A developer has written the following IAM policy to provide access to an Amazon S3 bucket:
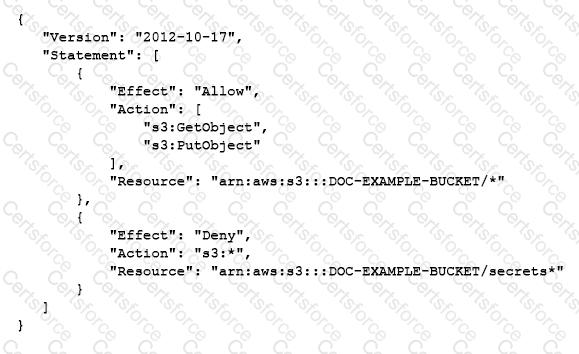
Which access does the policy allow regarding the s3:GetObject and s3:PutObject actions?
A developer is running an application on an Amazon EC2 instance. When the application attempts to read from an Amazon S3 bucket, the request fails. The developer determines that the IAM role associated with the EC2 instance is missing the required Amazon S3 read permissions.
The developer must grant the application access to read from the S3 bucket with the LEAST application disruption .
Which solution will meet this requirement?
A developer is preparing to deploy an AWS CloudFormation stack for an application from a template that includes an IAM user.
The developer needs to configure the application ' s resources to retain the IAM user after successful creation. However, the developer also needs to configure the application to delete the IAM user if the stack rolls back.
A developer needs to deploy an application running on AWS Fargate using Amazon ECS The application has environment variables that must be passed to a container for the application to initialize.
How should the environment variables be passed to the container?
A developer is integrating Amazon ElastiCache in an application. The cache will store data from a database. The cached data must populate real-time dashboards. Which caching strategy will meet these requirements?
A developer is running an application on an Amazon EC2 instance. When the application tries to read an Amazon S3 bucket, the application fails. The developer notices that the associated IAM role is missing the S3 read permission. The developer needs to give the application the ability to read the S3 bucket. Which solution will meet this requirement with the LEAST application disruption?
A developer maintains a serverless application that uses AWS Lambda to process financial transaction files uploaded to an Amazon S3 bucket. A Lambda function is scheduled to run once per hour to process the files.
As file uploads increase, the Lambda function occasionally exceeds the 15-minute execution limit . The developer must handle higher file volumes, reduce processing time, and prevent duplicate file processing .
Which solution will meet these requirements?
A developer is using an AWS account to build an application that stores files in an Amazon S3 bucket. Files must be encrypted at rest by AWS KMS keys. A second AWS account must have access to read files from the bucket.
The developer wants to minimize operational overhead for the application.
Which combination of solutions will meet these requirements? (Select TWO.)
A developer is writing an application for a company. The application will be deployed on Amazon EC2 and will use an Amazon RDS for Microsoft SQL Server database. The company ' s security team requires that database credentials are rotated at least weekly.
How should the developer configure the database credentials for this application?
A developer is creating a new batch application that will run on an Amazon EC2 instance. The application requires read access to an Amazon S3 bucket. The developer needs to follow security best practices to grant S3 read access to the application.
Which solution meets these requirements?
A company runs a critical application on AWS. The application uses credentials to access an Amazon RDS database.
As part of a risk assessment to analyze security vulnerabilities, the company found that database credentials are not frequently rotated. A developer needs to implement a solution that securely stores and rotates the credentials. The solution must not expose the credentials to anyone who should not have access to the credentials.
Which solution will meet these requirements?
An application reads data from an Amazon Aurora global database with clusters in two AWS Regions. Database credentials are stored in AWS Secrets Manager in the primary Region and are rotated regularly.
The application must be able to run in both Regions and remain highly available .
Which combination of actions will meet these requirements? (Select TWO.)
A company has a web application that is hosted on Amazon EC2 instances The EC2 instances are configured to stream logs to Amazon CloudWatch Logs The company needs to receive an Amazon Simple Notification Service (Amazon SNS) notification when the number of application error messages exceeds a defined threshold within a 5-minute period
Which solution will meet these requirements?
A company has an application that runs on Amazon EC2 instances. The application needs to use dynamic feature flags that will be shared with other applications. The application must poll on an interval for new feature flag values. The values must be cached when they are retrieved.
Which solution will meet these requirements in the MOST operationally efficient way?
A developer is receiving HTTP 400: ThrottlingException errors intermittently when calling the Amazon CloudWatch API. When a call fails, no data is retrieved.
What best practice should first be applied to address this issue?