Which of the following operations are performed by the Identity Management Process?
Each correct answer represents a complete solution. Choose all that apply.
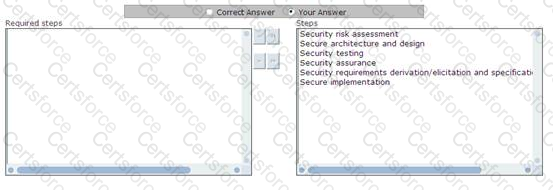
Cigital Risk Management Method was developed by Gary McGraw of Cigital and John Viega of Stonewall Software, and it defines software security risk management process. Choose and re-order the risk management steps that are included in this method.
Which of the following are features of protocol and spectrum analyzers?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following is a process of identifying and documenting project roles, responsibilities, and reporting relationships?
Which of the following is the correct formula of single loss expectancy?
Which of the following types of social engineering attacks is a term that refers to going through someone's trash to find out useful or confidential information?
Which of the following plans provides measures and capabilities for recovering a major application or general support system?
Which of the following states that a user should never be given more privileges than are required to carry out a task?
Which of the following tasks are performed by Information Security Management?
Each correct answer represents a complete solution. Choose all that apply.
You work as an Information Security Manager for uCertify Inc. You are working on a project related to communications and operations management. Which of the following controls of the ISO standard is concerned with operational procedures and responsibilities?