John works as an IT Technician for uCertify Inc. One morning, John receives an e-mail from the company's Manager asking him to provide his logon ID and password, but the company policy restricts users from disclosing their logon IDs and passwords. Which type of possible attack is this?
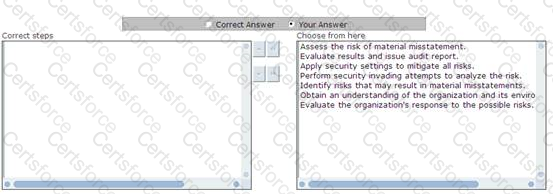
Choose and reorder the appropriate steps that you will take to perform auditing.
Which of the following is a technical measure?
You work as an Information Security Officer for uCertify Inc. You need to create an asset management plan differentiating fixed assets from inventory items. How will you differentiate assets from inventory items?
Which of the following statements about incremental backup are true?
Each correct answer represents a complete solution. Choose two.
Andrew is the CEO of uCertify Inc. He wants to improve the resources and revenue of the company. He uses the PDCA methodology to accomplish the task. Which of the following are the phases of the PDCA methodology?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following statements describes the purpose of information security policy?
You work as an Information Security Manager for uCertify Inc. You are working on communication and organization management. You need to create the documentation on change management.
Which of the following are the main objectives of change management?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following sections come under the ISO/IEC 27002 standard?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following can be protected by the RAID implementation?