What is a characteristic of a secure cloud architecture model?
Which three tools are used for ongoing monitoring and maintenance of a voice and video environment? (Choose three.)
An engineer must redesign the QoS strategy for Company XYZ The current network is experiencing many dropped packets due to oversubscription of the guaranteed bandwidth allocated by the service provider Company XYZ wants a design with a QoS strategy that controls the traffic flow leaving the Edge router to minimize packet drops Which QoS technique can be recommended as a solution?
Most security monitoring systems use a signature-based approach to detect threats. In which two instances are systems based on Network Behavior Anomaly Detection better than signature-based systems when it comes to detecting security threat vectors? (Choose two.)
A centralized control plane generally means one or more controllers gather the reachability and topology information from each switching device and calculate some part of the forwarding information at some place. How can a centralized control plane be defined or described?
A large enterprise cloud design team is evaluating different cloud consumption models What is an example of typical PaaS limitations or concerns that should be considered during service design?
The controller has a global view of the network, and it can easily ensure that the network is in a consistent and optimal configuration Which two statements describe a centralized SDN control path? (Choose two.)
The PaaS model provides customers with a virtualized application development platform without the need for them to furnish hardware or system administration using in-house resources All necessary infrastructure components and application development services are provided and managed by the cloud service provider. Which limitation should be considered when selecting PaaS model?
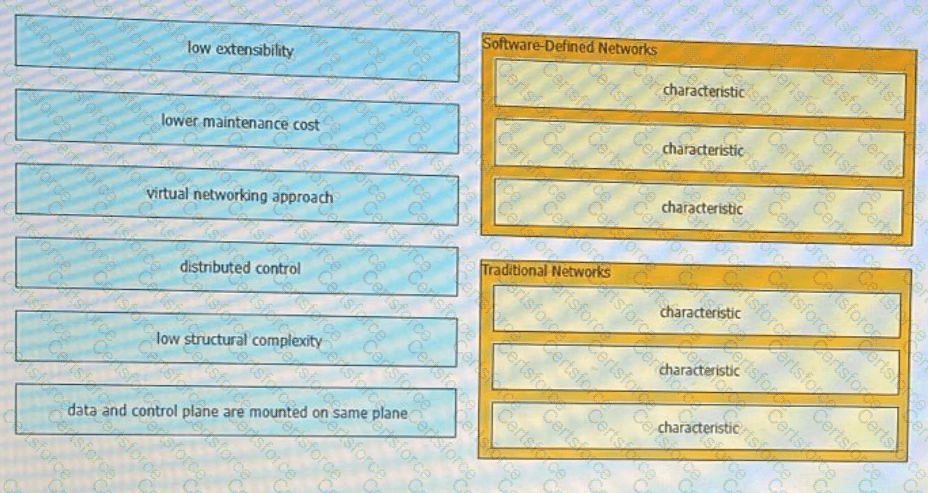
Software-defined network and traditional networks might appear the same to the end-user, but behind the scenes, each has unique sets of characteristics. Drag and drop these characteristic found on the left to the corresponding category on the right in no particular order?
An organization is looking to perform a major overhaul on their data center storage infrastructure with a focus on high availability and fault tolerance Which approach will accomplish this?