A business is hiring a remote employee and must provide the employee with graphical interface access to the in-house Linux servers. Which of the following should the business use for this process?
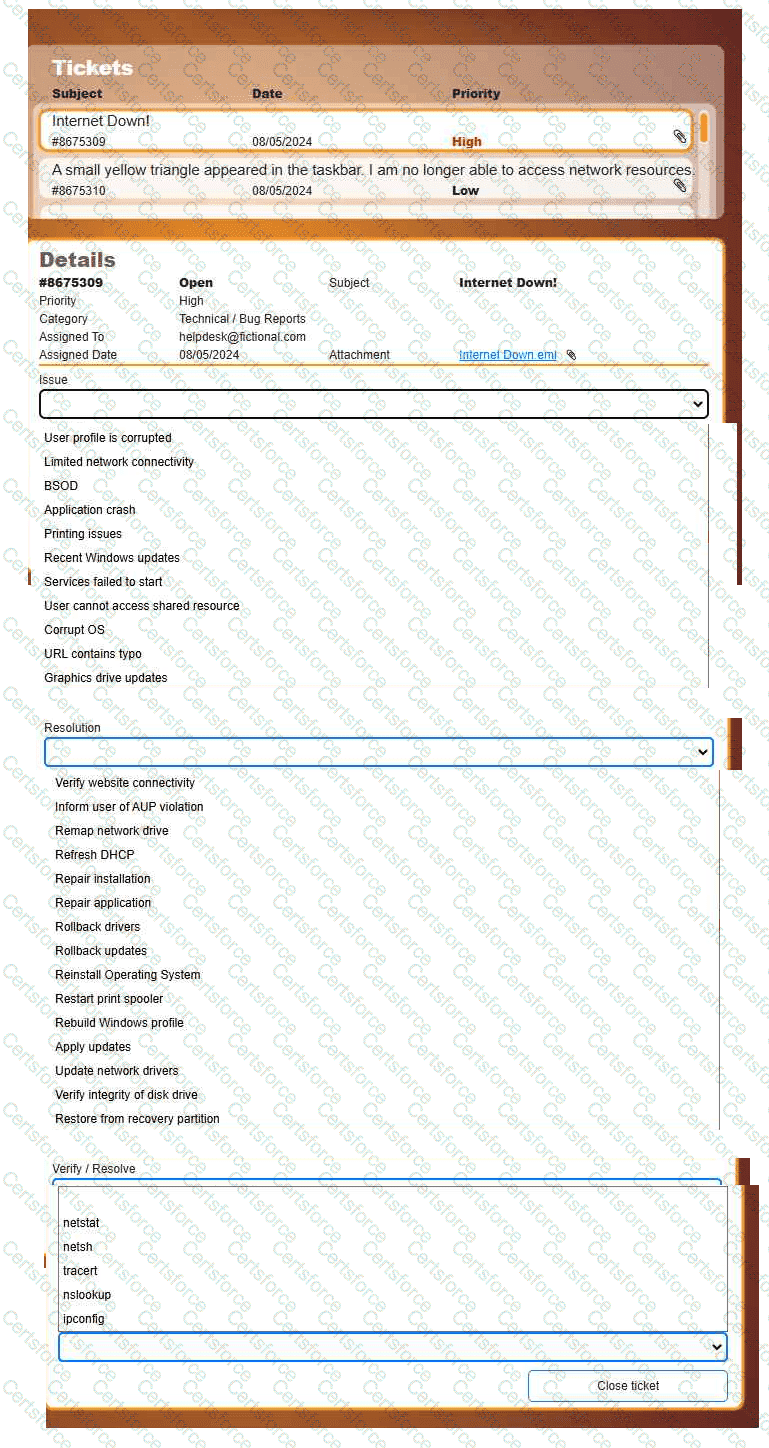
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
A technician inspects the following workstation configuration:
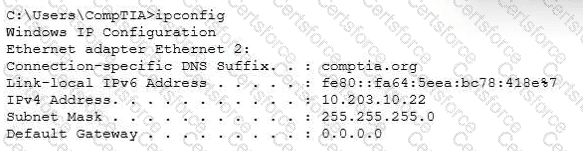
The workstation is unable to open any external websites. The browser displays an error message that says that the site cannot be reached.
A technician needs to configure laptops so that only administrators can enable virtualization technology if needed. Which of the following should the technician configure?
Users are reporting that an unsecured network is broadcasting with the same name as the normal wireless network. They are able to access the internet but cannot connect to the file share servers. Which of the following best describes this issue?
An IT technician must install a new software application across Linux, macOS, and Windows systems within an organization. The installation files are stored on the intranet. Which of the following approaches should the technician take to ensure proper installation?
A company would like to deploy baseline images to new computers as they are started up on the network. Which of the following boot processes should the company use for this task?
Which of the following filesystem types does the Linux OS use?
Which of the following file types would a desktop support technician most likely use to automate tasks for a Windows user log-in?
A technician wears a wrist strap while replacing RAM. Which of the following describes the purpose of the wrist strap during this task?