Refer to the exhibit.
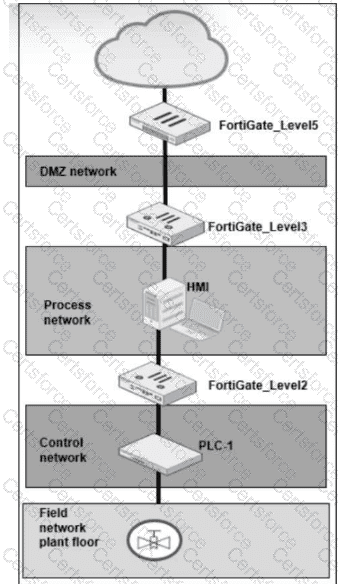
A simplified OT network is shown. You want to optimize the protection of this OT network. Which two controls must you implement? (Choose two answers)
Refer to the exhibit.
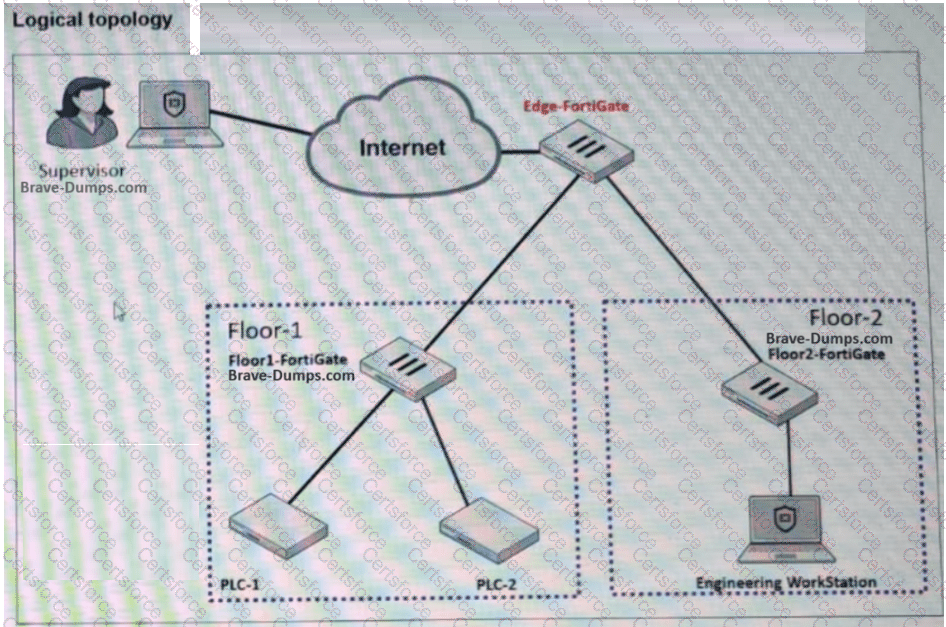
A partial OT network is shown. You want to provide the supervisor with secure remote access. Which two features can you implement on Edge-FortiGate ? (Choose two answers)
How are rogue devices evaluated in FortiNAC? (Choose one answer)
Refer to the exhibit.
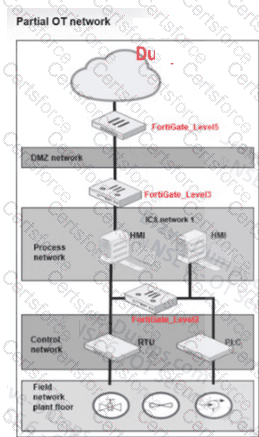
A partial OT network is shown. In this OT network, you must add additional security measures to detect OT protocols and, therefore, increase the traffic visibility. Which security sensor must you implement to detect the OT protocols in this network? (Choose one answer)
Refer to the exhibit.
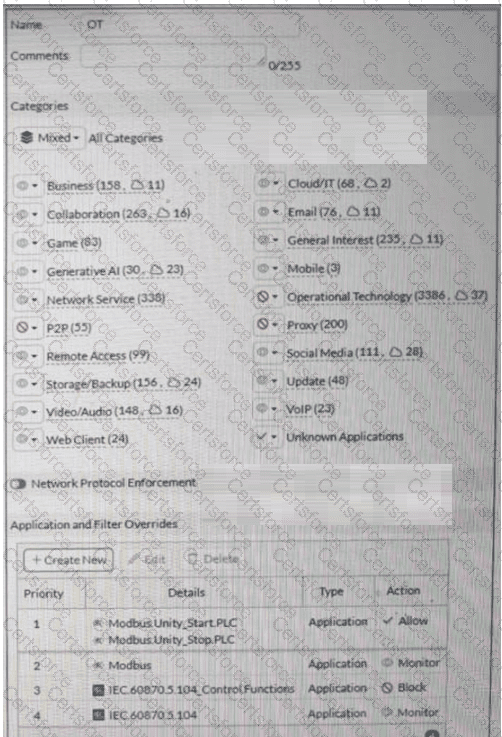
A partial Application Sensor profile is shown. When you apply this profile in a firewall policy, which two statements are correct? (Choose two answers)
Refer to the exhibit.
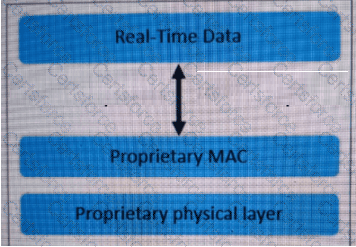
An industrial Ethernet protocol skipping layers 3 to 6 is shown. Which industrial Ethernet protocol is it? (Choose one answer)
Which industrial protocol does not support VLANs? (Choose one answer)
For the installation of your first FortiGate device, you want to minimize the impact in your OT network. Therefore, you deploy it initially as an offline IDS. Which two statements about this deployment are correct? (Choose two answers)
During layer 2 polling , which two pieces of information are gathered by FortiNAC to identify a device? (Choose two answers)
Refer to the exhibit.
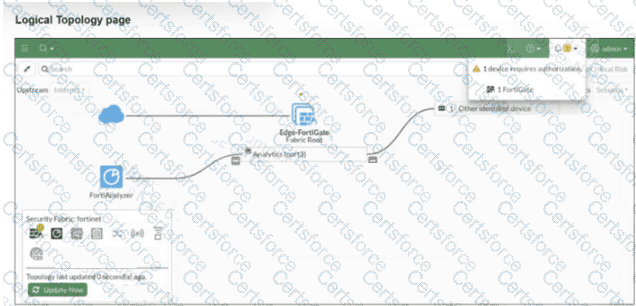
A Logical Topology page of a FortiGate device is shown. Your OT company wants to gain visibility into the network. You decide to implement device detection with the Security Fabric. Based on the exhibit, which statement is correct? (Choose one answer)