An administrator needs to delegate the management of security policies to a dedicated SecOps team. To enforce the principle of least privilege, the administrator assigns the predefined Flow Policy Author role to a user on the team. The user confirms they can create, monitor, and enforce security policies. However, when attempting to build a new application security policy for a set of newly deployed VMs, the user reports they are unable to create a new category to group these VMs. The option is not available in the Prism Central UI. Which statement explains this behavior?
Which statement best describes the function of an External Network in Flow Virtual Networking?
Before creating a new Application Security Policy in Prism Central, what prerequisite must exist?
Exhibit:
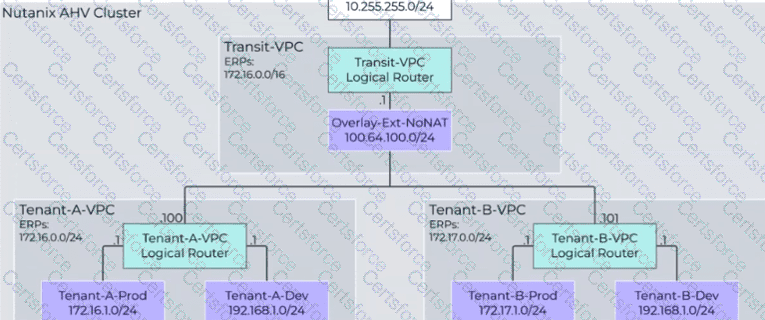
An administrator has just added a new VPC for Tenant-B... However, users are reporting that they are unable to access external resources from VMs created in the Tenant-B-Prod subnet. What should be done to correct the problem?
An administrator has a VPC with a single active gateway node that successfully peers with an external router using a single BGP GW and session. To eliminate a single point of failure, the administrator deploys a second BGP gateway to the VPC. After the second gateway is added and shows a healthy state, the external router still only sees a single BGP session. What is the most likely reason for the second session not being established on the external router?
An administrator creates a VPC named AppVPC1 in Nutanix Cloud Infrastructure (NCI) with separate subnets for the web, app, and database tiers. The database subnet must remain isolated from external networks; however, all tiers need to communicate with each other internally. What should the administrator configure to limit external access to only the web and app subnets?
A junior network operator is assigned two predefined roles in Prism Central... Role A: Prism Viewer Role B: VPC Admin The operator reports being able to successfully create, update, and delete Virtual Private Clouds (VPCs). However, the operator is unable to create a VM into the VPC. How does Prism Central determine the operator's effective permissions?
An administrator plans to upgrade a Nutanix cluster running AHV and Prism Central. The current cluster is on AOS 6.10, and the administrator wants to move to AOS 7.3 while ensuring all components remain compatible. What is the correct upgrade order to minimize downtime and maintain cluster functionality?
An administrator uses Nutanix Flow to secure a three-tier application (Web, App, and Database tiers). After observing the traffic, they find that: The Web tier communicates with the App tier over HTTP (port 80) The App tier communicates with the Database tier over TCP port 1433 The Database tier does not initiate connections The Web tier receives inbound HTTP traffic from the corporate DMZ on port 8080 No other traffic should be allowed What should the administrator do to document and then securely apply these flows in Nutanix Flow?
Which action allows an administrator to reuse a single existing policy in a different scope?