An administrator needs to install multiple Prism Central instances on a single Prism Element management cluster.
Which statement is valid?
An administrator needs to enable software data-at-rest encryption on a 2-node ROBO cluster. The organization requires that encryption keys are stored on-premises outside of the cluster. Which KMS type should the administrator configure?
Refer to Exhibit:
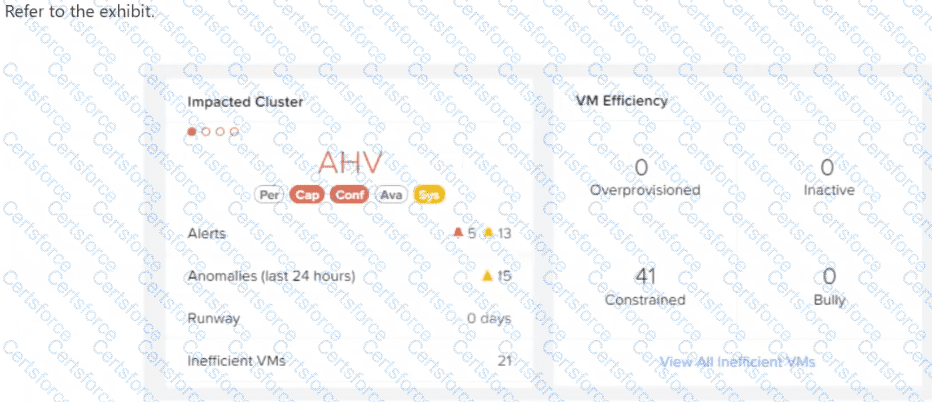
After logging into Prism Central, an administrator observes that there are a large number of constrained VMs.
What does this indicate about those VMs?
An administrator needs to adjust the settings of an existing virtual machine. Which parameter is restricted from modification once the VM has been created?
An administrator has 16 hosts in a cluster, including four undersized older hosts that needs to be removed from the cluster. Unfortunately new servers will take more than six months to be procured.
What policy should be defined within Prism Central to prevent five mission critical VMs from ever running on the older hosts?
An administrator detects suspicious outbound connections from a single VM that hosts a web tier component.
The incident response requirement is to immediately quarantine the VM so it cannot communicate with any other workload, but still allow connectivity from a designated forensic tooling group so investigators can collect evidence.
The organization uses categories for policy scope and wants a change that can be applied quickly during an incident without redesigning existing policies.
Which action best meets the requirement?
An administrator is trying to migrate a VM to a new container. The Migration of vDisks stalls.
What could be the cause of this?
An administrator needs to ensure that if a host remains in a disconnected status for 40 seconds, VMs running on a host are automatically restarted.
What method should the administrator use to ensure root file system corruption has not occurred and that the root file system of a host isn ' t in a read-only state?
A new naming-convention policy for storage containers requires VM placement to follow the updated naming rules. Which action can be performed to comply with the policy?
An administrator supports multiple AHV clusters under Prism Central and uses Intelligent Operations playbooks for remediation.
The organization recently standardized alert policies, but the alert policy names and IDs change between environments due to automated deployments and periodic updates.
The requirement is to trigger a remediation playbook for any alert that matches a defined performance pattern (for example, impact type and severity plus a keyword pattern), regardless of which specific alert policy generated it, while avoiding unrelated non-performance alerts.
Which playbook trigger best meets the requirement?