You are configuring FortiAuthenticator to integrate with FSSO for user identification. To enable FortiAuthenticator to extract user information from syslog messages and inject it into FSSO, you have configured syslog matching rules.
What is the role of syslog matching rules in the process of injecting user information into FSSO?
What is the expected behavior when enabling auto TX power control on a FortiAP interface?
Refer to the exhibits.
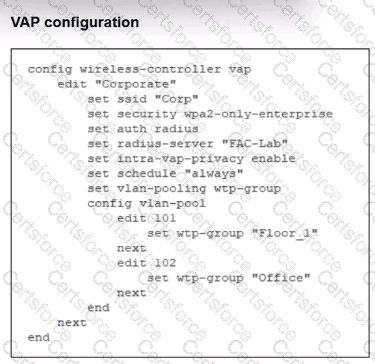
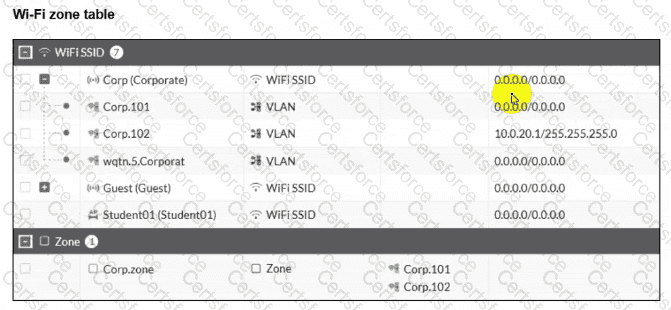
The exhibits show the VAP configuration. Wi-Fi SSIDs. and zone table.
Which two statements describe how FortiGate handles VLAN assignment for wireless clients? (Choose two.)
Why is the suppression of rogue APs becoming more difficult with the introduction of new wireless security standards, such as 802.11w?