Comprehensive and Detailed Explanation From Exact Extract:
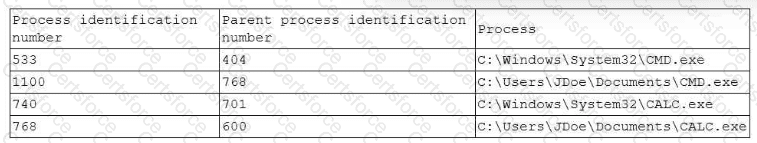
The analyst should review PID 768 first because it is the parent process of another suspicious process (PID 1100) and it is also highly suspicious itself due to its unexpected file path.
Why PID 768 is the best first process to review
Path anomaly (strong IoC): Legitimate Windows binaries like calc.exe and cmd.exe are normally found in trusted OS directories (e.g., C:\Windows\System32\). In the table, both CALC.exe and CMD.exe appear in a user’s Documents folder (C:\Users\JDoe\Documents\...). That is a classic sign of masquerading (a malicious binary using a legitimate-sounding name). The All-in-One guide explicitly describes how attackers disguise malicious processes by using legitimate-sounding names and mimicking system processes.
Parent-child relationship (investigation priority): PID 1100 (Documents\CMD.exe) is suspicious, but it is a child of PID 768 (Documents\CALC.exe). Investigating the parent first helps you understand what spawned the suspicious child, what activity preceded it, and whether PID 768 is the root of the execution chain. The All-in-One guide highlights that analysts should examine process parent-child relationships and investigate unexpected dependencies as a way to detect malicious activity:Exact extract (All-in-One Exam Guide): “Analyze process dependencies Examine process parent-child relationships and investigate any unexpected or unusual dependencies that may indicate malicious activity.” It also emphasizes monitoring grandparent/parent/child relationships to detect deviations from normal process hierarchies:Exact extract (All-in-One Exam Guide): “Monitoring the relationships between processes, particularly grandparent, parent, and child relationships, can be a valuable method for detecting unusual activity.”
Abused/LOLBIN context: cmd.exe is a commonly abused Windows utility in attacks. The Sybex Study Guide notes that attackers often abuse built-in tools and that abnormal OS process behavior involving tools like cmd.exe can indicate compromise:Exact extract (Sybex Study Guide): “For Windows systems, a handful of built-in tools are most commonly associated with attacks like these, including cmd.exe…”
Why the other options are less correct
A (533) and B (740) are running from C:\Windows\System32\... which is the expected location for legitimate Windows binaries in normal circumstances, so they’re less suspicious than the copies running from a user Documents folder.
D (1100) is suspicious, but it is a child of PID 768. Investigating 768 first helps determine the origin and execution chain that led to the suspicious cmd instance.
References (CompTIA CySA+ CS0-003 documents / study guides used):
Mya Heath et al., CompTIA CySA+ All-in-One Exam Guide (CS0-003): parent/child process dependency analysis; process hierarchy monitoring; masquerading techniques
Mike Chapple & David Seidl, CompTIA CySA+ Study Guide (CS0-003): abnormal OS process behavior; cmd.exe commonly associated with attacks
Submit