Under what circumstances will TAP generate an email notification alert?
What is the primary function of the People Page in the Threat Protection Workbench and TAP Dashboard?
Which filter category in the TAP Dashboard helps identify threats targeting VIPs or specific geographies?
Heuristic analysis, signature-based detection, and reputation-based methods are all examples of which type of cybersecurity analysis technique?
What does a notification of “Cleared” mean when shown in the header of an individual threat tab?
Which of the following is an item that should be included in an incident report as part of the post-incident debrief?
Exhibit:
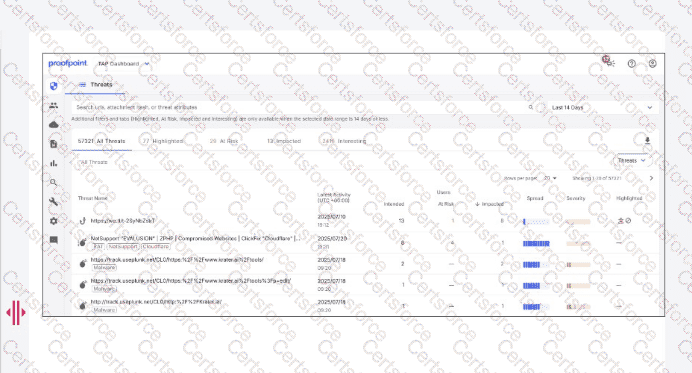
Which column indicates the number of users targeted by a malicious campaign or threat?
An analyst has been tasked with providing a report that can be used to prioritise investigations based on a user's Attack Index score. Which report would be most suitable for this purpose?
As a new analyst, you need to review threat intelligence related to threats in your environment. Which Proofpoint product provides this data?
Which two threat protection capabilities are available as part of Proofpoint’s Targeted Attack Protection (TAP)? (Select two.)