A SOC analyst detects multiple instances of powershell.exe being launched with the -ExecutionPolicy Bypass and -NoProfile arguments on a domain controller. The parent process is winrm.exe, and the activity occurs during non-business hours. What should be the analyst’s primary focus?
A multinational corporation with strict regulatory requirements (e.g., GDPR, PCI-DSS) needs a SIEM solution to monitor its global network. Data residency laws in certain regions prohibit transferring logs outside local jurisdictions. The company also requires centralized monitoring with 24/7 SOC operations but has limited in-house SIEM expertise. Which SIEM deployment model is appropriate?
A large financial organization has experienced an increase in sophisticated cyber threats, including zero-day attacks and APTs. Traditional detection relies heavily on signatures and manual intervention, causing delays. The CISO is exploring AI-driven solutions that can automatically analyze large datasets, detect anomalies, and adapt to evolving threats in real time—identifying suspicious activity without predefined signatures and with minimal human oversight. Which key AI technology should the organization focus on?
Rinni, SOC analyst, while monitoring IDS logs detected events shown in the figure below.
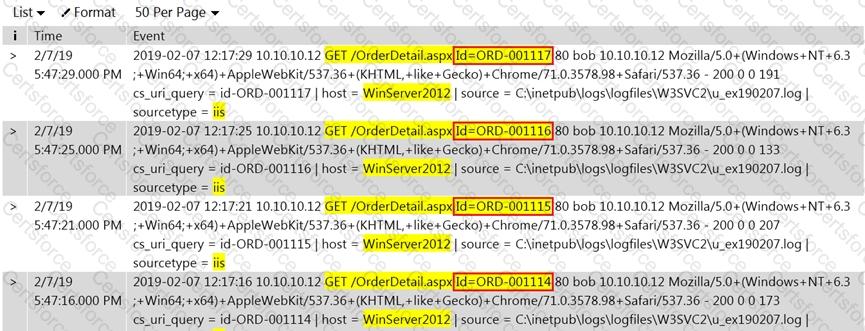
What does this event log indicate?
Which of the following attack can be eradicated by disabling of "allow_url_fopen and allow_url_include" in the php.ini file?
Mike is an incident handler for PNP Infosystems Inc. One day, there was a ticket raised regarding a critical incident and Mike was assigned to handle the incident. During the process of incident handling, at one stage, he has performed incident analysis and validation to check whether the incident is a true incident or a false positive.
Identify the stage in which he is currently in.
Sam, a security analyst with INFOSOL INC., while monitoring and analyzing IIS logs, detected an event matching regex /\\w*((\%27)|(\’))((\%6F)|o|(\%4F))((\%72)|r|(\%52))/ix.
What does this event log indicate?
CyberBank has experienced phishing, insider threats, and attempted data breaches targeting customer financial records. The bank operates across multiple regions and needs a solution offering continuous security monitoring, rapid threat detection, and centralized visibility across all branches. Which solution will provide automated alerting, digital forensics capabilities, and active threat hunting?
Which of the following attack can be eradicated by filtering improper XML syntax?
Mark Reynolds, a SOC analyst at a global financial institution, is working on the eradication phase after detecting phishing attacks targeting employees. To ensure attackers cannot reuse malicious infrastructure, Mark implements a technique that blocks known malicious IP addresses used for sending spam emails at the Domain Name System (DNS) level. Which technique is best suited?