Which of the following NAT technologies can implement a public network address to provide source address translation for multiple private network addresses ( )*
When forwarding a TCP, UDP, or ICMP packet, the firewall needs to query the session table in order to determine the connection to which the packet belongs and take corresponding measures.
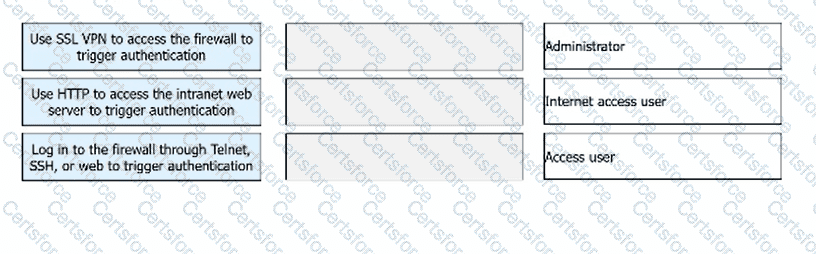
Match the following user categories and authentication modes.
The shard cache technology will wait for the arrival of the first shard packet, and then reassemble and decrypt all the packets, and then do subsequent processing by the device to ensure that the session can proceed normally in some application scenarios.
Huawei Firewall only supports the inter-domain persistent connection function for TCP packets.
Compared with the software architecture of C/S, B/S does not need to install a browser, and users are more flexible and convenient to use.
Which of the following types of malicious code on your computer includes?
In the authentication policy of the firewall, _____ allows the user to not need to enter the user name and password, but can obtain the corresponding relationship between the user and the IP, so as to carry out policy management based on the user[fill in the blank]*
The following description of the intrusion fire protection system IPS, which is correct?
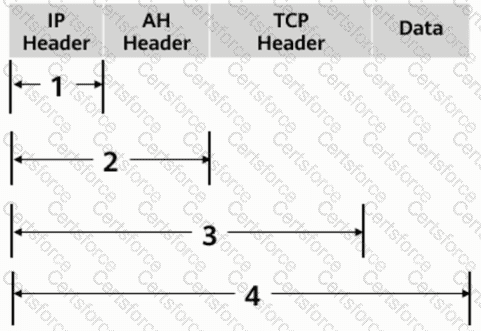
As shown in the figure, what is the range of the AH protocol authentication range in transmission mode?