What are two features of collector agent advanced mode? (Choose two.)
Refer to the exhibit.
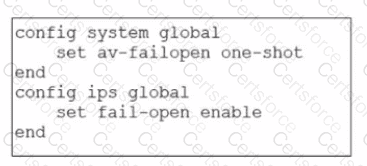
Based on this partial configuration, what are the two possible outcomes when FortiGate enters conserve mode? (Choose two.)
Refer to the exhibits.
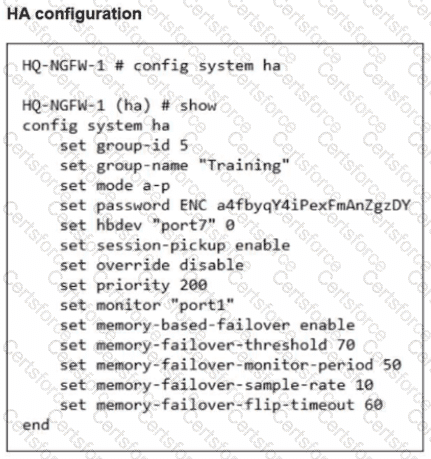
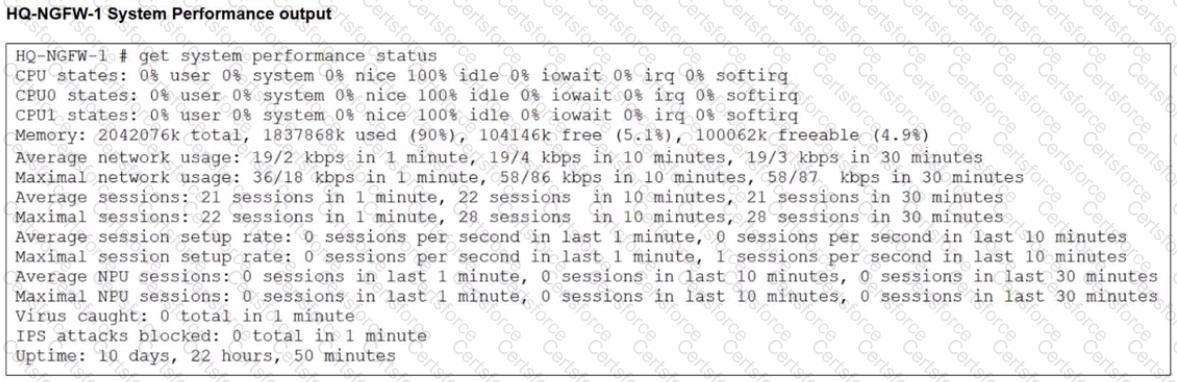
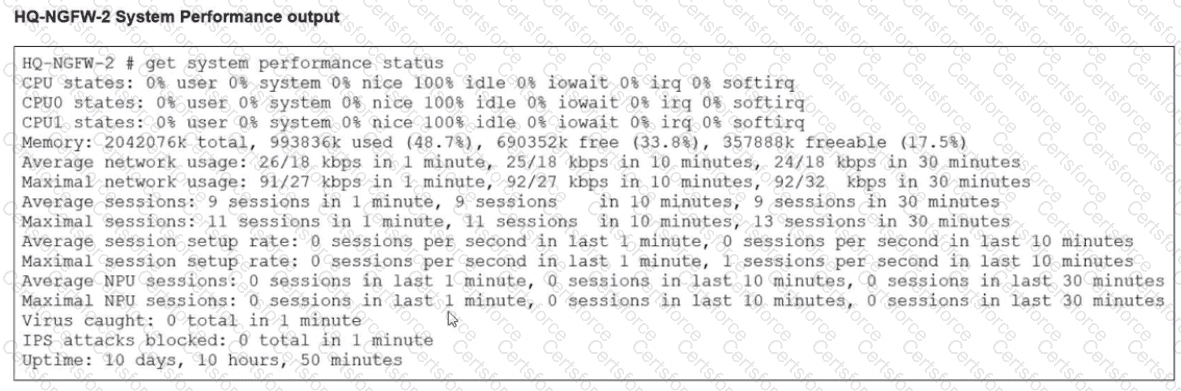
An administrator has observed the performance status outputs on an HA cluster for 55 seconds.
Which FortiGate is the primary?
A network administrator enabled antivirus and selected an SSL inspection profile on a firewall policy. When downloading an EICAR test file through HTTP, FortiGate detects the virus and blocks the file. When downloading the same file through HTTPS, FortiGate does not detect the virus and does not block the file, allowing it to be downloaded. The administrator confirms that the traffic matches the configured firewall policy. What are two reasons for the failed virus detection by FortiGate? (Choose two answers)
There are multiple dialup IPsec VPNs configured in aggressive mode on the HQ FortiGate. The requirement is to connect dial-up users to their respective department VPN tunnels.
Which phase 1 setting you can configure to match the user to the tunnel?
Which two features of IPsec IKEv1 authentication are supported by FortiGate? (Choose two.)
When configuring firewall policies which of the following is true regarding the policy ID? (Choose two.)