A company is adding a clause to its AUP that states employees are not allowed to modify the operating system on mobile devices. Which of the following vulnerabilities is the organization addressing?
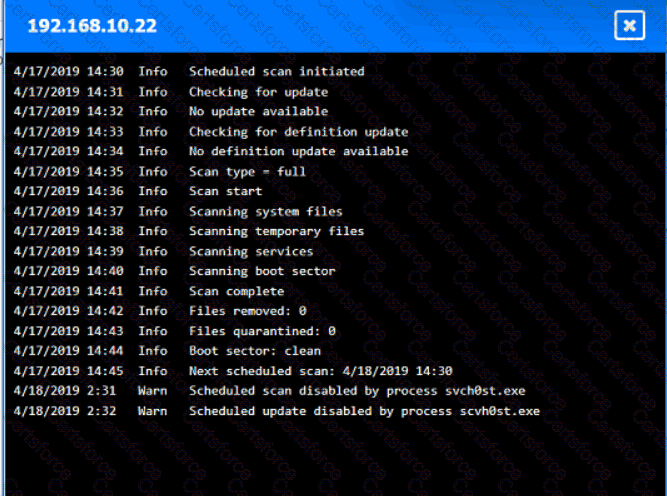
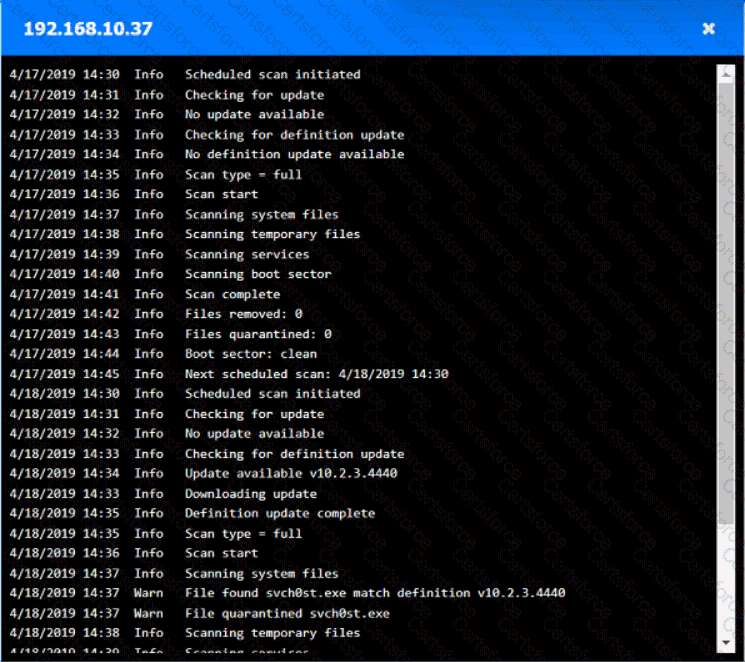
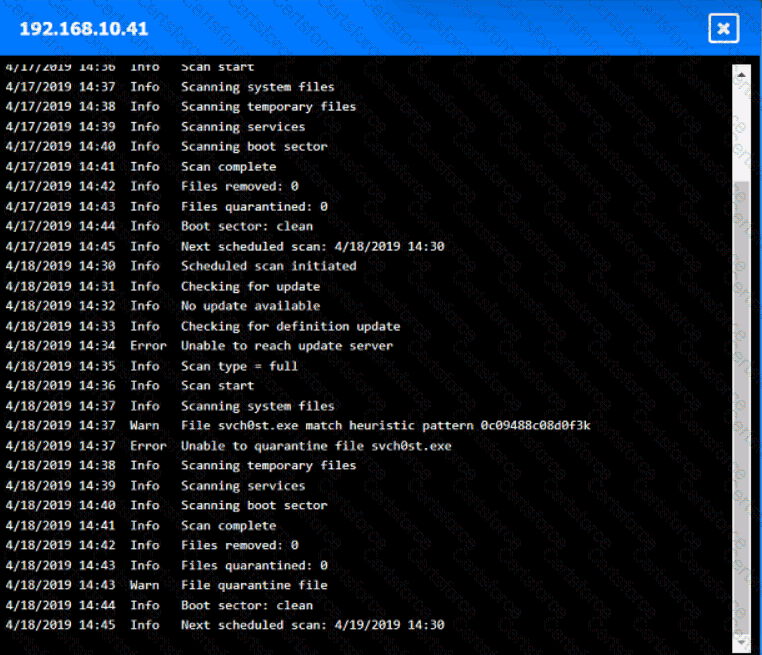
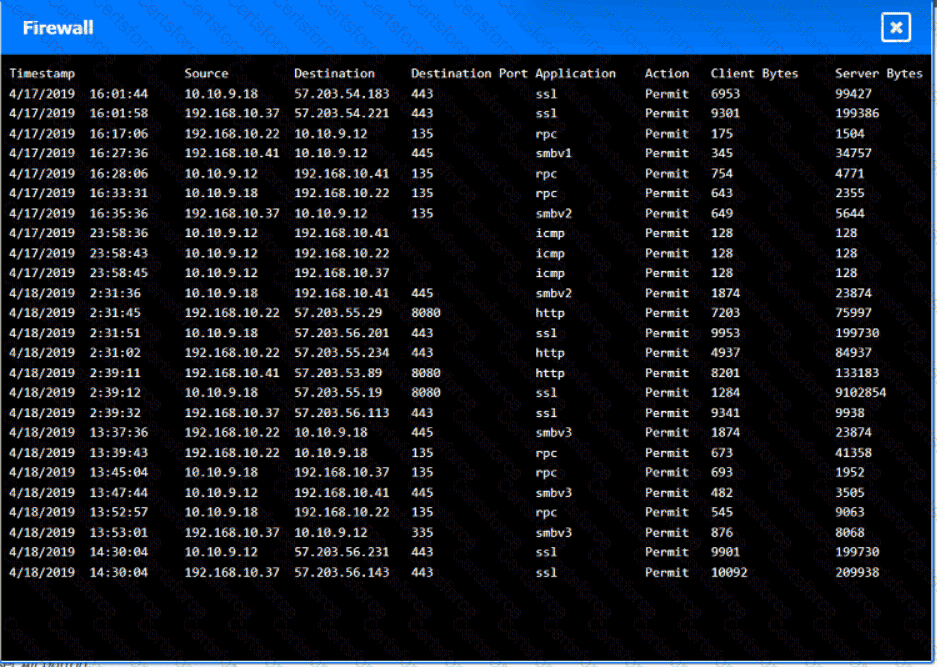
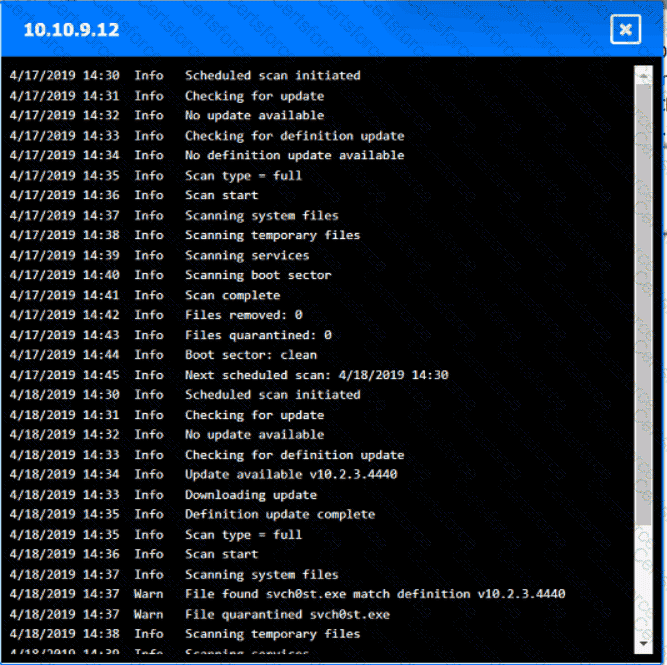
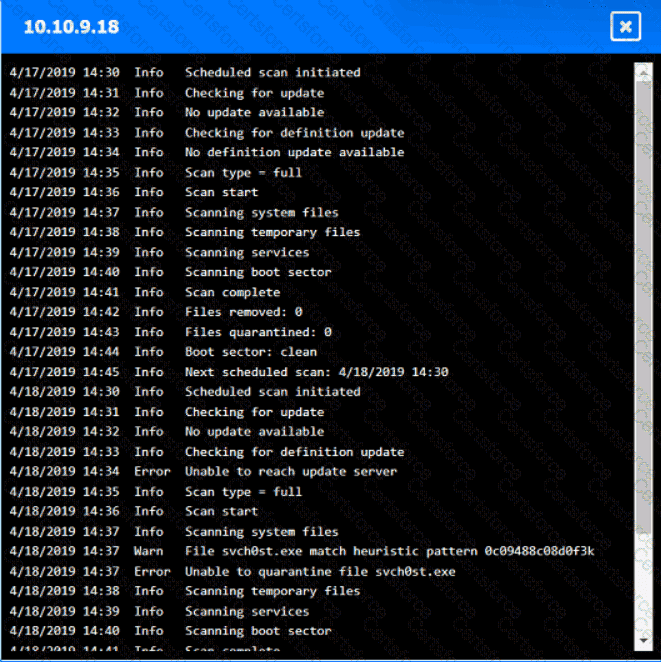
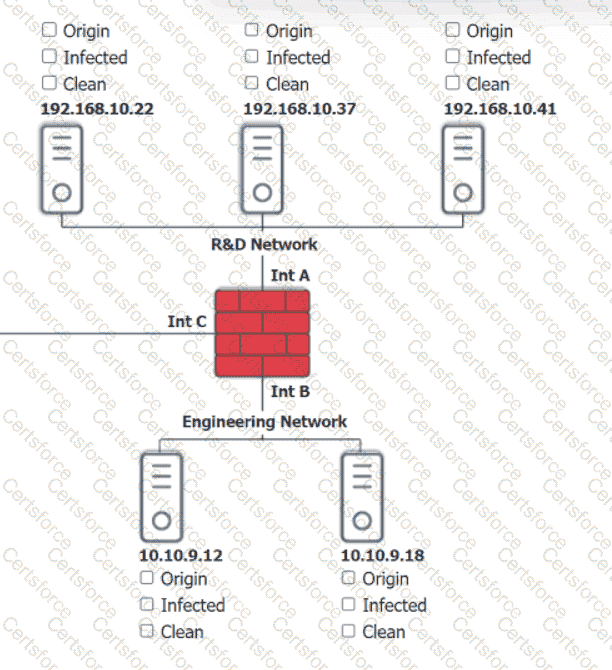
You are security administrator investigating a potential infection on a network.
Click on each host and firewall. Review all logs to determine which host originated the Infecton and then deny each remaining hosts clean or infected.
Which of the following would most likely be used by attackers to perform credential harvesting?
Several customers want an organization to verify its security controls are operating effectively and have requested an independent opinion. Which of the following is the most efficient way to address these requests?
Which of the following best explains the use of a policy engine in a Zero Trust environment?
A security manager is implementing MFA and patch management. Which of the following would best describe the control type and category? (Select two).
A company wants to reduce the time and expense associated with code deployment. Which of the following technologies should the company utilize?
The Chief Information Security Officer gives the security community the opportunity to report vulnerabilities on the organization’s public-facing assets. Which of the following does this scenario best describe?
Which of the following vulnerabilities is exploited when an attacker overwrites a register with a malicious address?
Which of the following is a benefit of vendor diversity?
Which of the following is a benefit of launching a bug bounty program? (Select two)
An IT security team is concerned about the confidentiality of documents left unattended in MFPs. Which of the following should the security team do to mitigate the situation?
An administrator is estimating the cost associated with an attack that could result in the replacement of a physical server. Which of the following processes is the administrator performing?
An accounting clerk sent money to an attacker ' s bank account after receiving fraudulent instructions over the phone to use a new account. Which of the following would most likely prevent this activity in the future?
Which of the following allows an exploit to go undetected by the operating system?