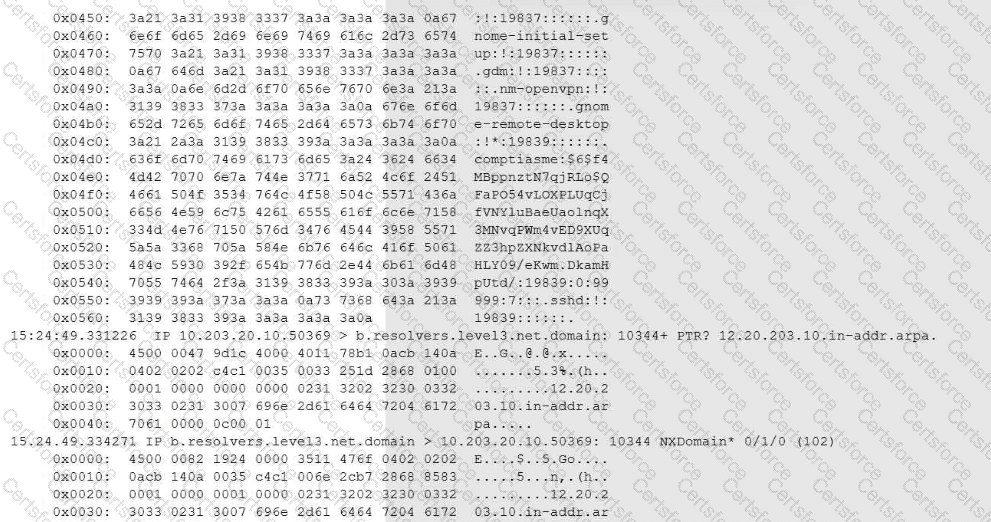
The tcpdump filter (udp and port 53) isolates DNS traffic. In the output, the analyst can see DNS queries/responses, including PTR lookups and NXDomain responses. What makes this suspicious is the context (“unusual volume of traffic”) combined with the appearance of encoded/high-entropy-looking content embedded in the DNS-related data in the capture.
This pattern strongly aligns with DNS tunneling, a technique used to move data (including stolen data) inside DNS queries because DNS (port 53) is widely allowed and often less inspected. In other words, the capture indicates a covert channel over DNS consistent with data exfiltration.
The All-in-One CySA+ CS0-003 guide explicitly describes DNS tunneling as an exfiltration method:
Exact extract (All-in-One Exam Guide):
“Domain Name System (DNS) tunneling, for example, is a method of sending data via encoded DNS queries… Hunters will need to keep an eye out for abnormal DNS queries or unusually high query volumes.”
That maps directly to this scenario:
You were told there is an unusual volume of traffic.
The traffic is DNS (UDP/53).
The output shows encoded/abnormal-looking DNS content, consistent with “sending data via encoded DNS queries.”
The Sybex CySA+ Study Guide reinforces that DNS queries can be used as covert channels (including encoded/encrypted data inside DNS requests), and that abnormal DNS patterns are IoCs:
Exact extract (Sybex Study Guide):
“DNS tunneling is another potential issue that can be monitored… DNS queries that include encoded or encrypted data are potential IoCs to watch for.”
Why the other options are not supported by the pcap output
A (Meterpreter payload delivery): Meterpreter delivery is not something you’d typically conclude from DNS-only traffic unless you see very specific exploit/payload staging indicators; the capture shown is DNS query/response behavior consistent with tunneling, not a clear Meterpreter staging pattern.
C (SQL injection): SQLi evidence is normally visible in HTTP(S) requests, parameters, URIs, or server responses—nothing in the DNS-only view indicates SQLi payloads.
D (DNSSEC): DNSSEC would be indicated by DNSSEC-specific records/flags (e.g., DNSKEY/DS/RRSIG/NSEC, DO bit usage). The shown traffic is not presented as DNSSEC validation traffic; the suspicious element is encoded/high-entropy data consistent with tunneling.
E (Normal Unix-based traffic): “Normal” is contradicted by the scenario’s stated unusual traffic volume and by the presence of encoded/abnormal DNS content consistent with tunneling IoCs.
References (CompTIA CySA+ CS0-003 documents / study guides used):
Mya Heath et al., CompTIA CySA+ All-in-One Exam Guide (CS0-003): DNS tunneling = sending data via encoded DNS queries; watch for abnormal queries / high volume
Mike Chapple & David Seidl, CompTIA CySA+ Study Guide (CS0-003): DNS tunneling and DNS queries containing encoded/encrypted data are IoCs
Submit