Exhibit.
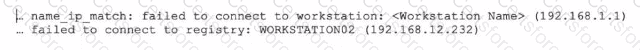
Refer to the exhibit, which shows two entries that were generated in the FSSO collector agent logs.
What three conclusions can you draw from these log entries? {Choose three.)
Which authentication option can you not configure under config user radius on FortiOS?
What are two reasons you might see iprope_in_check() check failed, drop when using the debug flow? (Choose two.)
Refer to the exhibit, which shows the output of get router info bgp summary.
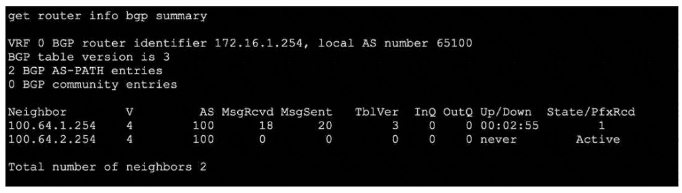
Which two statements are true? (Choose two.)
Which statement about IKEv2 is true?
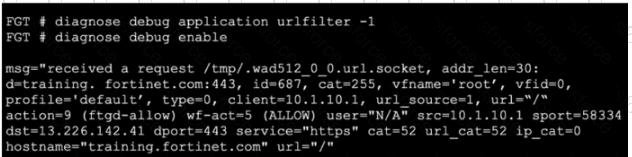
Refer to the exhibit.
The exhibit shows the output from using the command diagnose debug application samld -1 to diagnose a SAML connection.

Based on this output, what can you conclude?
What is the correct order of the IKEv2 request-and-response protocol?
Refer to the exhibit, which shows the output of a real-time debug. Which statement about this output is true? (Choose one answer)
Refer to the exhibit, which shows the output of a diagnose command.
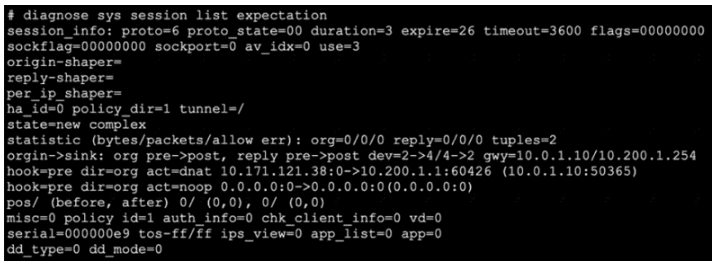
What two conclusions can you draw from the output shown in the exhibit? (Choose two answers)