While performing a threat hunt in your environment, you decide to identify rare occurrences of user agent strings over the past 30 days. Which query will highlight those results using CQL?
Refer to the image. Which query will show file execution from a suspicious directory across all hosts?
You have received a detection and want to begin analyzing the triggering file in the process timeline dashboard. Which is required to execute the search?
Refer to the exhibit.
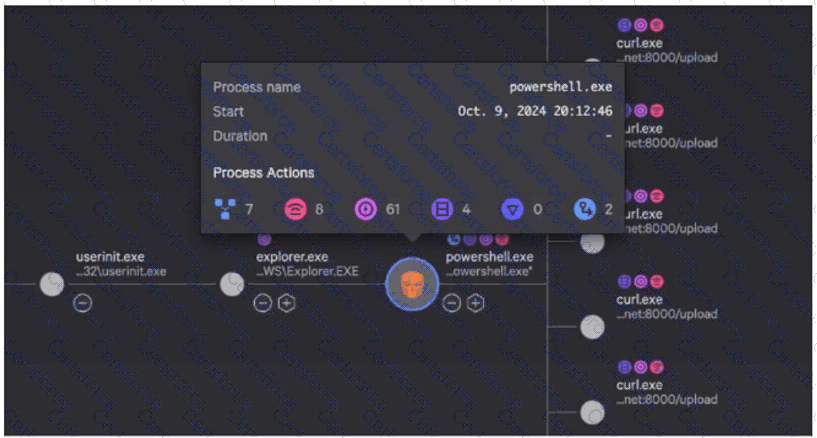
While investigating a process tree, you hover over a malicious powershell.exe process. What is the correct sequence of Process Actions?
Refer to the image.
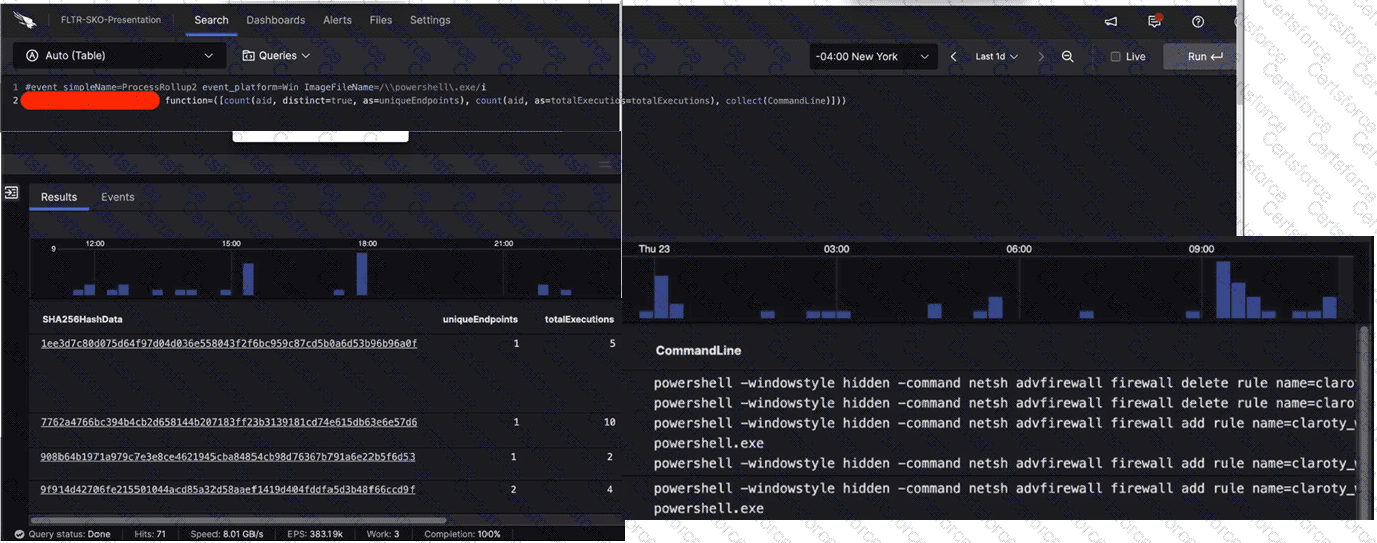
What aggregate function in the CrowdStrike Query Language (CQL) was used to provide the filtered results?
You are investigating an alert for a process that connected to the following suspicious domain: reallysuspiciousdomain[.]com. Which of the Investigate dashboards would provide a list of processes that looked up the specified domain?
An independent investigation team based in Europe asks for the Event Search data to be formatted to Central European Summer Time (CEST). Which parameter within the formatTime() function is required to convert the Unix timestamps?
You've experienced a ransomware infection that has spread throughout the enterprise. What is the first step you would take to determine the source of infection?