In which of the following sections of the Computer Misuse Act 1990 are amendments made by Part 5 of the Police and Justice Act 2006?
Each correct answer represents a complete solution. Choose all that apply.
Sam works as the Chief Information Security Officer for Blue Well Inc. There are a number of teams for the security purposes. Which of the following are the types of teams of which Sam can be a part of?
Each correct answer represents a complete solution. Choose all that apply.
You are the Network Administrator for a school. You are concerned that end users' might accidentally have access to resources they do not require. What concept should you implement in your network security management to best address this concern?
You work as an Information Security Manager for uCertify Inc. You are working on asset management. You need to classify different information assets used in your organization. Which of the following should be the basis of your classification?
Mark works as a Webmaster for Infonet Inc. He sets up an e-commerce site. He wants to accept online payments through credit cards on this site. He wants the credit card numbers to be encrypted. What will Mark do to accomplish the task?
Which of the following is a technique for a threat which creates changes to the project management plan?
You are the Network Administrator for a school. You are concerned that end users' might accidentally have access to resources they do not require. What concept should you implement in your network security management to best address this concern?
How can you calculate the Annualized Loss Expectancy (ALE) that may occur due to a threat?
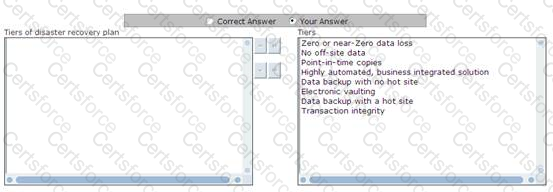
Disaster recovery plan consists of various tiers for identifying the methods of recovering mission-critical computer systems that are necessary to support business continuity. All these tiers provide a simple method to define current service levels and associated risks. Choose and re-order the tiers of disaster recovery plan.
You work as an Information Security Manager for uCertify Inc. You are implementing an asset management strategy. Which of the following should you include in your strategy to make it effective?
Each correct answer represents a complete solution. Choose all that apply.