Protocol identification and analysis
Application data reassembly
Signature matching
Attack response
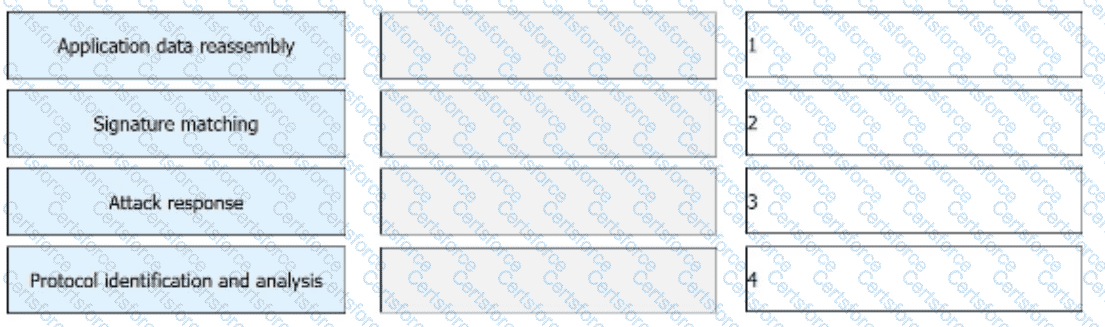
The correct IPS processing order starts with protocol identification and analysis . Before an IPS can judge whether traffic is malicious, it must first determine what protocol is being used and analyze the packet structure according to the expected protocol behavior. This helps the device understand whether the traffic is HTTP, FTP, SMTP, DNS, or another protocol and prepares it for deeper inspection.
After that, the IPS performs application data reassembly . Many attacks are not visible in a single packet, so the IPS must reconstruct fragmented or segmented traffic into complete application data. This allows the device to inspect the real payload content rather than isolated packet pieces.
Once the data is reassembled, the IPS performs signature matching . At this stage, the traffic content and behavior are compared with known attack signatures, protocol anomalies, and detection rules to determine whether the traffic matches a malicious pattern such as injection, buffer overflow, or directory traversal.
Finally, the IPS performs the attack response . Based on the detection result, it may permit, block, reset, alarm, or log the traffic. Therefore, the correct order is D → A → B → C .
Submit