A VDI policy in Flow Network Security allows access to specific resources only when users from the Admins Active Directory group log into a VM. Some administrators report that when they log in to certain VMs, access is blocked (default deny applies), while the same user accounts work correctly when logged on to other VMs. When checking the VM details in Prism Central, operations observes that the expected dynamic category based on the logged-in AD user is not assigned on the affected VMs. What is the most likely reason for this behavior?
Refer to Exhibit:
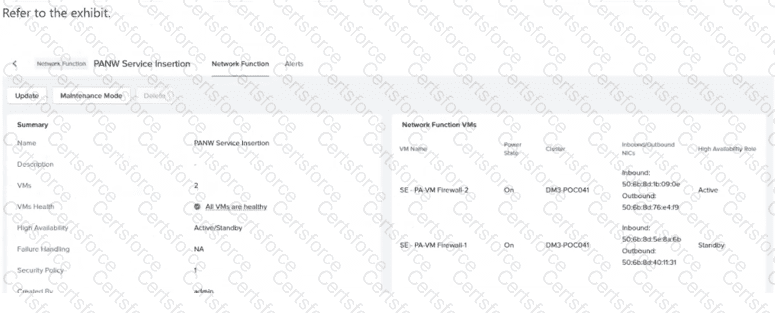
An organization uses an FNS-NG Service Chain to steer application traffic through a pair of third-party firewall Network Function VMs operating in Active/Standby mode. Users suddenly report that all application access is blocked. The administrator reviews Prism Central - > Network & Security - > Network Functions, where the summary shown in the exhibit is displayed. Additional information: Alert: "Network Function 'PANW Service Insertion' virtual NIC pair(s) are unhealthy." Both firewall VMs are powered on and reachable. The security policy using the service chain has not been changed. Based on the exhibit and findings, what is the most likely cause of the traffic outage?
What must an administrator do before disabling the Network Controller?
When cloning a Flow Network Security policy, what should be verified before enabling Enforce mode?
An administrator needs to make a web server VM, which is inside a private VPC overlay subnet, accessible from the external network. The administrator assigns a Floating IP to the VM, but the service is still unreachable from the outside. What is a likely reason for this failure?
Which two statements are true with respect to Flow Network Security Policies? (Choose two.)
An administrator plans to upgrade the Network Controller in a Flow Virtual Networking deployment. The environment includes multiple AHV clusters managed by Prism Central. Which prerequisite must be verified before upgrading the Network Controller?
An administrator is configuring a Nutanix environment for Flow Network Security Next-Gen. Where should the MTU be set to ensure that Geneve encapsulation overhead is properly accounted for?
Which step is required to prepare an AHV cluster for Flow Network Security Next-Gen?
An administrator is responsible for managing user access to a Nutanix cluster... configure custom user roles... What is the first step in configuring and managing user roles for a Nutanix cluster?