What is a characteristic of gain in wireless antenna design?
What defines device sensitivity in a wireless environment?
Which Cisco Ultra-Reliable Wireless Backhaul process enables devices to establish a reliable connection with the next AP along their path before losing connectivity to the current one in a wireless network during roaming?
A network administrator at a marketing company manages a Cisco Catalyst 9800 Series Wireless Controller running Cisco IOS XE 17.x. The WLAN named XYZ-Guest is set up for visitors, and the administrator wants to implement a web authentication (WebAuth) portal using an external server to manage guest access. To ensure seamless and secure guest authentication, the controller must be configured to use an external WebAuth server for the WLAN. The administrator must configure the XYZ-Guest WLAN to use an external WebAuth server with a parameter map named webauth-ext. Which set of Cisco IOS XE commands must be used?
Which process enables seamless Layer 2 handoff in a wireless network during roaming?
What happens when a radio wave bends around objects?
Exhibit:
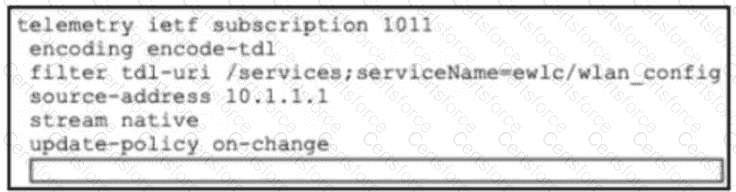
Refer to the exhibit. An organization wants to use Cisco Spaces for location analytics, and an engineer is setting up the Cisco Catalyst 9800 WLC to send location data. The Spaces connector has already been configured and is operational on the WLC. The engineer must now configure the controller to forward telemetry data to the correct Spaces cloud endpoint using TLS to complete the integration. Which CLI command must be added to the box in the code?
Which feature does a high-gain patch antenna impart to a wireless signal?
Refer to the exhibit.]
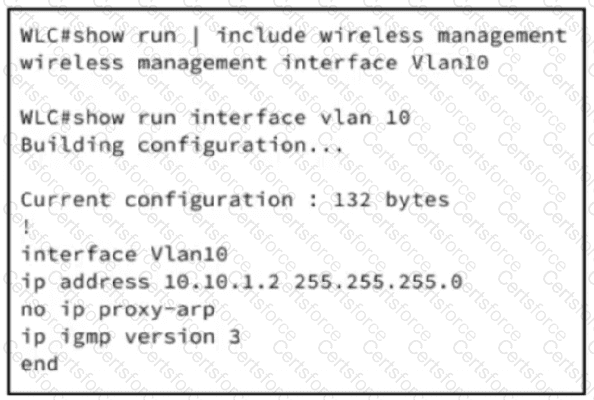
An engineer is setting up a new WLC in a branch office. The IT security policy states that all management access must use encrypted protocols, administrators will connect remotely, and network scans will be run to check for any noncompliant management protocol exposure. Which action must the engineer take to achieve the required management access policy?
What is a benefit of applying TACACS authentication for device access?