An organization implemented cloud-managed IP cameras to monitor building entry points and sensitive areas. The service provider enables direct TCP/IP connection to stream live video footage from each camera. The organization wants to ensure this stream is encrypted and authenticated. Which of the following protocols should be implemented to best meet this objective?
A security team must help secure a company site after attackers defaced it. The site must be available to a wide range of countries over a secure protocol, but access from known malicious networks should be blocked. Which of the following will best secure the site?
A company wants to get alerts when others are researching and doing reconnaissance on the company One approach would be to host a part of the Infrastructure online with known vulnerabilities that would appear to be company assets. Which of the following describes this approach?
Which of the following threat actors would most likely target an organization by using a logic bomb within an internally-developed application?
Which of the following most securely protects data at rest?
Which of the following describes when a user installs an unauthorized application by bypassing the authorized application store and installing a binary file?
An organization is leveraging a VPN between its headquarters and a branch location. Which of the following is the VPN protecting?
Which of the following types of identification methods can be performed on a deployed application during runtime?
Which of the following describes the maximum allowance of accepted risk?
A security analyst is reviewing alerts in the SIEM related to potential malicious network traffic coming from an employee’s corporate laptop. The security analyst has determined that additional data about the executable running on the machine is necessary to continue the investigation. Which of the following logs should the analyst use as a data source?
Which of the following should be used to ensure an attacker is unable to read the contents of a mobile device ' s drive if the device is lost?
A bank set up a new server that contains customers ' Pll. Which of the following should the bank use to make sure the sensitive data is not modified?
An organization is building a new backup data center with cost-benefit as the primary requirement and RTO and RPO values around two days. Which of the following types of sites is the best for this scenario?
A security administrator recently reset local passwords and the following values were recorded in the system:
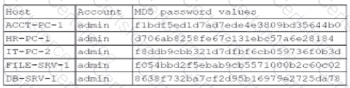
Which of the following in the security administrator most likely protecting against?
A software developer released a new application and is distributing application files via the developer’s website. Which of the following should the developer post on the website to allow users to verify the integrity of the downloaded files?