An engineer needs to back up the firewall configuration. Now he wants to use a command to view all the current configurations of the firewall. May I ask the command he uses is ____[fill in the blank]*
IPS signatures describe the characteristics of attack behaviors on the network. The firewall detects and defends against attacks by comparing data flows with IPS signatures.
Which of the following statements is incorrect about information transmission through the heartbeat link between two firewalls that work in hot standby mode?
When IPSec VPN uses tunnel mode to encapsulate packets, which of the following is not within the encryption scope of the ESP security protocol?
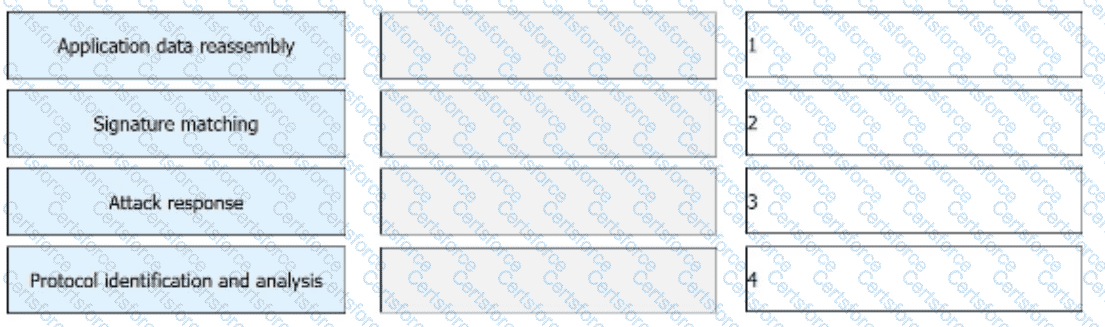
The IPS detects and analyzes all packets passing through a device and determines whether to permit or block the packets in real time based on the comprehensive detection mechanism. Sort the following steps into the correct order based on the basic implementation mechanism of the IPS.
As shown in the figure, the administrator needs to test the network quality of the 20.0.0/24 CIDR block to the 40.0.0/24 CIDR block on Device B, and the device needs to send large packets for a long time to test the network connectivity and stability.

Drag the phases of the cybersecurity emergency response on the left into the box on the right, and arrange them from top to bottom in the order of execution. 1. Inhibition stage, 2. recovery phase, 3. Detection stage, 4. eradication phase[fill in the blank]*
A three-way handshake is required to establish a TCP connection, and a four-way handshake is required to end a TCP connection.
In most cases, a user applies for a local certificate from a CA, and the CA approves the application and issues the certificate to the user.
Using the ___ method of the Web proxy, the virtual gateway will encrypt the real URL that the user wants to access, and can adapt to different terminal types.[fill in the blank]*