Which of the following attacks can be detected through intrusion prevention?
____- The goal is to provide a rapid, composed and effective response in emergency situations, thereby enhancing the ability of the business to recover immediately from a disruptive event.[fill in the blank]*
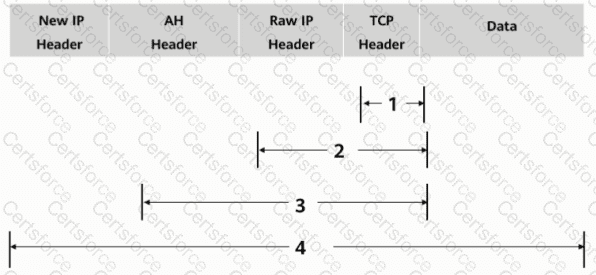
As shown in the figure, what is the authentication range of the AH protocol in tunnel mode?
Which of the following statements is incorrect about DoS attacks?
Under normal circumstances, the Emai1 protocols we often talk about include ____, POP3, and SMTP.[fill in the blank]*
In the PKI certificate revocation process, a user needs to send a signed and encrypted email to the RA to apply for certificate revocation.
Database operation records can be used as ___ evidence to backtrack security events.[fill in the blank]*
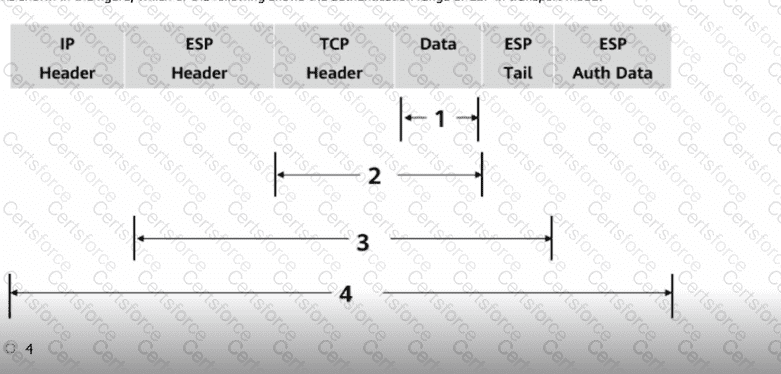
As shown in the figure, which of the following shows the authentication range of ESP in transport mode?
Regarding the characteristics of the routing table, which of the following items is described correctly
As shown in the figure, which of the following shows the authentication range of ESP in transport mode?