Task 5
You need to ensure that content on Microsoft SharePoint Online sites can be shared only with new and existing guest users.
Task 8
You need to prevent guest users from calling your company ' s Teams users.
You need to implement the planned changes for the marketing department.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
You need to resolve the issue reported by the project management department users.
What should you do?
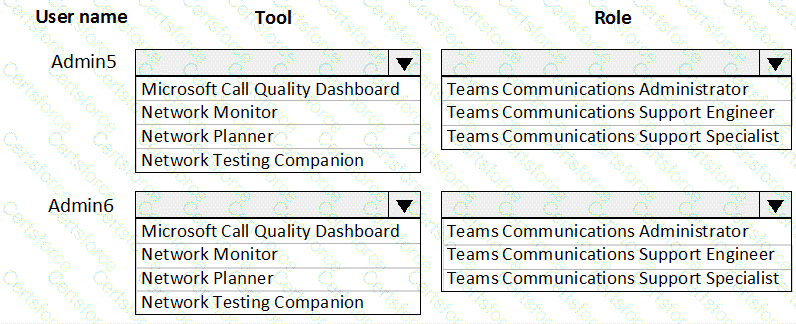
You need to recommend a solution to perform the network validation tasks for the platform upgrade.
Which tool and role should you recommend for each user? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
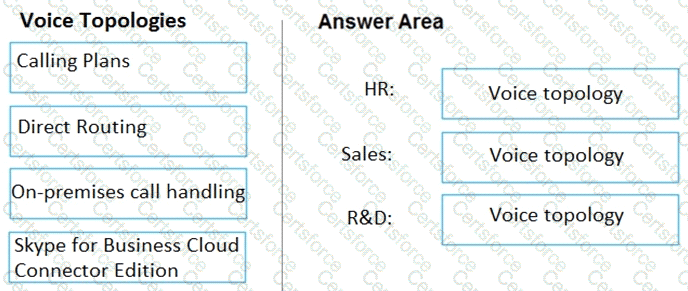
You need to recommend a voice topology for the departments. The topology must meet the calling requirements and the security requirements.
What should you recommend for each department? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 subscription that contains a user named Used.
User1 experiences audio issues while sharing his screen during Microsoft Teams meetings.
You need to investigate whether the headset of User1 causes the issues.
Which report should you use?
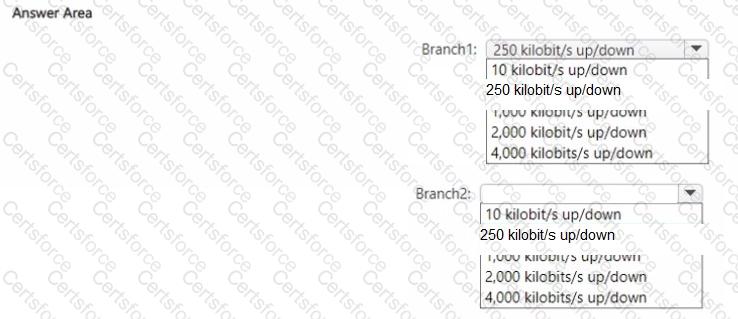
Your company has two branch offices named Branch1 and Branch2. The company uses Teams.
You plan to deploy Teams to the branch offices. The solution must meet the following requirements:
• Users in Branch1 must use only audio and video for meetings.
• Users in Branch2 must be able to enable Together Mode for meetings.
• Network bandwidth costs must be minimized.
What is the minimum bandwidth required for each branch office? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to configure the user accounts of the sales department users to meet the security requirements.
What should you do for each user?
You need to configure the environment to meet the security requirements for the R & D group.
What should you do first?