An administrator needs to configure Cisco ESA to ensure that emails are sent and authorized by th e owner of the domain. Which two steps must be performed to accomplish this task? (Choose two.)
The company security policy requires that the finance department have an easy way to apply encryption to their outbound messages that contain sensitive data Users must be able to flag the messages that require encryption versus a Cisco Secure Email Gateway appliance scanning all messages and automatically encrypting via detection Which action enables this capability?
Drag and drop the graymail descriptions from the left onto the verdict categories they belong to on the right.

Refer to the exhibit.
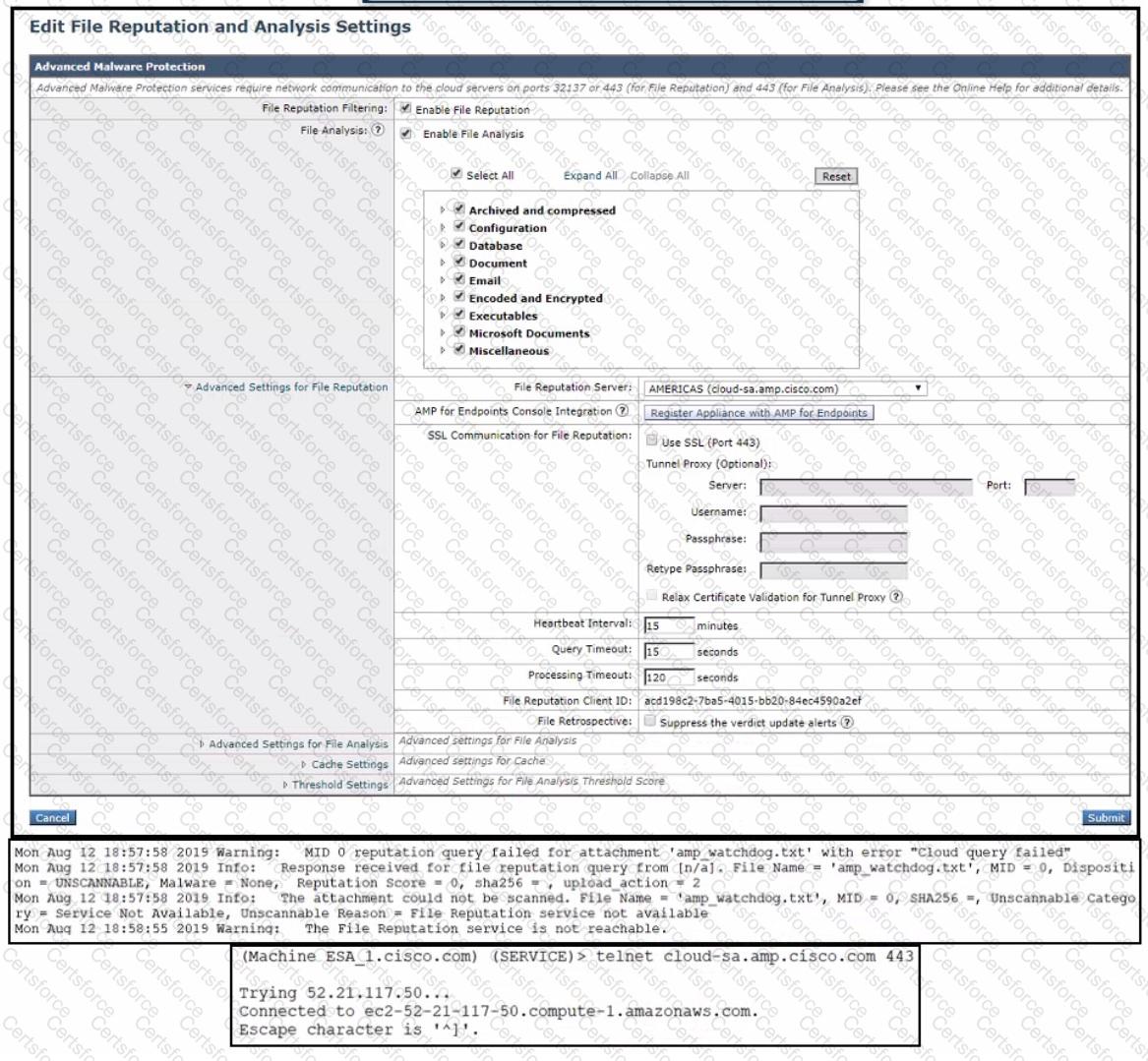
An administrator has configured File Reputation and File Analysis on the Cisco Secure Email Gateway appliance however it does not function as expected What must be configured on the appliance for this to function?
To comply with a recent audit, an engineer must configure anti-virus message handling options on the incoming mail policies to attach warnings to the subject of an email.
What should be configured to meet this requirement for known viral emails?
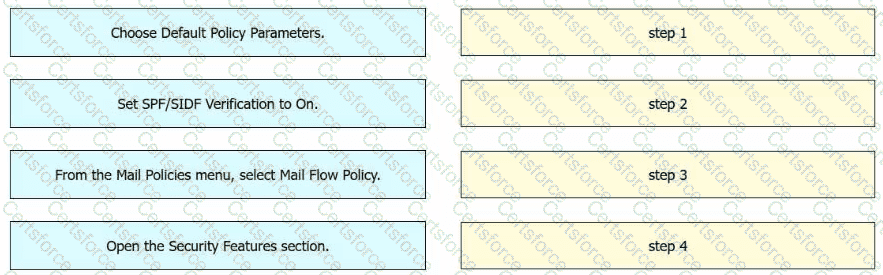
Drag and drop the actions from the left into sequence on the right to validate the authenticity of email on a Cisco Secure Email Gateway by using DNS records.
Which method enables an engineer to deliver a flagged messag e to a specific virtual gateway address in the most flexible way?
Which type of attack does Bounce Verification fight against?
What must be configured to allow the Cisco ESA to encrypt an email using the Cisco Registered Envelope Service?
Which action is a valid fallback when a client certificate is unavailable during SMTP authentication on Cisco ESA?