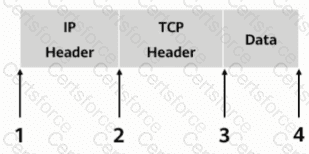
As shown, in transmission mode, which of the following locations should the AH header be inserted in?
Which of the following problems cannot be solved using PKI?
The keys used by the IPSec encryption and authentication algorithms can be configured manually or dynamically negotiated via the ____ protocol. (abbreviation, all uppercase).
Which of the following is the numbering range of Layer 2 ACLs?
Data monitoring can be divided into two types: active analysis and passive acquisition.
What is the protocol number of the GRE protocol?
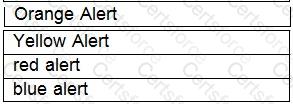
Drag the warning level of the network security emergency response on the left into the box on the right, and arrange it from top to bottom in order of severity.[fill in the blank]*
Which layer of data packets does a packet filtering firewall check?
Which layer of the protocol stack does SSL provide end-to-end encrypted transmission services?
On a firewall, security policies with the permit action do not need to be configured for traffic between users in the same zone.