Which of the following is a primary driver behind the creation and prloritteation of new strategic Initiatives established by an organization?
Which of the following documents would provide an internal auditor with information on the length of time to maintain documents after the completion of an engagement?
During an internal audit engagement, it was found that several vendors were on a government sanctions list and must no longer be traded with. Which of the following would most effectively mitigate the risk of noncompliance with sanctions lists that are updated regularly?
A new clerk in the managerial accounting department applied the high-low method and computed the difference between the high and low levels of maintenance costs. Which type of maintenance costs did the clerk determine?
Which of the following bring-your-own-device (BYOD) practices is likely to increase the risk of Infringement on local regulations, such as copyright or privacy laws?
The internal audit activity has identified accounting errors that resulted in the organization overstating its net income for the fiscal year. Which of the following is the most likely cause of this overstatement?
An internal auditor discovered that the organization was not in full compliance with a regulatory labeling requirement for one of its products. The responsible manager indicated that the current product labeling has been in use for several years without any problems. If discovered, this regulatory breach could result in significant fines for the organization. What should be the chief audit executive's next course of action?
Which of the following is a characteristic of big data?
Which of the following forms of compensation best indicates that an organization’s cost-saving objectives have been targeted?
According to 11A guidance on IT, which of the following spreadsheets is most likely to be considered a high-risk user-developed application?
Which of the following best describes owner's equity?
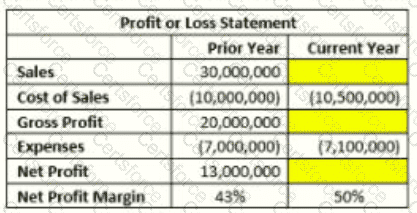
The manager of the sales department wants to Increase the organization's net profit margin by 7% (from 43% in the prior year to 50% in the current year). Given the information provided in the table below, what would be the targeted sales amount for the current year?
Which of the following IT-related activities is most commonly performed by the second line of defense?
Which of the following bring-your-own-device (BYOD) practices is likely to increase the risk of infringement on local regulations, such as copyright or privacy laws?
An organization discovered fraudulent activity involving the employee time-tracking system. One employee regularly docked in and clocked out her co-worker friends on their days off, inflating their reported work hours and increasing their wages. Which of the following physical authentication devices would be most effective at disabling this fraudulent scheme?