What is the most important aspect of security awareness and training?
What is the primary goal of a risk management process in cybersecurity?
Example of a technical control:
An external entity has tried to gain access to your organization’s IT environment without authorization. This is an example of a(n):
A method for risk analysis that is based on the assignment of a descriptor such as low, medium, or high.
Four main components of Incident Response are:
Exhibit.
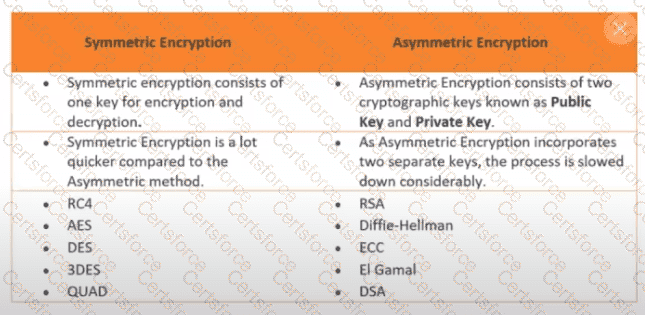
How many keys would be required to support 50 users in an asymmetric cryptography system?
Which of the following is the LEAST secure communications protocol?
Which one of the following controls is NOT particularly effective against the insider threat?
What is the first step in incident response planning?