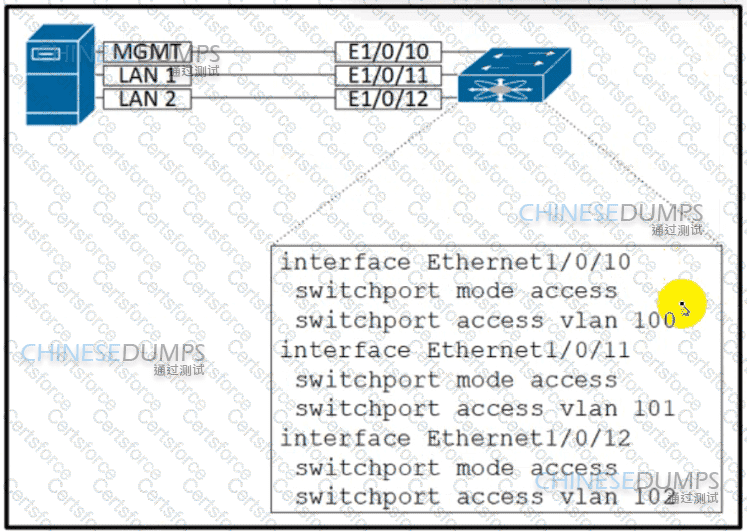
Refer to the exhibit An engineer must access a Cisco UCS C-Series server KVM from a remote location. The engineer must use the out-of-band interface to access the KVM Which configuration set meets these requirements?
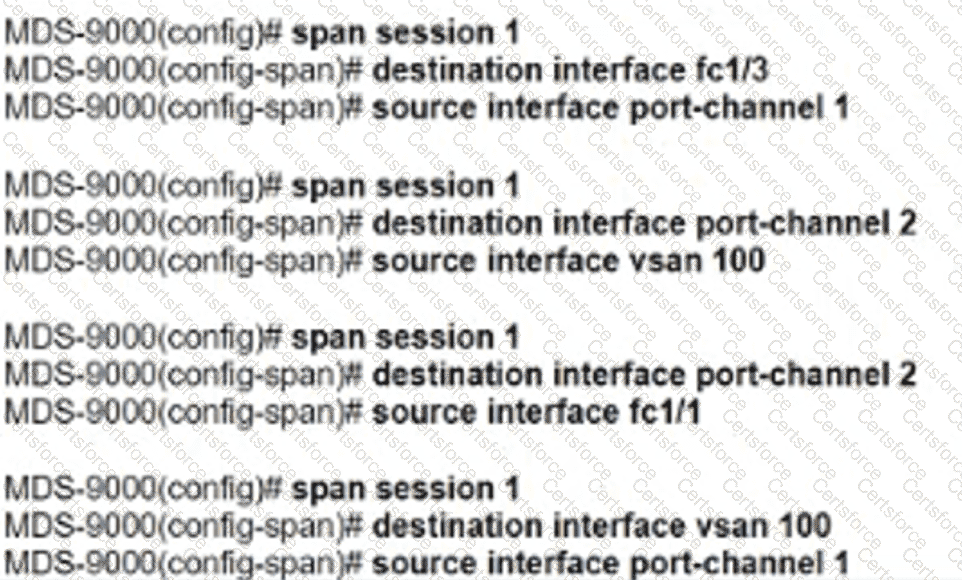
Refer to the exhibit.
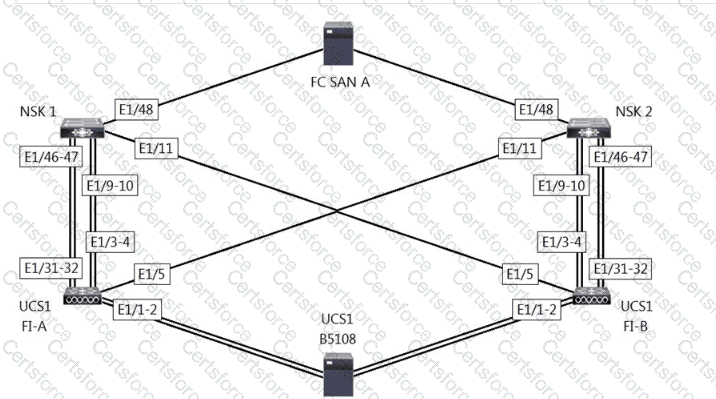
A network engineer must configure port E1/31- 32 to forward only storage server traffic of VLAN 200 on Cisco fabric interconnects A and B. Port E1/31- 32 is not reserved for any other traffic. Which port type must be configured to accomplish this goal?
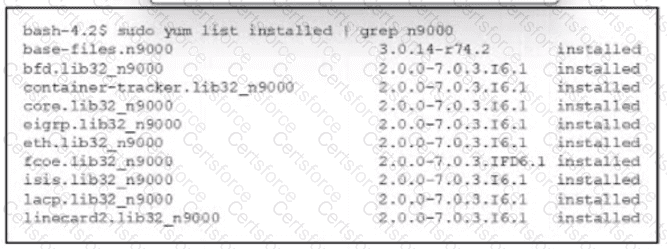
Refer to the exhibit. The list of RPM packages was installed in a Bash shell of a Cisco Nexus 9000 Series Switch. Which action must be used to install and enable a BGP feature on the switch?
What is an advantage of using Network File System (NFS) rather than Storage Area Network (SAN)?
Which protocol supports mounting shared folders and access to storage at the file level?
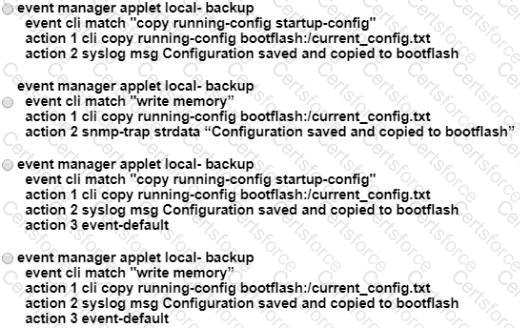
A network engineer must create an EEM script that saves a copy of the running configuration on bootflash and writes a message to syslog when a user saves the configuration to a Cisco Nexus switch. Which configuration set should be applied to complete this task?
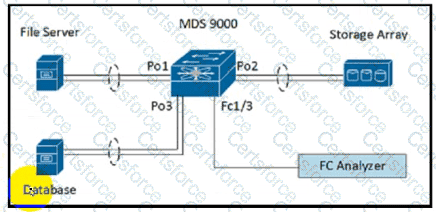
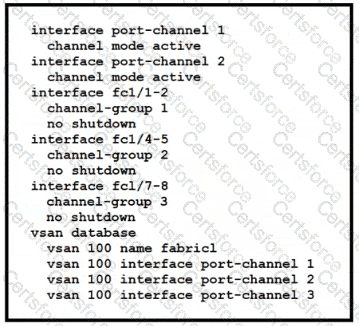
Refer to the exhibit. A storage engineer must monitor the traffic from the file server to the FC analyzer. The file server and the database use the same storage array. Which configuration must be applied to the Cisco MDS 9000 Series Switch to accomplish this goal?
The Cisco UCS blade chassis must send SNMPv3 traps to a network monitoring system. The SNMP trap messages should be authenticated and have protection from closure. Which SNMP security privileged level should be configured?